The Canadian Negotiator with a Russian Accent: Conti’s Shadow Diplomat
In any ransomware operation there is a figure people rarely write about, yet it is precisely this figure who determines the final ransom amounts — the negotiator. This is the elite of the group: a master of pressure, manipulation and psychological warfare. He assesses the victim’s financial capacity, pressure points and the optimal moment when the organization will break. One successfully conducted dialogue can bring the criminals millions.
The hackers’ work is only a preparatory stage.
An access broker sells the entry, pentesters expand presence, exfiltrate data and deploy the encryptor. And when a company is already in panic, when infrastructure is paralyzed and gigabytes of stolen documents hang under the threat of publication, — the negotiator steps onto the stage.
He is the one who determines the final outcome of the attack.
Now imagine: one of Conti’s negotiators works at a legitimate recovery company where victims turn for help.
The victim trusts him with restoration and protection.
And he — works for the criminals.
-
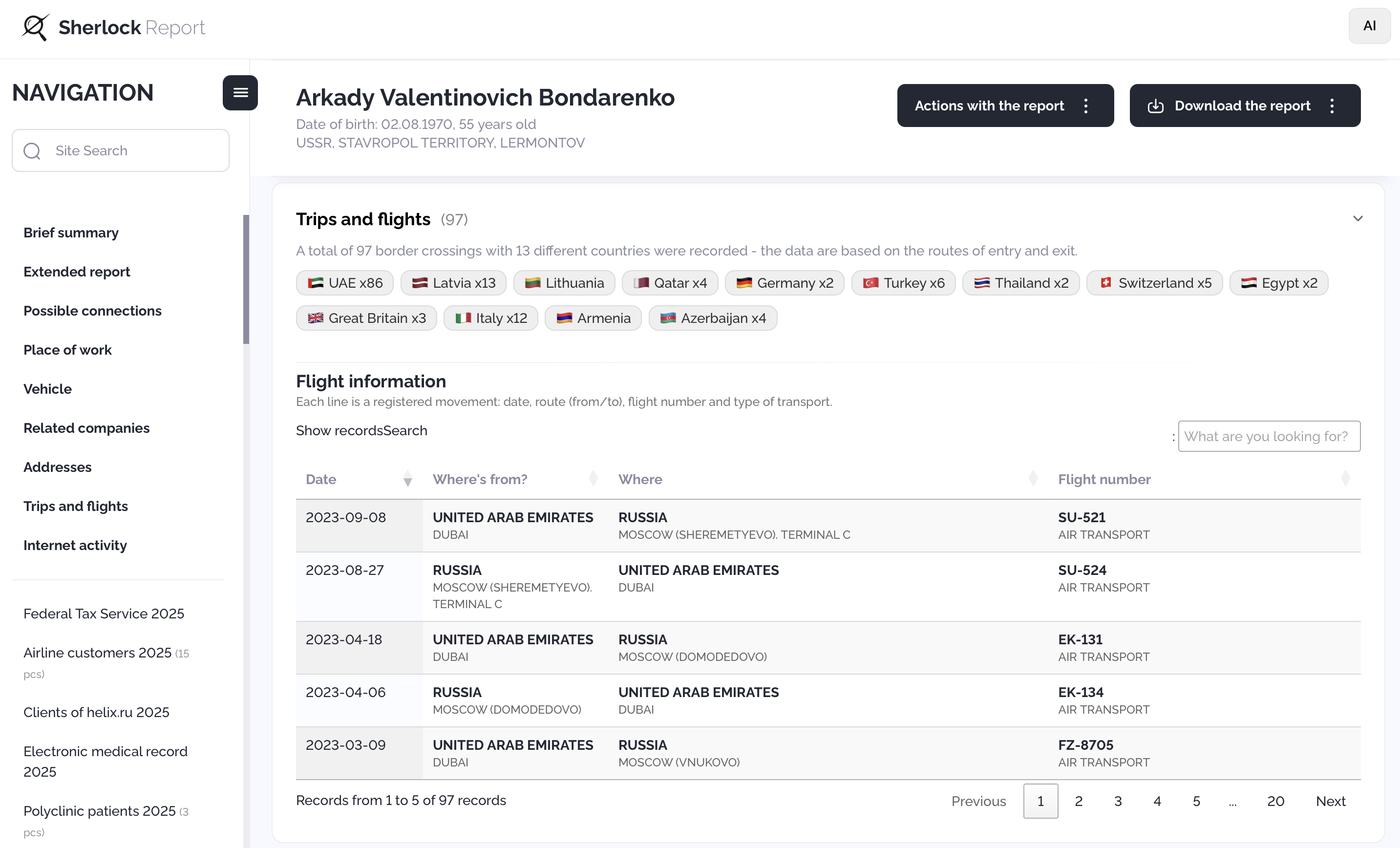
Who is Arkady Bondarenko
Arkady Bondarenko, a dual citizen (Russia and Canada) — a successful businessman with luxury real estate in Moscow, a network of financial-intermediary companies, and a fondness for private jets. In reality, he is a key “diplomat” of the Conti ransomware group, which from 2019 to 2022 extorted victims for around two hundred million dollars, attacking targets from hospitals to whole governments.
My previous investigations already pointed to Bondarenko as a negotiator-informant — a person who, apparently, squeezed the maximum from negotiations, knowing the internal workings of both sides.
 BONDARENKO ARKADY VALENTINOVICH 02.08.1970
BONDARENKO ARKADY VALENTINOVICH 02.08.1970
-
Identification in Conti chats
In the leak of Conti’s internal communications the following exchange is recorded:
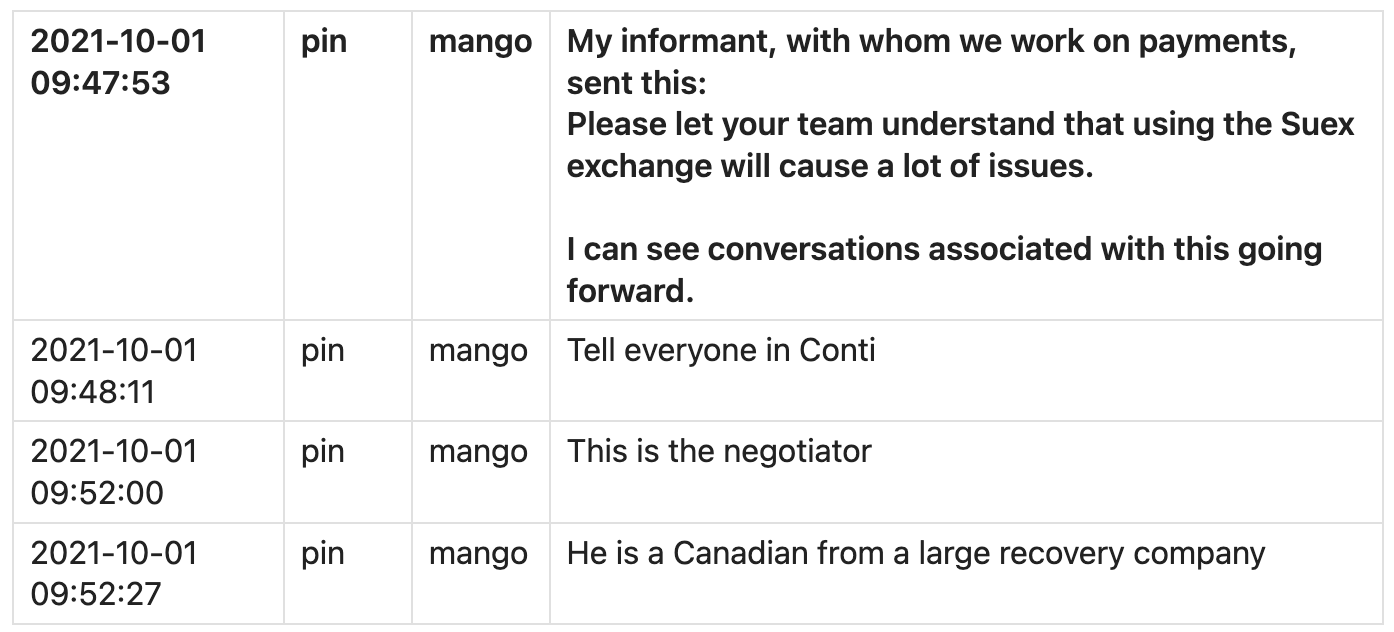
-
“Bondarenko Arkady holds Canadian citizenship. And he has ties with Conti leaders.”
