Who Was Behind LockBitSupp: An Independent OSINT Investigation into the Roles of Dementyev and Khoroshev
🇷🇺 оригинальная версия на русском
Introduction
All individuals mentioned are presumed innocent unless proven otherwise in court.
This analysis is based solely on publicly available and leaked OSINT materials and represents a hypothesis, not a legal determination.
In May 2024, the U.S. Department of Justice named Dmitry Khoroshev a key figure behind LockBit — the most significant public move against the world’s most notorious ransomware group in recent years.
The official indictment matters: it confirms that Khoroshev was indeed connected to LockBit and played a major technical role in its development.
However, the internal structure of groups like LockBit is almost always more complex than a single person behind a single nickname.
This article is not an attempt to dispute law enforcement findings. Rather, it is an independent OSINT contribution — an effort to understand how operational roles may have been distributed inside LockBit, and who may have been behind the public persona of LockBitSupp in day-to-day activity.
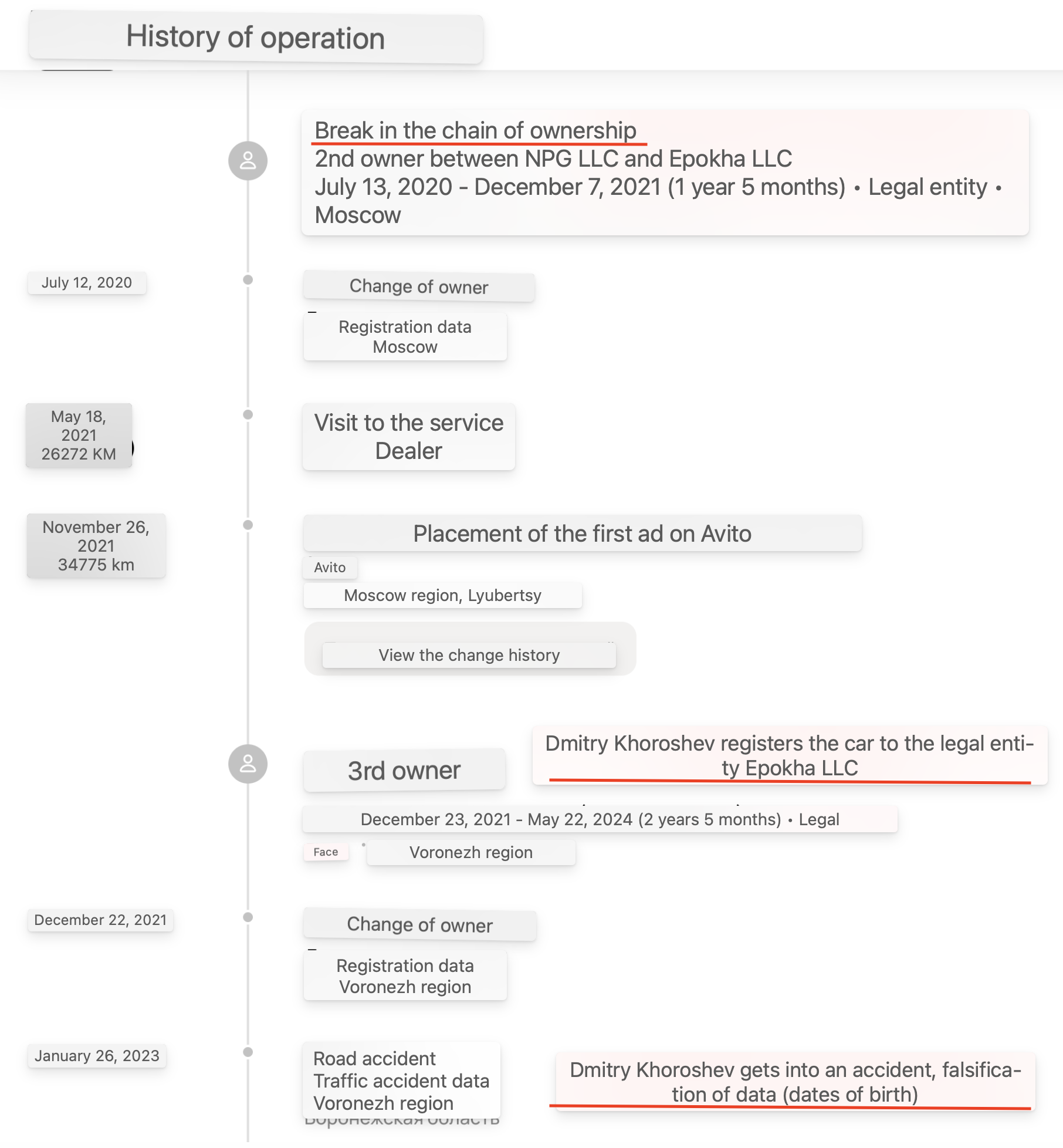
The investigation began with what seemed like a minor detail: a Mercedes vehicle linked to Dmitry Khoroshev.
It ended with something far more unexpected — a three-year timeline in which the traffic-fine activity of a Moscow businessman and the online presence of LockBitSupp appear to alternate with near-perfect consistency.
This is not a single “clue.”
It is a behavioral pattern.
And it deserves careful scrutiny.
What follows is the full chain, step by step.
On May 7, 2024, the U.S. Department of Justice charged Dmitry Yuryevich Khoroshev (Voronezh) with 26 criminal counts (extortion, wire fraud, conspiracy). He is described as a LockBit developer.

- 2012 — under the nickname Pin on forums Opensc and Antichat, he shared code for bypassing memory protection in Windows XP/7 and injecting malware into trusted processes.
- 2011–2016 — under NeroWolfe on Russian forums (Verified, Exploit, etc.), he sold custom malware, botnets, SpyEye/ZeuS panels, loaders, worms, and browser exploits. Specialized in C/C++, anti-detection techniques, and encryption.
- 2013 — offered a $5,000 loader capable of bypassing Windows XP/7 protection.
- 2013 — discussed the ethics and future growth of ransomware on Exploit.
- Email sitedev5@yandex.ru (mailto:sitedev5@yandex.ru) (listed in U.S. sanctions) was used to register tkaner.com(Khoroshev’s legitimate Voronezh business).
- The same email and phone number (+7-952-102-02-20) appear in older domains (e.g., stairwell.ru) and NeroWolfe accounts.
- Password 225948 from stairwell.ru was reused across multiple NeroWolfe accounts (2011–2015).
- ICQ 669316 (Pin/NeroWolfe) → d.horoshev@gmail.com (mailto:d.horoshev@gmail.com) → Voronezh.
