PART 0. BACKGROUND
NET-WORKER: how a Conti hacker gave himself away with a single phrase
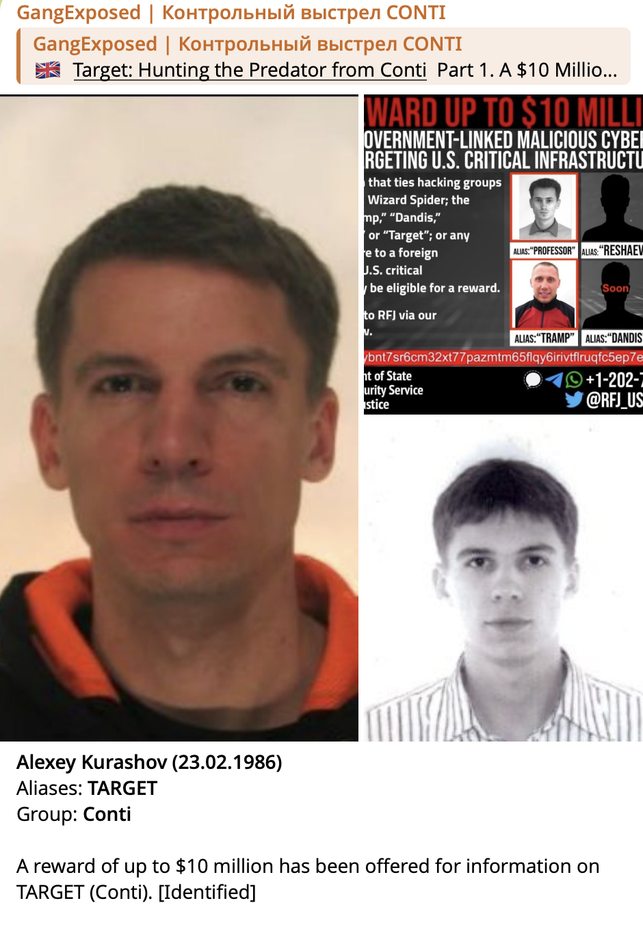
When you dig into the dark corners of the darknet, expect surprises. One of them is NET-WORKER, who presented himself as a young hacker with connections to LockBit and access to Russian special services.However, an analysis of his behavior, speech, and digital footprints shows: behind this persona is not a teenager at all, but Aleksey Kurashov, also known as Target — one of the leaders of the Conti Ransomware group. What gave him away was not a sophisticated exploit, but the habit of writing “дадада” (“yeah yeah yeah”).
The comment that launched the investigation
NET-WORKER came into my field of view on June 24, 2025, after I published my investigation about Oleg Fakeev (White) — a Conti pentester and close friend of Aleksey Kurashov. Under this material in my Telegram channel, he left a sarcastic comment:
“Yeah yeah yeah little bro, Bloomberg is such a f***ing authoritative publication, sure, go on.”
At first glance — ordinary trolling. But this exact manner of speech had appeared before.In the leaked internal Conti chats, one participant with the nickname target very often used the same constructions:
Such speech habits are rarely controlled and often persist for years. In criminal investigations, this is called a behavioral marker.
2020-09-17 10:34:08 target bentley yes yes yes yes2020-10-02 00:00:07 target troy I’m saying yes yes yes2020-09-25 10:11:30 target professor yeyayea2020-09-25 10:10:49 target professor yeayea
When I wrote to NET-WORKER in private messages, calling him “Alex”, he almost immediately deleted all his comments under the post. Well, what cybercriminal wouldn’t panic after that?
The “teenage genius” persona
In correspondence, NET-WORKER built an elaborate legend. According to his messages, he:
- founder of the NET-WORKER ALLIANCE project
- gives interviews to the media
- consultant and contractor for SVR, FSB Cybersecurity Service, Rostec, Ministry of Defense, and Roscosmos
- organizer of DDoS operations against Moldova’s infrastructure “on behalf of Gazprom”
- de-anonymized members of the hacktivist group KillNet
- destroyed infrastructure of the hacker group Anonymous
- technical employee of the darknet drug marketplace MEGA, allegedly acting “for ideological reasons”
- partner of LockBitSupp, involved in cryptocurrency laundering
- owns more than 6000 BTC
What was confirmed
Analysis of correspondences, chats, and activity shows that NET-WORKER is Aleksey Kurashov, who continued working in the darknet after the collapse of Conti in 2022.Facts:
- In 2023, he infiltrated the drug marketplace MEGA posing as a moderator
- https://knds.com/fr/communiques-de-presse/cyber-incident
- https://tass.ru/obschestvo/18848397
- Participated in DDoS attacks on competitors
- Engaged in de-anonymization of key hacker groups and darknet figures
- There are darknet ads where criminals themselves offer $50,000 for NET-WORKER’s de-anonymization and “$10,000 for his fingers”
- Recorded episode of distribution of narcotic substances on a particularly large scale worth 6.4 million rubles "October 5, 2023: “Total stash amount 6.4 million ₽” (HUSTLE FAMILY, imsg_bot)"
- There are public correspondences indicating cooperation with Russian structures and industrial espionage in the military-industrial complex
- LockBitSupp publicly confirmed their acquaintance
Threats
When it became clear he was being identified, the tone of the correspondence changed sharply.First — attempts to evoke sympathy: that my publications destroy families, people’s businesses collapse, he allegedly helps victims financially.