-
On the very day these messages were sent (1 October 2021) Bondarenko flew from Dubai to Moscow (flight EK-133).
Here is another Conti chat where the same participant (“pin”) refers to his negotiator from a firm that conducts negotiations on behalf of the victim:
The context of the messages clearly indicates a person who negotiates on behalf of victims while maintaining direct contact with Conti.
It is obvious that this is the same negotiator — Bondarenko.
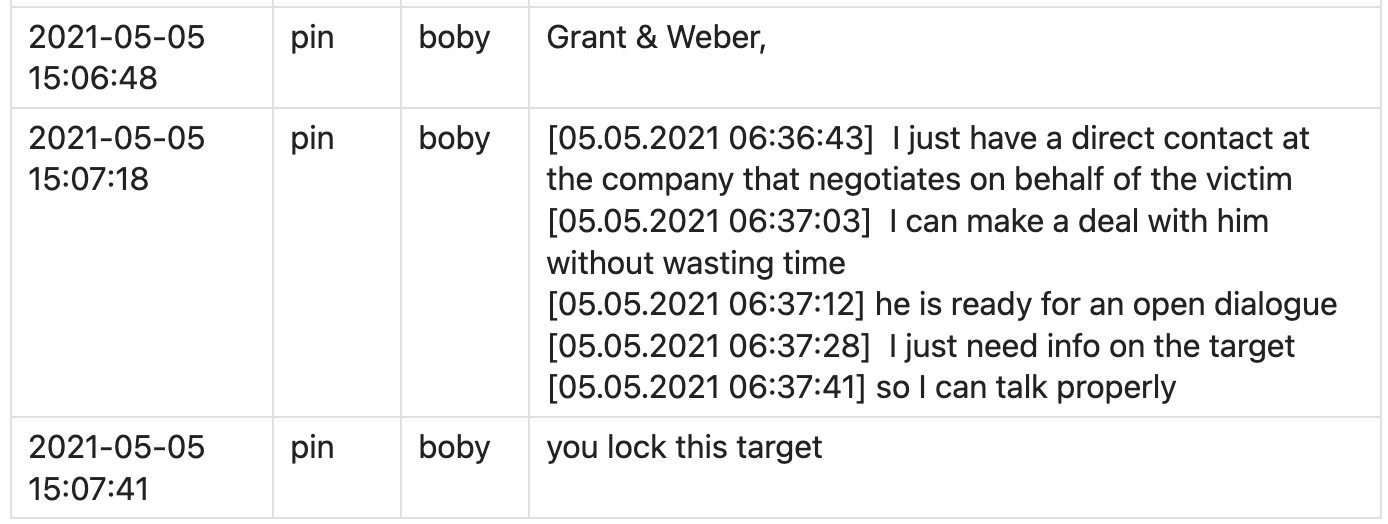
Grant & Weber — an American debt collection and revenue cycle management company operating since 1977.
Address: 26610 Agoura Road, Suite 209, Calabasas, CA
Phones: (800) 947-1656, (702) 366-7008
Website: grantweber.com
This is an important lead that journalists and law enforcement should check. Contact Grant & Weber about this incident — which recovery company they engaged and who conducted negotiations.