2. Khoroshev’s Mercedes: the critical slip that exposed the trail
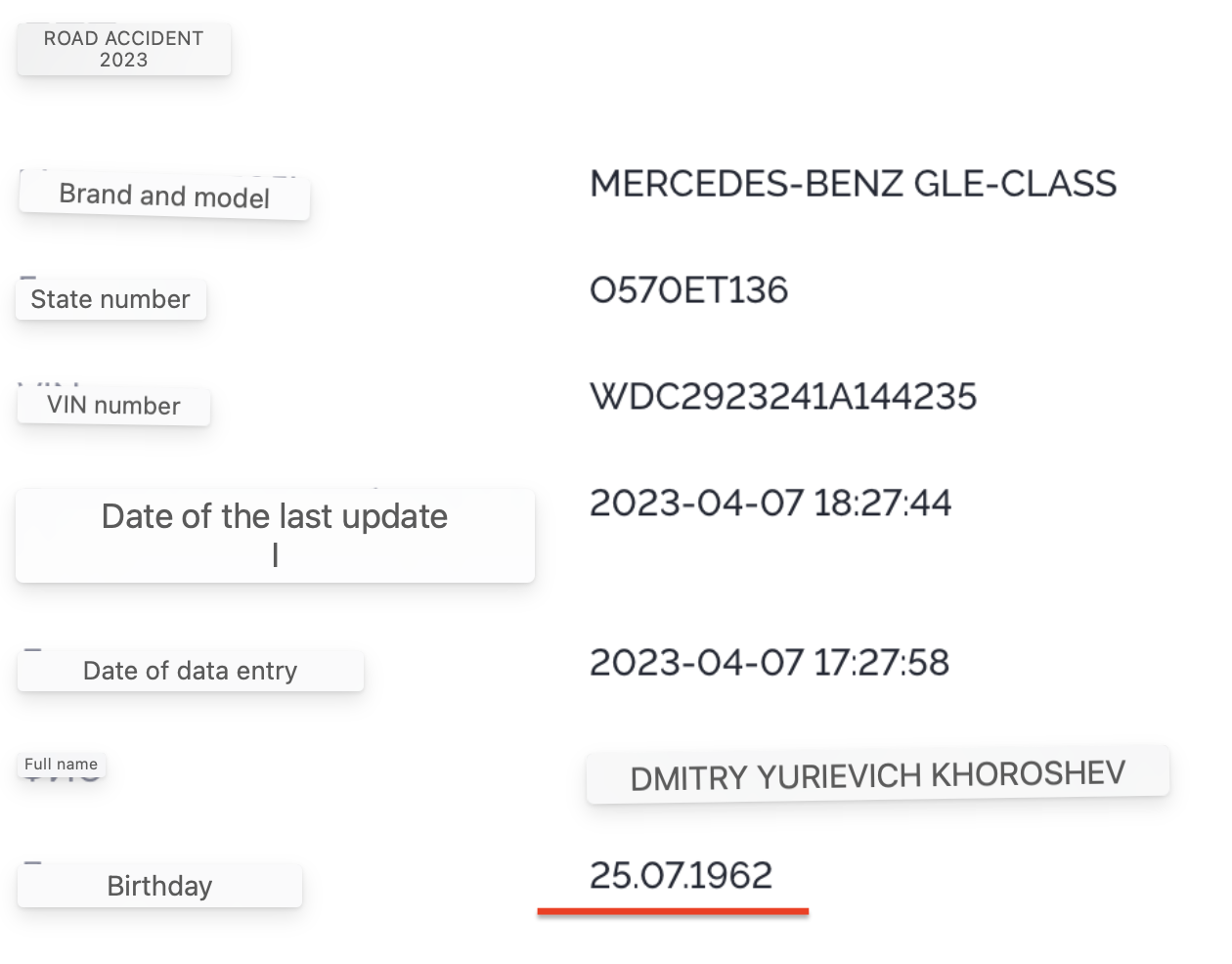
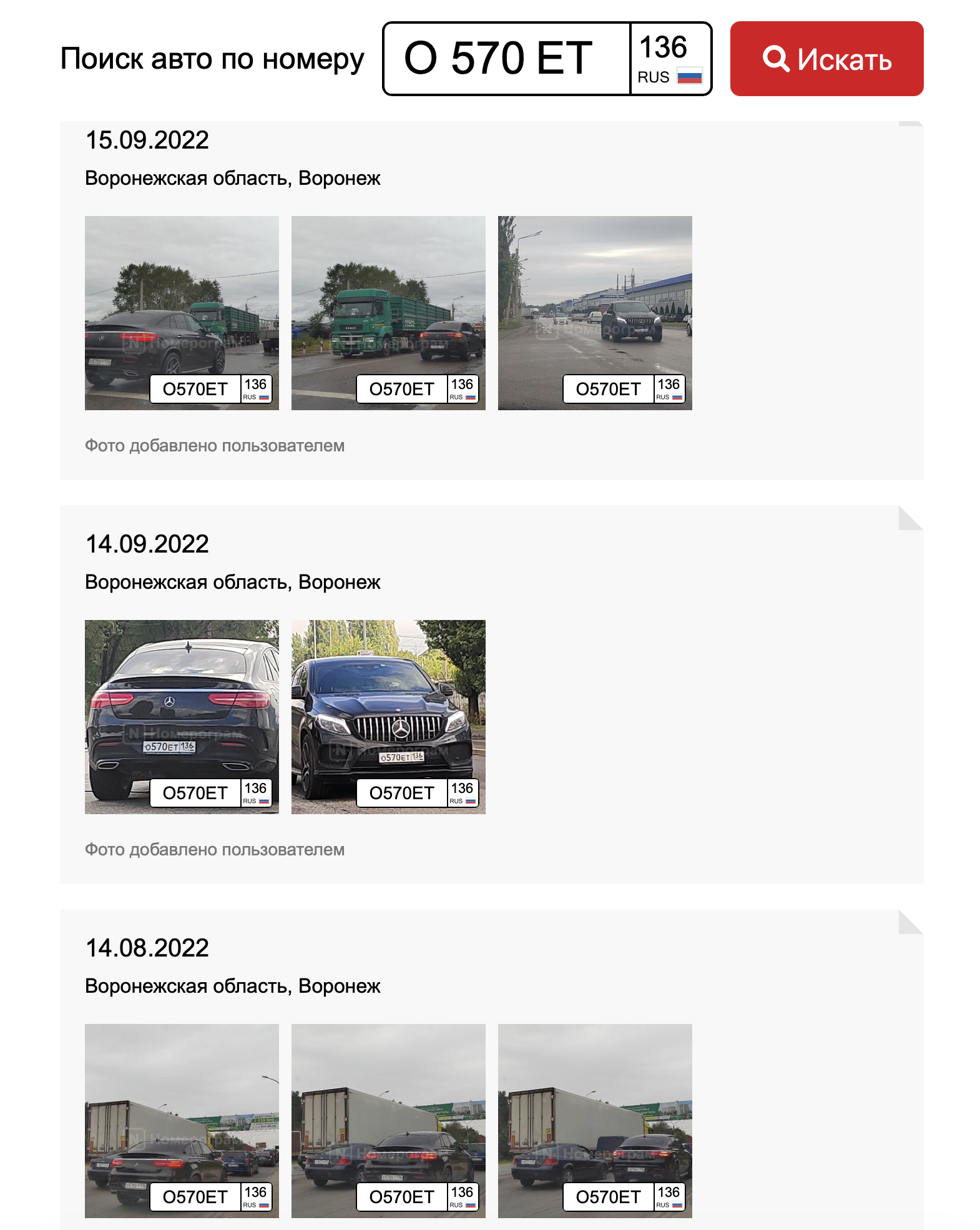
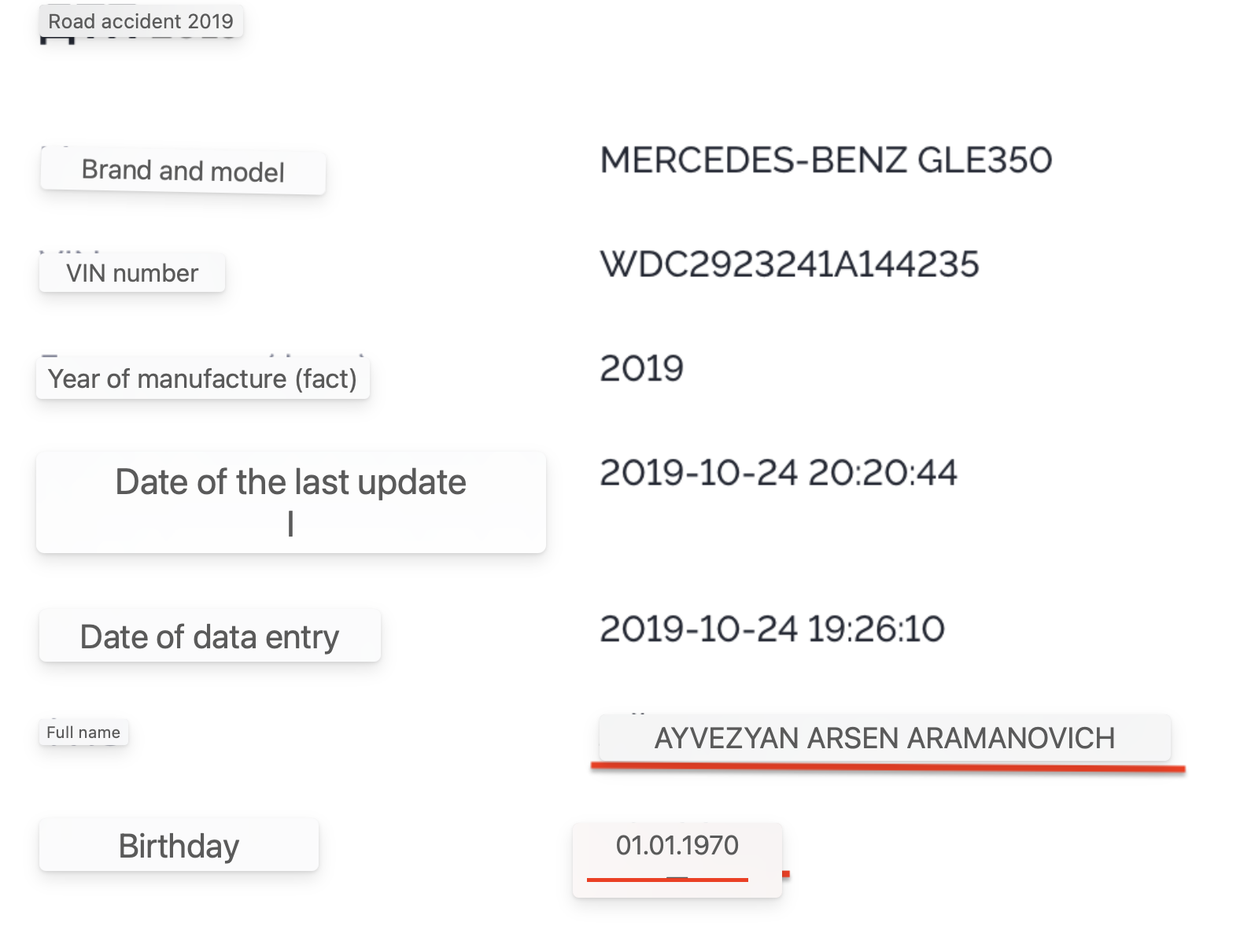
Dmitry Khoroshev owned (but concealed ownership of) a Mercedes-Benz GLE 350d 4MATIC, VIN WDC2923241A144235, Russian license plate О570ЕТ136.The same email sitedev5@yandex[.]ru was used for domain registrations, including his legitimate company LLC TKANER (ООО "ТКАНЕР" INN 3662295721).
