Hunting Conti’s Shadow
How I found what the FBI, NSA and an army of researchers couldn’t
Imagine hunting the most disciplined cyber-criminal group in the world — Conti.
These guys wrote textbooks on OPSEC. Impeccable digital hygiene.
In 2022, all their internal work chats (hundreds of thousands of messages) leaked online.
Conti simply laughed, then went on to encrypt an entire country — Costa Rica, changed their label, and continued working.
Intelligence agencies, analysts and independent researchers spent years looking for even a single lead.
Nothing.
The FBI, admitting defeat, announced a $10 million reward for the names of the leaders.
Three years of gold rush, thousands of analysts, endless reports — and zero results.
But I decided to challenge that.
This is the story of how I, step by step, uncovered and mapped connections, flights, and identities of key figures in the group, using the leaked FSB border-control database “Granitsa,” fragments of data from Conti chats, and pure OSINT.
These anonymous figures had no faces — only shadows.
I turned on the spotlight, and their own shadows caught up with them.
Thus, the hackers gained names.
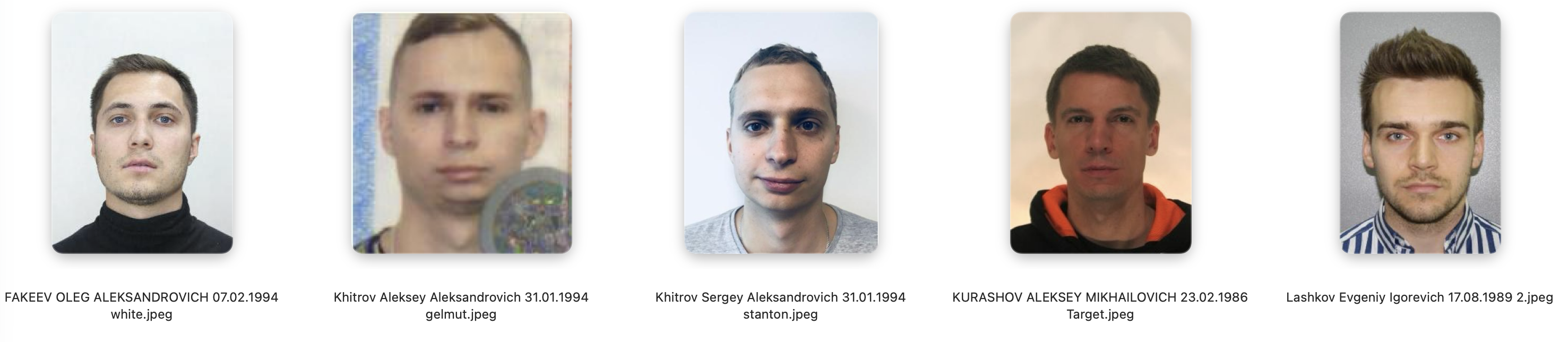
The First Lead. Kurashov and His Fellow Travelers
Those flying to Dubai weren’t tourists
It all started with Alexey Kurashov.
His name surfaced after analyzing thousands of leads pointing to Moscow-City.
There was no hard evidence — only communication-style analysis in Conti chats suggested he was Target, a key figure in the group. Only stylometry and intuition. I decided to go direct — I texted him on Telegram.
After a short conversation I understood: yes, it’s him. The first key member identified.
But I needed undeniable proof.

I gathered all border-crossing data for Kurashov over the last 10 years.
Dozens of flights, hundreds of co-travellers.
Gradually, a network of his closest contacts began to emerge — people he flew with over and over.
The UAE trips since 2021 stood out sharply.
These weren’t random vacations: the same faces, round-trip flights on a tight schedule.
As if the hackers worked by a timetable.
But why?
I decided to dig deeper.