-
The triangle with Conti’s ringleaders
To prove that Bondarenko is not a random middleman but someone tightly embedded in Conti’s core, just look at his multi-year travel history.
For years he regularly flew together with two of Conti’s key figures:
-
 Aleksey Kurashov (Target) — one of CONTI’s leaders, an organizer.
Aleksey Kurashov (Target) — one of CONTI’s leaders, an organizer. -
 Vladimir Kvitko (Professor) — one of CONTI’s leaders, hacker, negotiator.
Vladimir Kvitko (Professor) — one of CONTI’s leaders, hacker, negotiator.
Kurashov Aleksey — shared flights:
to UAE Dubai 24.09.2021 flight EK-134 from Moscow — Bondarenko + Kurashov
to UAE Dubai 25.09.2022 flight EK-134 from Moscow — Bondarenko + Kurashov
to UAE Dubai 15.10.2023 flight A6EDQ from Moscow — Bondarenko + KurashovKurashov Aleksey — close-by flights:
to UAE Dubai 26.03.2024 from Russia — Kurashov
to UAE Dubai 27.03.2024 from Russia — Bondarenko
Kvitko Vladimir — close-by flights:
to UAE Dubai 03.11.2018 flight EK-134 from Moscow — Bondarenko
to UAE Dubai 03.11.2018 flight SU-520 from Moscow — Kvitkoto UAE Dubai 24.10.2019 flight EK-134 from Moscow — Bondarenko
to UAE Dubai 25.10.2019 flight SU-524 from Moscow — Kvitkoto UAE Dubai 17.01.2020 flight EK-134 from Moscow — Bondarenko
to UAE Dubai 17.01.2020 flight SU-522 from Moscow — Kvitkoto UAE Dubai 25.09.2020 flight EK-134 from Moscow — Bondarenko
to UAE Dubai 26.09.2020 flight SU-522 from Moscow — Kvitko
Kurashov and Kvitko — shared flights:
to UAE Dubai 14.10.2021 SU-520 from Moscow
to UAE Dubai 05.02.2021 SU-524 from Moscow
to UAE Dubai 08.11.2019 EK-134 from Moscow
There are also other patterns in the timeline where Kvitko, Kurashov and Bondarenko visit the UAE several times on a kind of schedule — one leaves, another arrives. Example:
from UAE Dubai 23.01.2021 SU-525 to Moscow — Kvitko
to UAE Dubai 23.01.2021 EK-132 from Moscow — Bondarenko
from UAE Dubai 27.01.2021 SU-521 to Moscow — Kurashov
from UAE Dubai 03.02.2021 EK-133 to Moscow — Bondarenko
to UAE Dubai 05.02.2021 SU-524 from Moscow — Kvitko
to UAE Dubai 05.02.2021 SU-524 from Moscow — Kurashov
This is not two or three coincidences. These are dozens of matches stretched over years.
These are not “circumstantial coincidences.”
They are chronologically precise synchronizations, verified by border databases and airline records.
All three figures regularly visited Dubai, which for a long time has been one of the key “havens” for Conti’s cybercriminal operations.
And all this demonstrates a direct, long-term connection between Bondarenko and Conti’s two main ringleaders.
-
A brief summary of evidence on Target and Professor
In my separate work “Hunting the Shadow of Conti” I explained in detail how I identified the two key Conti members — Target (Kurashov) and Professor (Kvitko). Their identification is not based on a single circumstantial fact, but on a set of independent facts that converge on the same people. In the case of Target (Aleksey Kurashov) several lines matched at once: unique features of his communication style in Conti chats, his contacts and repeated travel companions, as well as the timing of synchronized flights to the UAE. Key chat messages (“we send the guys early in the morning”, “I’ll be without access until Friday…”) matched the dates and routes of his real departures and disappearances from the network. These data were checked via border databases, flight history and crossing records.