The disappearance was not only anecdotal — the service produced different results for the same plate across time.
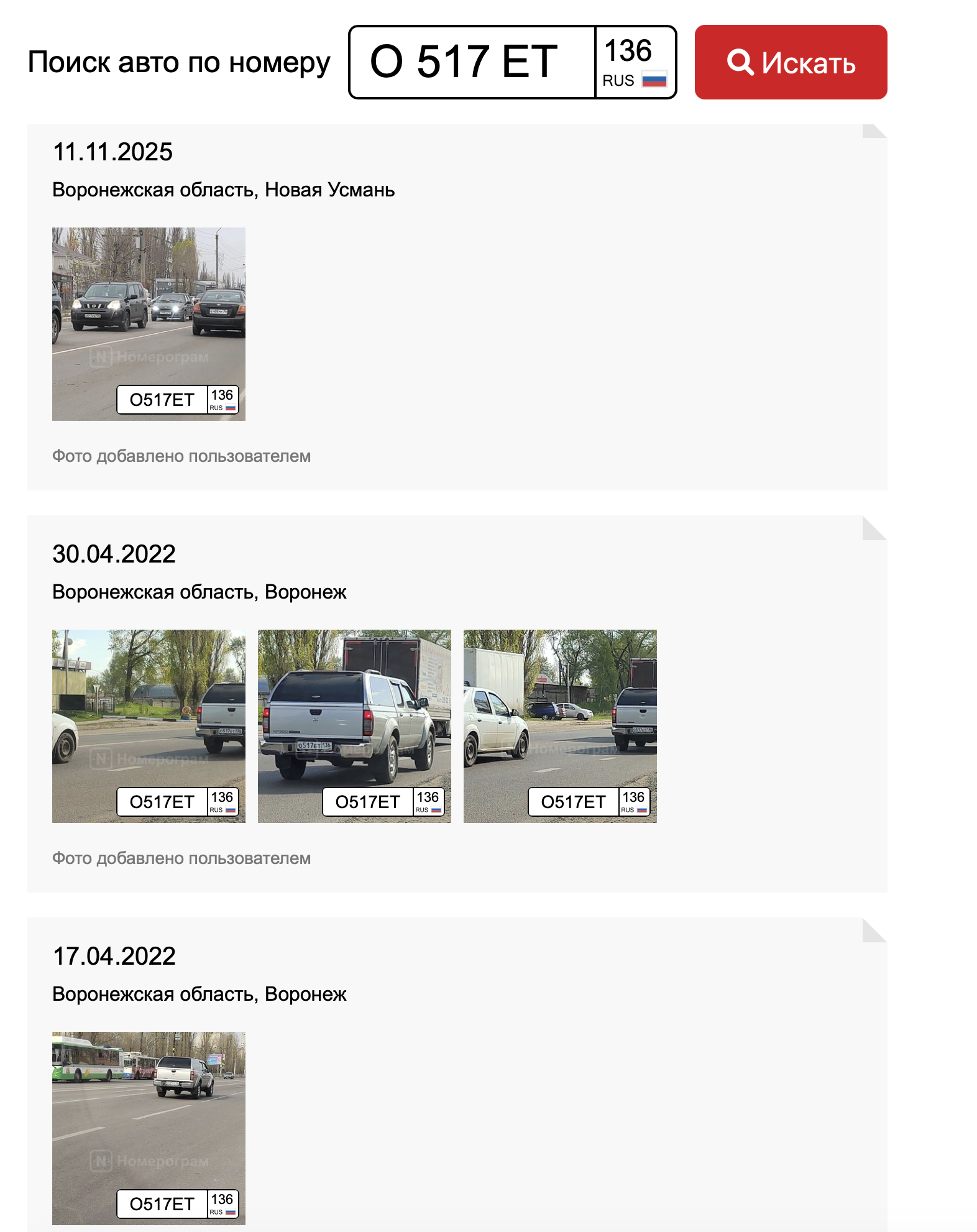
⚠️ Archived query: (Mercedes absent) https://www.nomerogram.ru/n/o517et136-1253a4145/
⚠️ Updated query: (Mercedes restored) https://www.nomerogram.ru/n/o570et136-1369f5b53/
Screenshots were preserved for verification.