The Timeline: A Map of Their Secrets
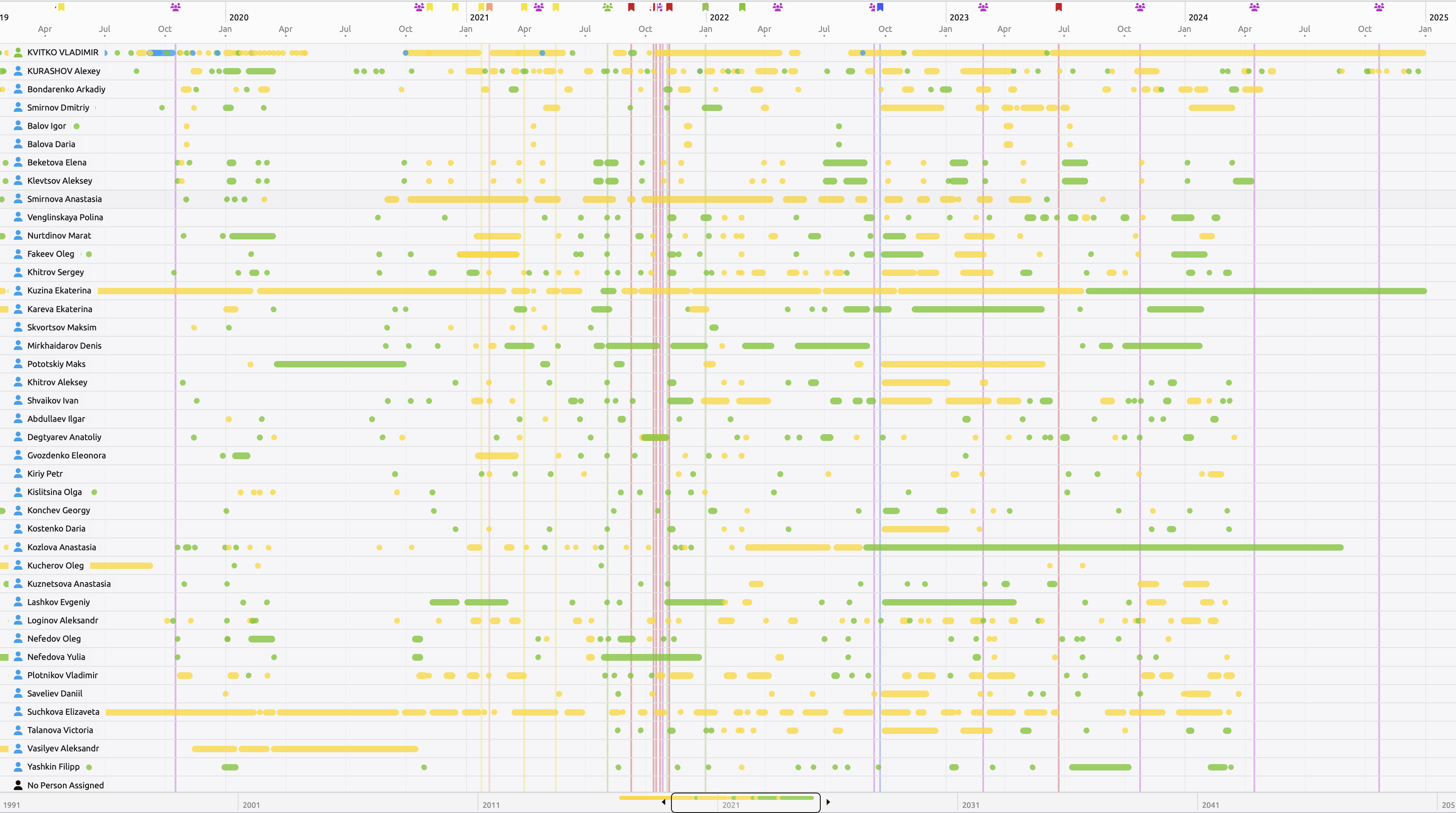
To understand how this network operated, I created a visual timeline of Kurashov’s flights and those of his co-travellers.
Each flight — a fragment of mosaic revealing their movements.
In parallel I immersed myself in reading Conti chats — and began comparing.
Everyone there followed strict compartmentalization and masked themselves even from one another.
But systematic work paid off.
In the Rocket.Chat dump, I found a message from user RED — an account Target used for only a couple of hours:
2021-10-12 15:35:49 red: “мы рано по утру высылаем ребят”
("we’re sending the guys early in the morning")
Seems ordinary, right?
At first glance.
But flight data told more:
On October 13, 2021, on flight SU-520 to Dubai, Marat Nurtdinov and Oleg Fakeev — Kurashov’s close friends — flew out.
Coincidence? Unlikely.
This was the first lead connecting the digital world to the real one.
The Phrase That Led Me to Conti's Dubai Office
Another clue surfaced in Jabber.
A user named Bloodrush (who is Target, as I established via stylometry and fact-checking) wrote:
13.10.2021: “Я до пятницы не имею доступ к кошельку для онлайна, у меня чистая крипта только.”
("I don’t have access to the online wallet until Friday, I only have clean crypto.")
And on October 14 — guess what?
Kurashov flies to Dubai.
On the same SU-520 flight with him — someone named Vladimir Kvitko.
Bloodrush disappears from the network and reappears on October 15.
Friday.
Everything aligned perfectly.


💥 Next I’ll tell you who Vladimir Kvitko is, and how one tiny OPSEC mistake erased a decade of his perfect operational discipline.