Identification of Professor (Vladimir Kvitko) relies on the same scheme: the timing of his chat accounts’ activity fully coincided with his documented flights. The phrase “I’ll be there in a couple of hours, I’m on the road” fell exactly at the time of his Novosibirsk–Moscow flight, which is confirmed by the “Magistral” database. Additionally, age (a “couple of years” difference compared to Target), roles in the group and overlapping routes with Kurashov matched. All these signs are independent of one another, but point to the same result. Therefore, the conclusion about their identification is not speculation — it follows from objective data that corroborate each other.
-
Triple extortion in action
Conti was believed to use double extortion:
-
encrypt the data,
-
publish stolen files.
But in reality a harsher format emerged — triple extortion.
They placed “their person” into negotiations on behalf of the victim via a recovery company.
If a victim sought help, they ended up… directly with the group’s negotiator.
Here is another dialogue from Conti chats:
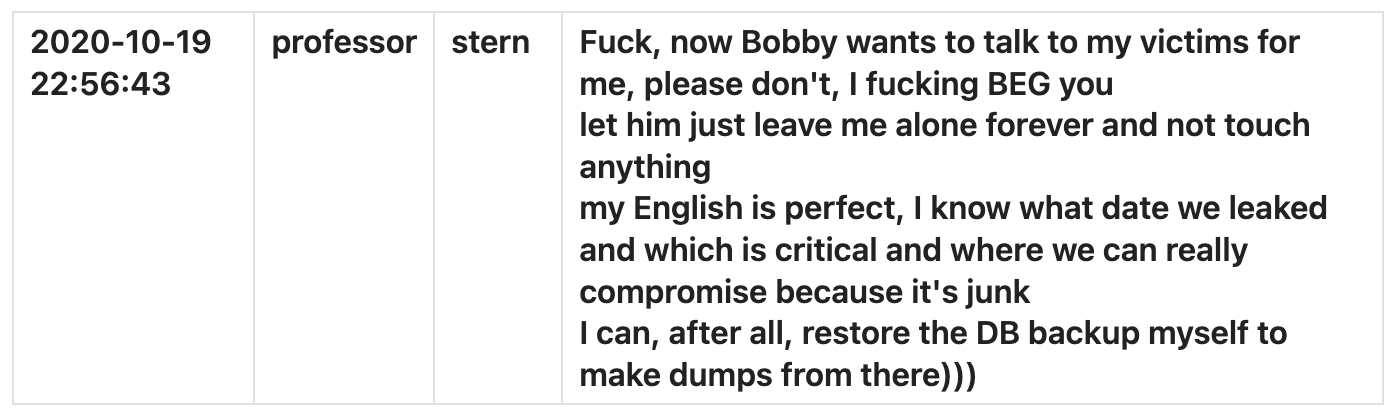
As seen from the dialogues, Professor (Kvitko) personally conducted ransom negotiations with his victims.
If you add Bondarenko’s ties to Kvitko and Bondarenko’s simultaneous work in recovery companies — you get the perfect triple extortion scheme: the victim pays the criminals and the “own” negotiator who actually works for the same people.
And this is roughly how the extortionists’ ambitions look when they have a confident negotiator who fully controls the situation:
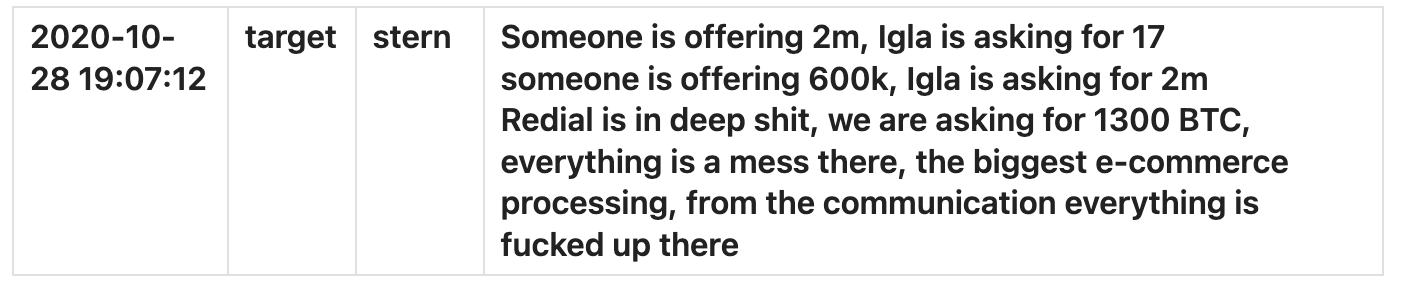
These mentions concern the negotiator Igla (voron, Ryuk); I will publish a separate piece on him.