CEO and owner: Evgeny Petrovich Dementyev, born July 21, 1987.

- Moscow and Khimki
- Kaluga region
- Kievskoe Highway
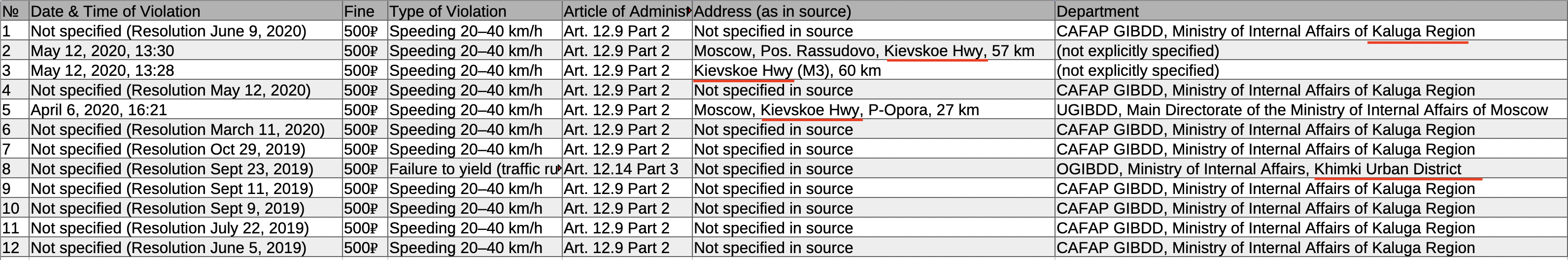
Parking spot 453, Khimki, ul. Moskovskaya 21 — confirmed as Dementyev’s property via EGRN (кадастр 50:10:0010211:828) extract.

- Home base near Kievskoe Highway
- Regular trips along Kievskoe Highway
- Infrequent but systematic long-distance travel to/from Kaluga region (1–3 times per month)
- Primarily highway usage, almost no Moscow city camera hits
This is one of the strongest and most visually clear arguments in the entire investigation.
I collected all available traffic fines associated with the vehicle used by Dementyev, as well as all public LockBitSupp messages, and compared them chronologically.
Data Sources
-
Data on traffic fines and recorded vehicle detections (license plate K102CX799) was obtained from commercially available extended reports (Autocode, AvInfo, etc.), which aggregate information from public and official sources (example: avtocod.ru).
-
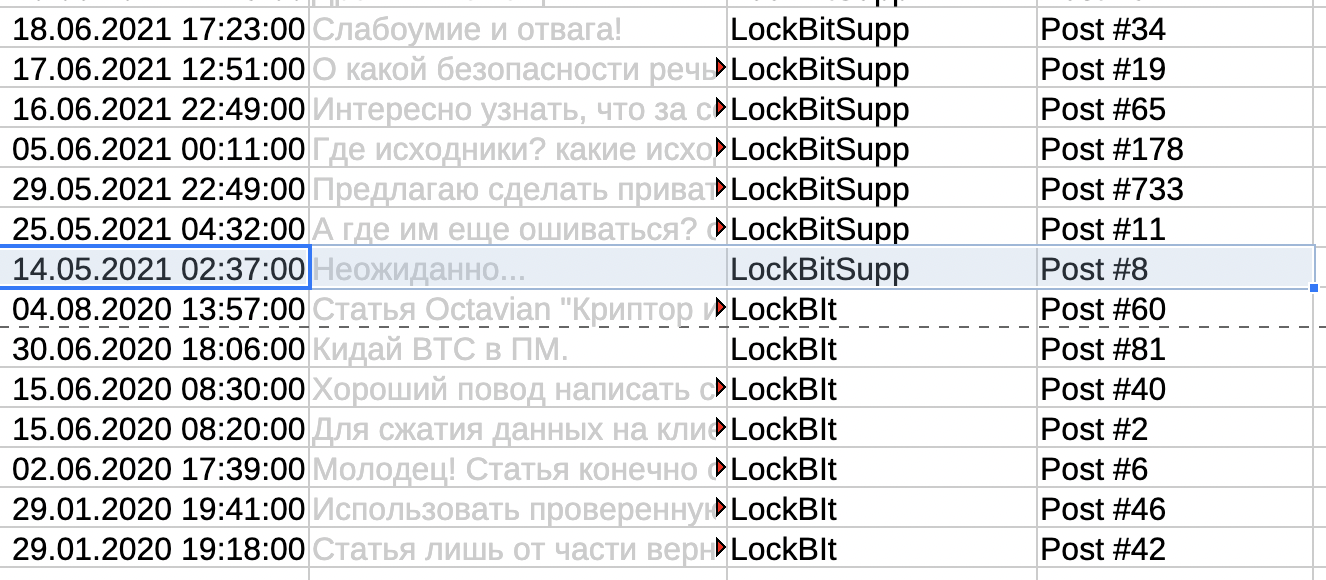
Public LockBitSupp posts from the XSS forum (xss[.]pro) — accounts LockBitSupp and LockBit.
-
Public LockBitSupp posts from the ReHub forum (onion) — account LockBit.
-
LockBitSupp messages from the Tox messenger (published in an interview with Tor Zirael — file petuh.txt).
-
Public messages from the Telegram account Fox William Mulder (ID 7262708360), which was widely considered to be the official LockBitSupp channel (now deleted).
- Analysis of 162 fines
- add: there is also a free and fully legal source for obtaining traffic fines — the mobile application “ШТРАФЫ ГИБДД” (in Russian, available in the Play Store or App Store with the region set to Russia or Kazakhstan — but it works from any IP address). Search icense plate K102CX799 CTC 9946414542. A virtual Android environment can be used as well: https://cloud.geny.io/l
All original materials, tables, and raw datasets (in redacted form, without publishing personal data) were previously referenced in my earlier article.
In order to reduce potential legal risks, I do not publish the full dataset openly. However, I am prepared to provide it to journalists and researchers for independent verification upon request.
Overall Timeline
The overall graphical timeline makes it possible to clearly see the density of events and the periods where activity is absent.