Continuation
How I Unraveled the Web of Conti’s “Professor” and His Dubai Allies
The shadows highlighted in Kurashov’s (Target’s) timeline led straight to Dubai — the unofficial capital of their operations.
There, in the shadow of Burj Khalifa, hackers exchanged crypto and plans while posing as businessmen at conferences.
But one careless phrase in chat and one flight — and an analyst gets a golden clue.
Next in the crosshairs: Vladimir Kvitko, Kurashov’s fellow traveler on three UAE flights.
This man was a ghost among ghosts.
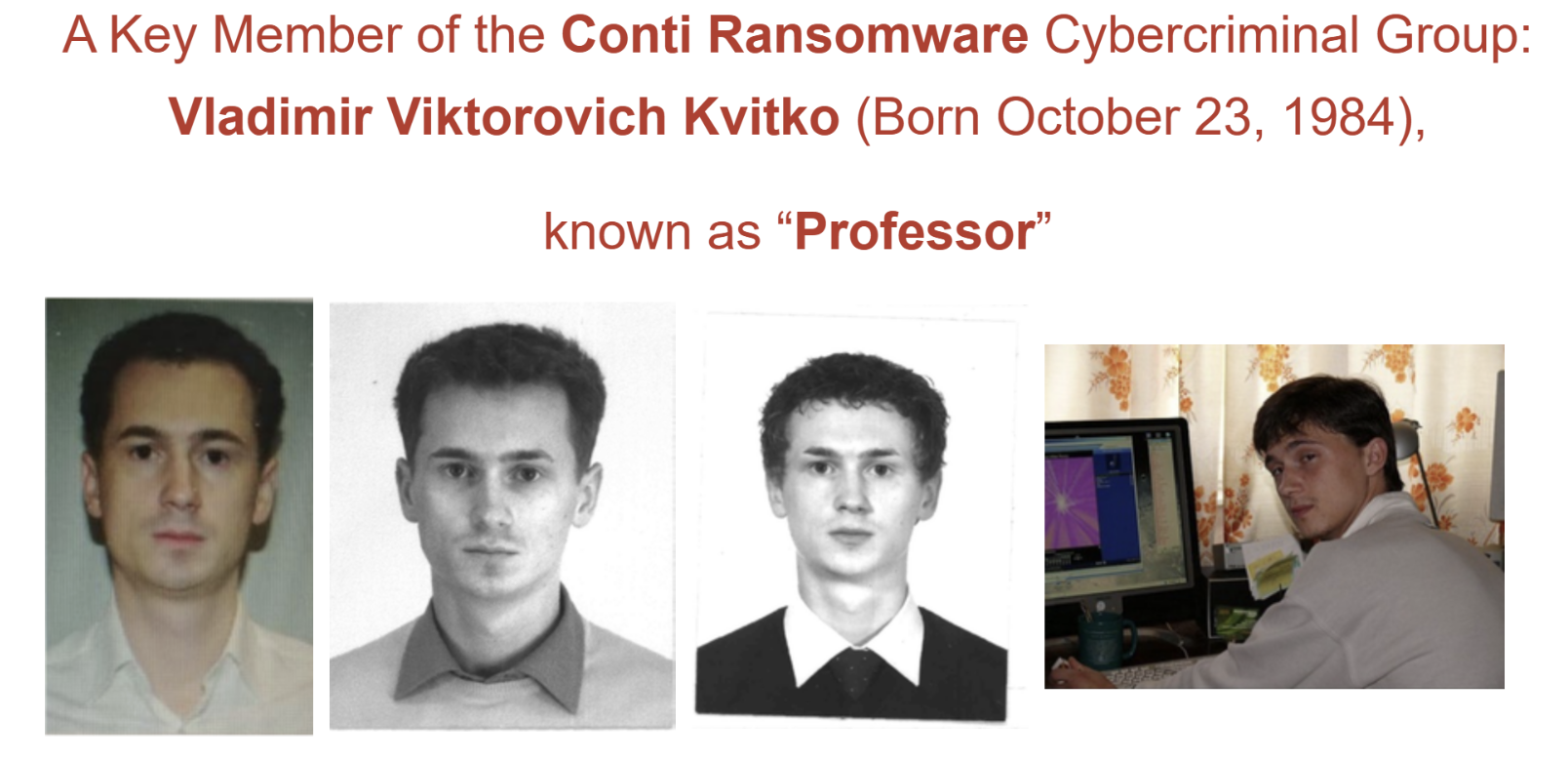
The Professor — A Genius Who Tripped Over the Phrase “On the Road”
Vladimir Kvitko was a digital perfectionist.
His LinkedIn looked like a polished museum exhibit:
An MBA from IE Business School, a PhD, patents, work at major companies, numerous achievements.