-
How to verify the data yourself
For independent verification I recommend using the Telegram bot:
@Sherlock_GangIntel_bot
By full name and date of birth it returns:
- photos,
- passport data,
- full border-crossing history (FSB “Kordon-2023” leak),
- other leaks (addresses, relatives, cars, real estate, etc.)
This allows you to independently verify all my work and conduct your own investigations.
Important clarification: I have no relation to this information system and am not connected to it.
Example report — query by full name + DOB "БОНДАРЕНКО АРКАДИЙ ВАЛЕНТИНОВИЧ 02.08.1970" (in Russian):
https://dc6.sherlock-report.at/r/35cf98f8-ab57-42e4-aa6d-5d661bcdf919-31bb1e2ab458a706b1#
Translated from Russian
Also, I can advise where to acquire the full leaked FSB Border Service database “Kordon 2014–2023.”
You can contact me in private messages.
-
Bondarenko’s team
A separate investigation showed: Bondarenko surrounded himself with a small but stable personal team — people who participated in logistics, financial flows and technical support.
 LI ZEE 20.05.1987
LI ZEE 20.05.1987
 SMIRNOV DMITRY MIKHAILOVICH 08.09.1985
SMIRNOV DMITRY MIKHAILOVICH 08.09.1985
 ABDULLAIEV ILGAR OGLY 25.06.1972
ABDULLAIEV ILGAR OGLY 25.06.1972
 Lyong Suan 22.02.1990 (presumed)
Lyong Suan 22.02.1990 (presumed)
Abdullaiev and Smirnov are confirmed figures who participated in Conti’s schemes at various levels.
-
A few words about my methods
There is an old puzzle: connect nine dots with four straight lines without lifting the pencil.

Most cannot solve it because they mentally limit themselves with an imaginary square around the dots. That limitation is not part of the condition.
I solve the Conti puzzle the same way — I go beyond standard OSINT:
-
HUMINT
-
stylometry
-
correlation of digital traces
-
honeypots
-
real-time behavioral observation
-
direct contacts and active measures where passive search has long been exhausted.
Everything is within the law.
Everything is verifiable.
I do not hide that I work offensively, but I act ethically. These people know about me, run counter-operations, try to identify me, publish disinformation.
They do not act ethically; they do not care about the law.
They have repeatedly blocked my channels — and continue to try.
But I have a principle: I do not back down.
If you are reading this text — their attempt has failed again.
My restored Telegram channel with more detailed materials in English and Russian:
👉 https://t.me/gangexposed_int
-
Why it is important to spread this data
Bondarenko, Kurashov, Kvitko and their accomplices evaded investigations for years.
But now their roles are established clearly and with documentation.
I am not seeking fame. I act anonymously, within the law and in the interest of public safety.
This investigation can become the starting point for serious criminal cases — but only if the information is heard.
If you are a journalist, analyst or law-enforcement officer — take any data, verify it, publish.
The wider the distribution, the less chance they have to remain in the shadows.
-
What comes next
In upcoming publications I will reveal:
real-time HUMINT methods,
how interactions between Conti participants are organized after its reorganization,
how I established direct contacts with several key figures,
why stylometry became my secret weapon against anonymous hackers,
how I track their current behavior, movement, communications and attempts to hide.
This will be a series revealing something never before published publicly:
how offensive intelligence is conducted against cybercriminal syndicates — step by step, in the field.