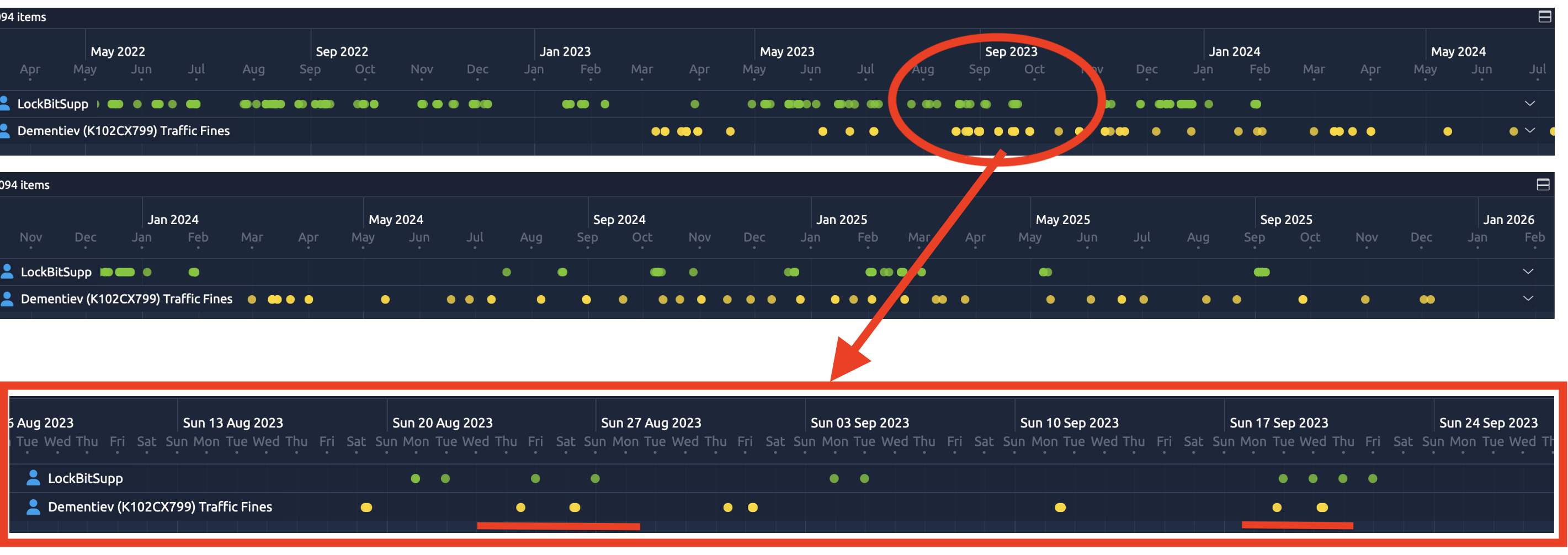
I consolidated all this data into a single timeline table 👉 Download, with traffic fines highlighted in yellow for clarity.
Key Observation
The main fact is the following:
LockBitSupp publications and recorded vehicle travel events (through fines and traffic cameras) almost never coincide in time over a three-year period (2023–2025).
It is important to clarify:
-
Traffic fines do not identify the driver directly, but rather reflect vehicle activity associated with travel.
-
Posts reflect the operator’s online activity (forums, Tor, Tox).
The picture looks like this:
-
When travel is recorded (fine “clusters”) → LockBitSupp demonstrates prolonged silence.
-
When series of posts appear → the vehicle does not appear on road cameras during that period.
This is not a single episode, but a repeated alternation structure.
Why This Deserves Attention
Both signals are relatively rare:
-
Fines: only 66 unique days over 3 years (~48 trips).
-
LockBitSupp posts: about 87 active days over the same period.
Out of ~1095 days, only 5 days contain both events, and even in those cases they are separated in time (typically by 6–12 hours).
The only “close” example is 03.02.2025:
Fine at 15:33–15:34 → Tox message at 16:24.
Even here, the time gap increases after accounting for the Moscow time zone (UTC+3), and more likely reflects a mode switch: “travel → return → online activity.”
Examples of Clear Alternation Clusters
On December 6, 2025, a fine was recorded for Dementyev (LockBitSupp had not posted for three months before that — since September 18, 2025). Then starting the next day, December 7, LockBitSupp posted messages for several days in a row (December 7–8–9). But on the following day, December 10, a Dementyev trip was recorded again, and LockBitSupp fell silent for several days until December 16, 2025.
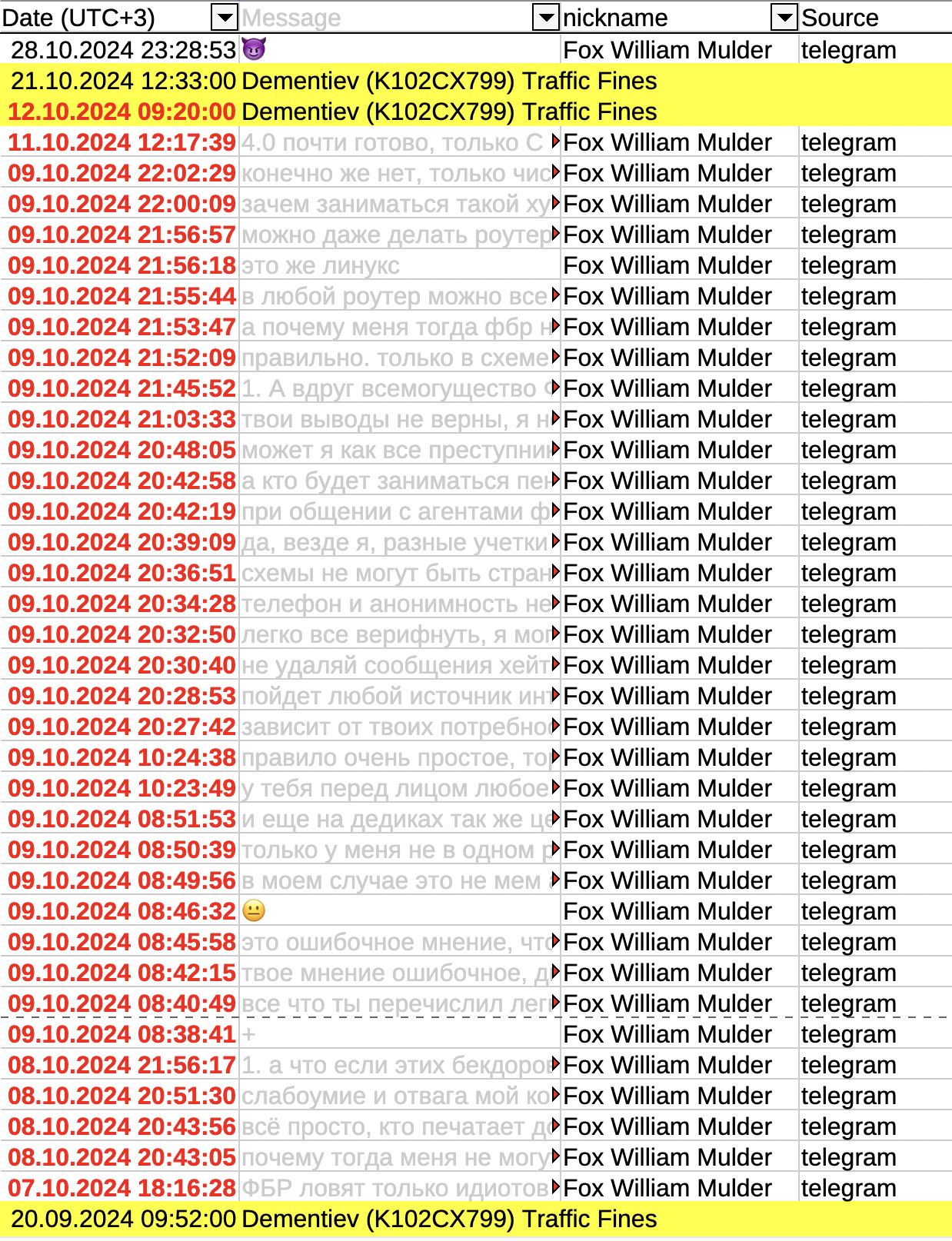
A similar example appears in the Telegram group: LockBitSupp had been silent for two months since August 18, 2024. Then on October 7, 2024, LockBitSupp became active and sent messages to the chat on October 7–8–9 and 11. But on the next day, October 12, the messages stopped and we see a fine (a trip) recorded for Dementyev, and there were no further LockBitSupp messages for several days until October 28, 2024.