Not a single scratch on his digital profile.
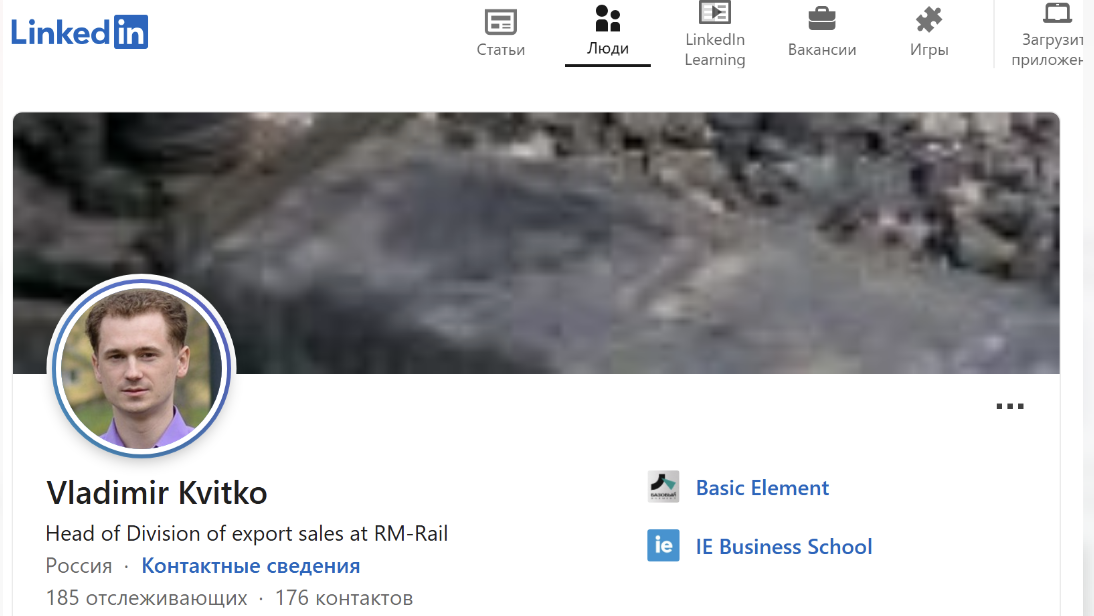
A random businessman? Possibly.
But one detail bothered me — his birth year: 1984.
Here’s the hint — Target once joked about the Professor in Conti chats:
2020-08-20 09:43:15 target → dandis:
“ну проф просто вредный тип и старый )))))))))”
(“well the Prof is just a grumpy type and old”)2020-08-20 09:43:38 dandis: “Почему старый? :D”
2020-08-20 09:44:33 target: “потому что на пару лет старше как выяснилось )”
(“because he turned out to be a couple years older.”)
Kurashov was born in 1986.
Kvitko in 1984.
A two-year difference.
“Prof” = “Professor” — the Conti general, strategist, the brain of operations.
The FBI also offered $10M for identifying him.
This man was a master of secrecy, a genius who made no mistakes.
No wonder the FBI analysts gave up — everything was too clean.
I sifted through RosPassport records, the “Magistral” flight database.
Kvitko was careful: his flights usually occurred on weekends, when chats went quiet.
I studied thousands of messages from “Professor” (a.k.a. “Alter”, “TeamLead2”) — a maze of obfuscation.
And suddenly — an unexpected discovery.
One line like a bullet piercing his armor of secrecy.
Not just text.
A golden clue:
2021-06-14 16:57:26 professor → paranoik:
“декриптни файл пожалуйста людям”
(“decrypt the file for the people please”)
Silence.
Absolute silence from Professor until June 18.
Then:
2021-06-18 10:40:33 professor → pin:
“ку
через пару часов буду
в дороге”
(“hey, I’ll be on the road in a couple hours”)
I checked: on exactly those dates, Kvitko was in Altai.
Moscow–Novosibirsk and back — the “Magistral” database confirmed it:
1553-SU 18.06.21 TOLMACHEVO (Novosibirsk) → SHEREMETYEVO (Moscow)
Perfect anonymity collapsed because of one phrase.
The Professor was identified.
Another “10-million-dollar” ghost caught.
But Kvitko wasn’t alone — he too had interesting associates I investigated.
Yet the most intriguing was another mysterious figure, appearing on the same timeline but carefully avoiding joint flights with him.
Professor crossed paths in Dubai seven times with Arkady Bondarenko — always 1–2 days apart to avoid showing up as co-travellers.
Let’s take a closer look at the next target.
Next: Arkady Bondarenko — The Canadian Negotiator with a Russian Accent