Another example: August 19, 2023 — a fine; August 21–22 — messages; August 24 — a fine; August 25 — a message; August 26 — a fine; then August 27 — a message. Practically day by day, fines and messages alternate. When on the road — no posts. When at the computer — no fines are recorded.
On the same screenshot below: September 18, 2023 — a fine; September 19 — a message; September 20, 2023 — fines from 6 to 8 a.m., and by midnight only messages appear (September 20, 2023 at 23:12:00).
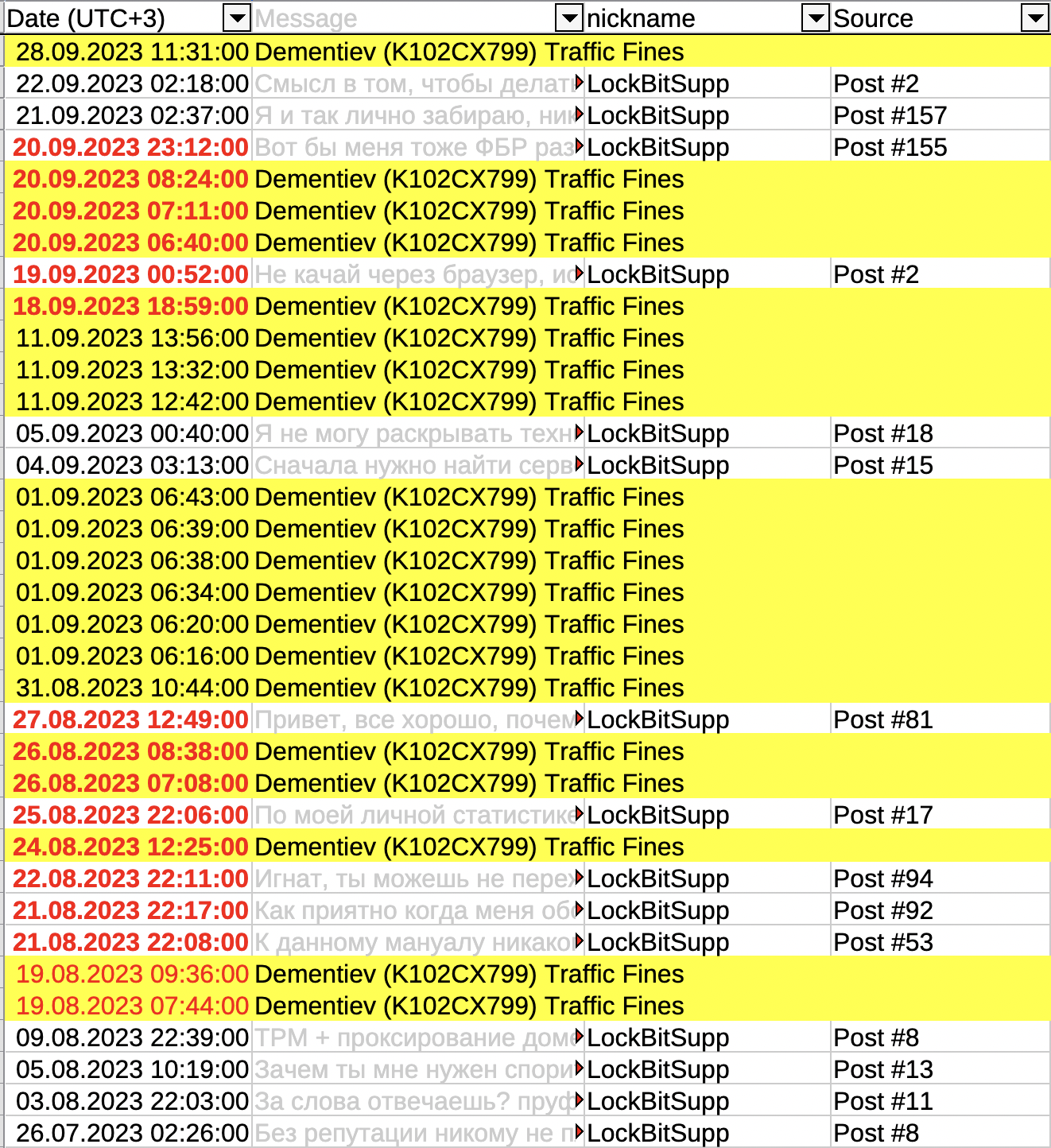
Such vivid sequential alternations are marked in 13 fragments (highlighted in the table), and simpler supporting patterns number several dozen.
This forms a repeating behavioral signature.
Forensic Metric: Alternation, Not Just Absence of Overlap
What matters here is not the minimal distance between “fine ↔ post,” but the sequential blocks:
silence → travel → messages → travel → silence → messages …
If these were completely independent signals, random overlaps should occur more often.
Instead, there is near-complete mutual exclusion over a long interval.
Control Comparison
When applying the same method to other random vehicles, such “ideal” alternation does not appear: events overlap far more chaotically.
This makes the observed pattern statistically unusual.
Conclusion of This Section
The fines and vehicle detections associated with Dementyev do not simply “fail to overlap” with LockBitSupp posts — they form a stable alternation pattern that may be compatible with the hypothesis of a single operator.
This behavioral pattern warrants further examination and independent verification.
Imagine this: you are a person with a $10 million bounty on your head.
You are hiding better than anyone in the world of cybercrime.
You have no face on social media, no old photos, no leaks. No traces.
You are the god of ransomware — LockBitSupp.
And then a message arrives on Telegram:
“Hello, Evgeny Petrovich. This is part of your dossier. When would it be convenient to discuss?”
And you realize: that’s it. The end.
This message... it came from me, an anonymous investigator who spent half a year tearing apart the Conti group, published photos of 80+ members, and then reached LockBit.
Here is the rest of the story.
On August 1, 2025, I sent LBS on Tox a photo of Evgeny Dementyev with the words:
“By any chance, is your name Evgeny?)”
(this was said with uncertainty; LockBitSupp did not reply and blocked my contact).
On January 5, 2026, I wrote directly to Evgeny Dementyev on Telegram from an anonymous account not connected to GangExposed. I sent part of his dossier (I will attach the full version to this article) with the words:
“Hello, Evgeny Petrovich. This is part of your dossier, I can send the full version. I also have critically important information for you that I would like to share. When would it be convenient for you to discuss?”
Dementyev read it but did not respond. He blocked me, removed his profile picture (no face) from his account, and completely close incoming messages (except for Telegram Premium).
Such a reaction is a sign of concern.
It was necessary to push him toward actions, toward mistakes.
On January 10, 2026, I wrote in a public chat: “In the next few days I’ll drop an interesting topic about LockBit.” It worked!
The next day, January 11, 2026, an official Telegram account was registered: LockBitSupp Innokentii Petelkin @PetelkinKesha (ID: 8293550563) with the LockBit logo as the avatar.
I verified @PetelkinKesha as an authentic LBS account through his Tox. Independently of me, Tor admin Zireael and another source confirmed this via the LockBit panel Tox and the ReHub forum.
Then he “found” my Telegram channel https://t.me/GangExposed_int and joined my group.
He joined my Telegram group and publicly announced a $22 million “bug bounty” for information leading to the identification of the alleged leaker — on the condition that the information be delivered exclusively to him and not shared with U.S. Rewards for Justice or disclosed publicly.
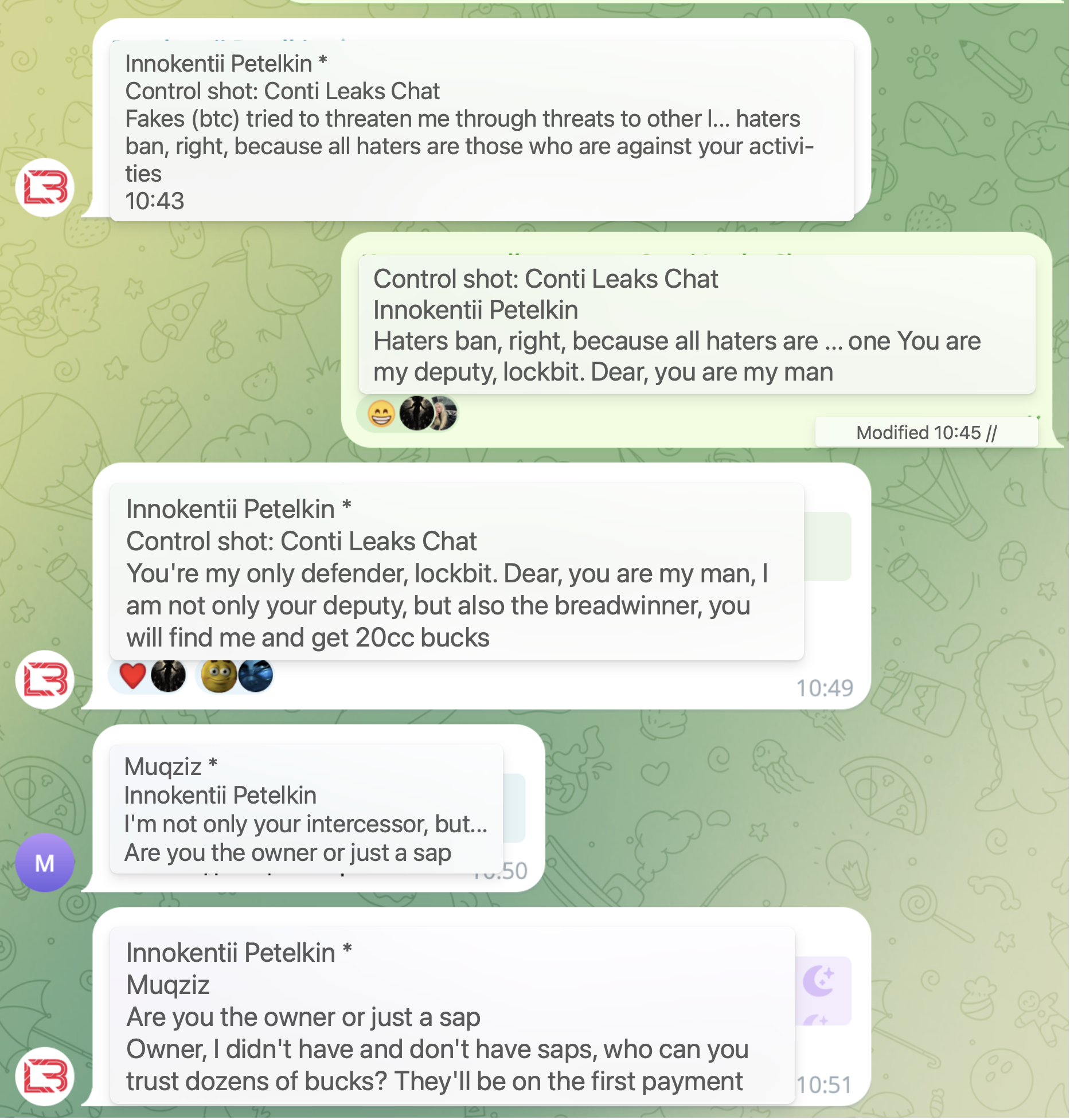

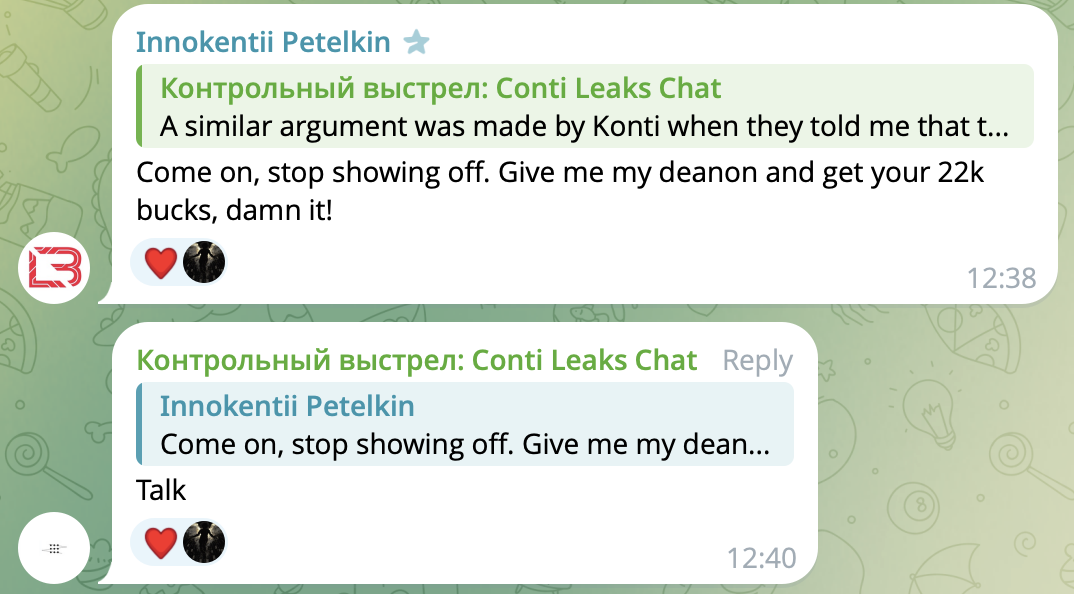
Looks like I just wiped out the most expensive bug bounty in ransomware history.
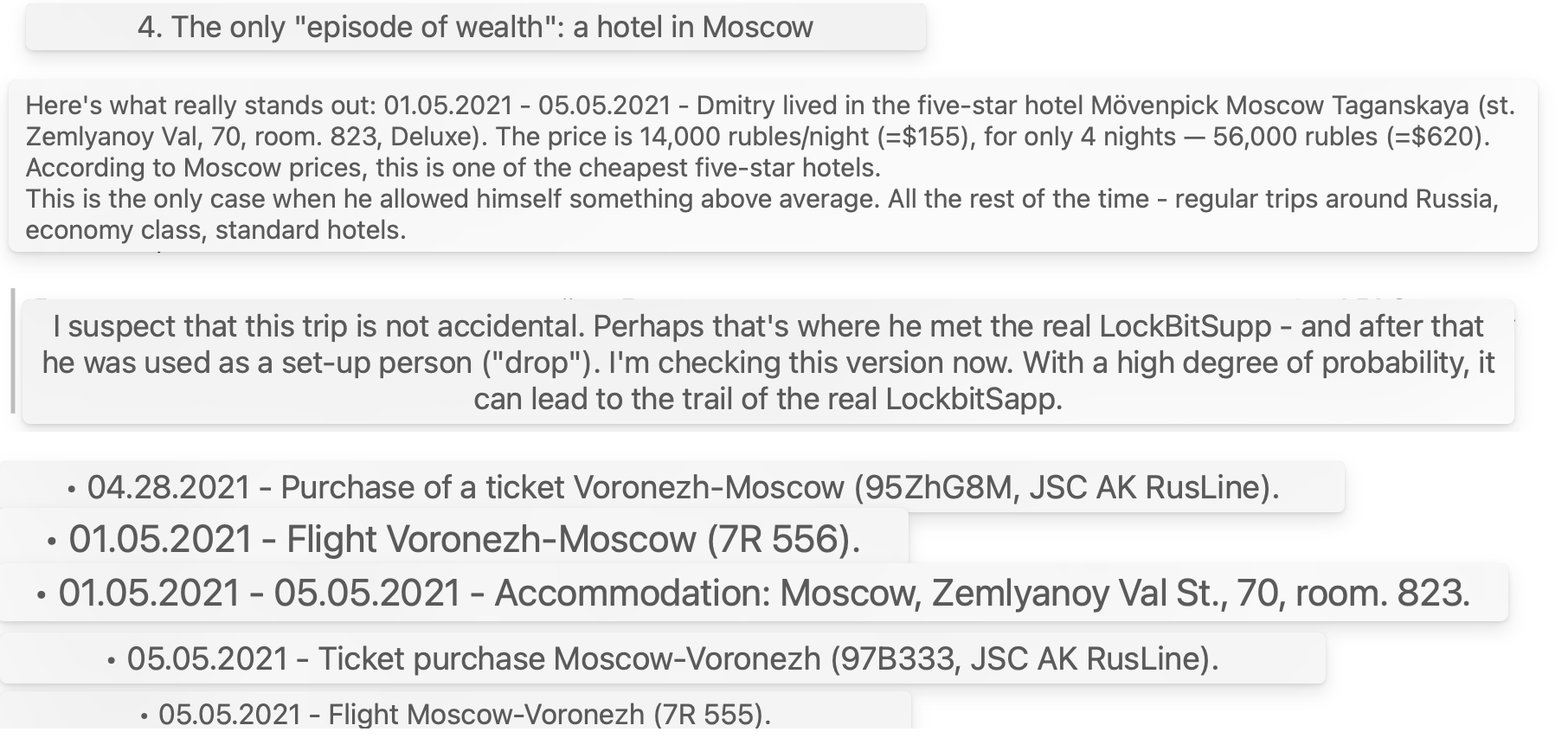
Notable: Khoroshev traveled to Moscow May 1–5, 2021.
- Khoroshev — long-time malware developer (Pin → NeroWolfe → …)
- Concealed Mercedes not registered to him
- 2023 crash — owner data falsified
- Photos scrubbed from Nomerogram (later restored)
- Sold immediately after May 2024 U.S. charges
- Vehicle originated from Dementyev’s Moscow LLC “NPG”
- Earlier Mercedes fines match Dementyev’s geography
- Transfer hidden via fake intermediaries
- BMW X6 parked at Dementyev’s owned spot in Khimki
- BMW fines — rare long trips to Kaluga region, likely country residence
- Three-year perfect alternation between fines and LockBitSupp posts
- Zero time overlap; 20+ alternation clusters; statistically near-impossible coincidence
- January 2026: dossier sent to Dementyev → subsequent public response → new account + $22M bounty
Evgeny Dementyev may represent one of the strongest observable candidates for the LockBitSupp operator role, based on the behavioral correlation presented.
15. Next steps: roadmap for law enforcement and researchers
- Check other vehicles owned/used by Dementyev (including possible Mercedes sedan seen in Telegram avatar)
- Verify parking spots 451–453 (Khimki, Moskovskaya 21) and Timiryazevskaya 1 via residents’ chats
- Locate current primary residence (likely cottage on Kievskoe Highway)
- Cross-reference Khoroshev’s May 2021 Moscow trip with LockBitSupp debut (possible handover)
- Reconstruct full trip patterns (days absent, birthdays, etc.) for predictive analysis
- Identify other LockBit members and Dementyev’s trusted circle
- Trace shell companies, contacts, financial flows
- Forum accounts (putinkrab etc.), stylometry vs. older nicknames
- Photos from documents, biography, China trip (Shanghai), billing, cameras, assets, fake IDs
- Past carding activity, cover stories, enemies, competitors
16. Thanks to everyone fighting LockBit — now it’s your turn
Gratitude to the researchers, journalists, and agencies who have systematically eroded LockBit for years:- Jon DiMaggio (Analyst1) - Ransomware Diaries
- Allan Liska (Recorded Future)
- Arda Büyükkaya (Trend Micro)
- Michael Gillespie (Emsisoft / No More Ransom)
- Alon Gal (Hudson Rock)
- Valery Rieß-Marchive (LeMagIT)
- Brian Krebs (krebsonsecurity.com)
- Baptiste Robert (special thanks for the photo of Khoroshev’s Mercedes)
- XOXO (from Prague)
- BleepingComputer (Lawrence Abrams, Bill Toulas, team)
- WIRED, Computer Weekly, The Register (Jessica Lyons), Bloomberg (Jake Bleiberg), etc.
- Chainalysis, Recorded Future, Trend Micro, Secureworks, Prodaft, Flashpoint, Arctic Wolf, MalwareHunterTeam, Sophos, Emsisoft, Hudson Rock, Group-IB, BI.ZONE, Kaspersky
- Law enforcement: NCA, FBI, Europol, Eurojust, BKA, Australian Federal Police, etc. — and Operation Cronos teams
While the trail is still warm — help verify, amplify, and finish LockBit together.
I need your support, help, and resources to work on exposing the next ransomware group — Qilin, DragonForce