Then — threats followed:
“I have more than 6000 bitcoinsI can buy a countryTanksAirplanesI can start a war with the FBIA real oneI can declare an action like EscobarKill copsOr rather FBI agents”
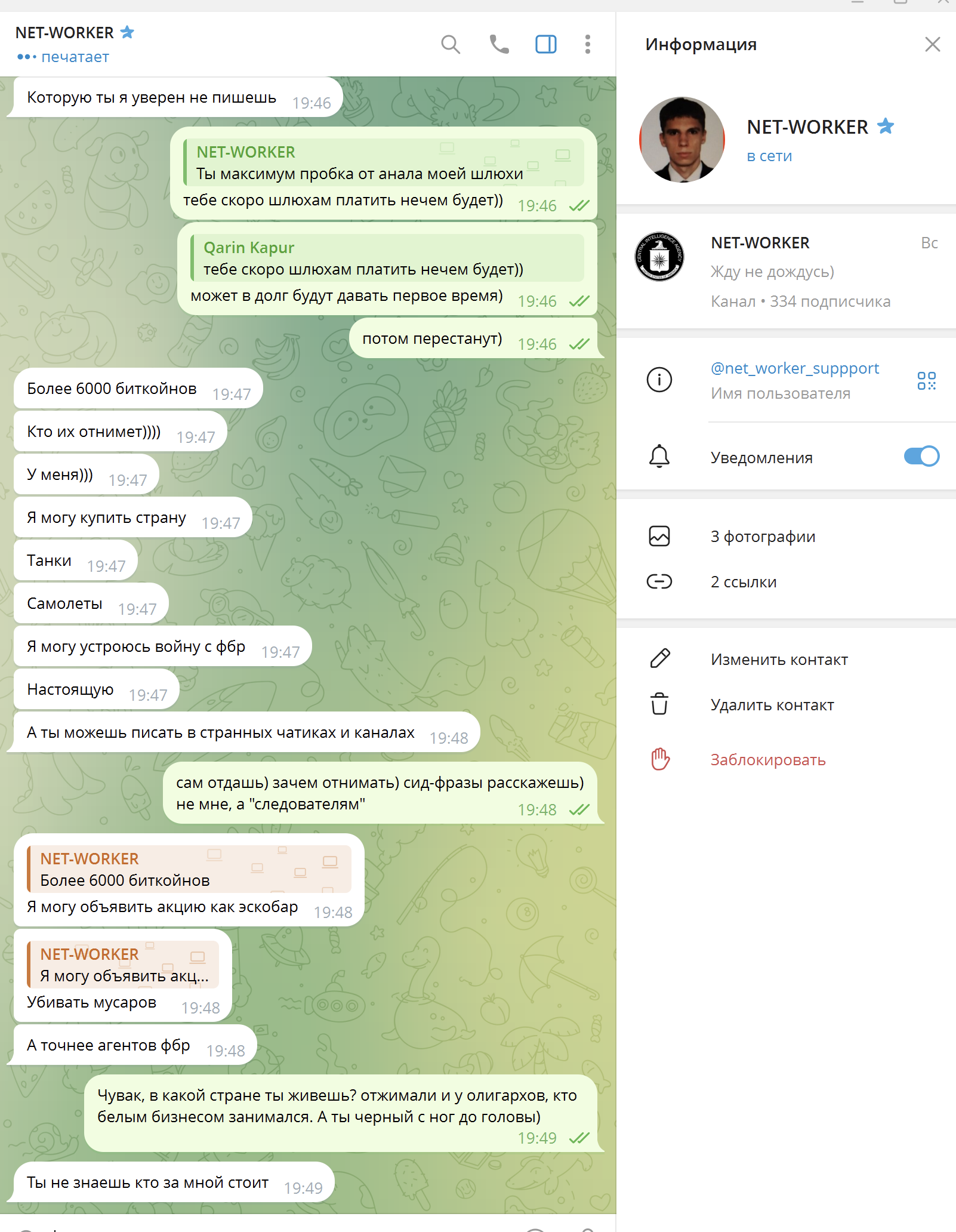
(NET-WORKER gave consent to publish our correspondence. At the time of the dialogue, there was no photo on the avatar; the screenshot was taken later. These threats were made to me in the context that Kurashov (NET-WORKER, Target) was convinced that I was an FBI employee. Later, he repeatedly publicly reaffirmed these threats when I showed this screenshot in Telegram groups.)
There were also threats of brutal physical violence, which are not quoted here.After that, he proposed a “peace agreement”: delete the published materials in exchange for “reconciliation”. The offer was declined.
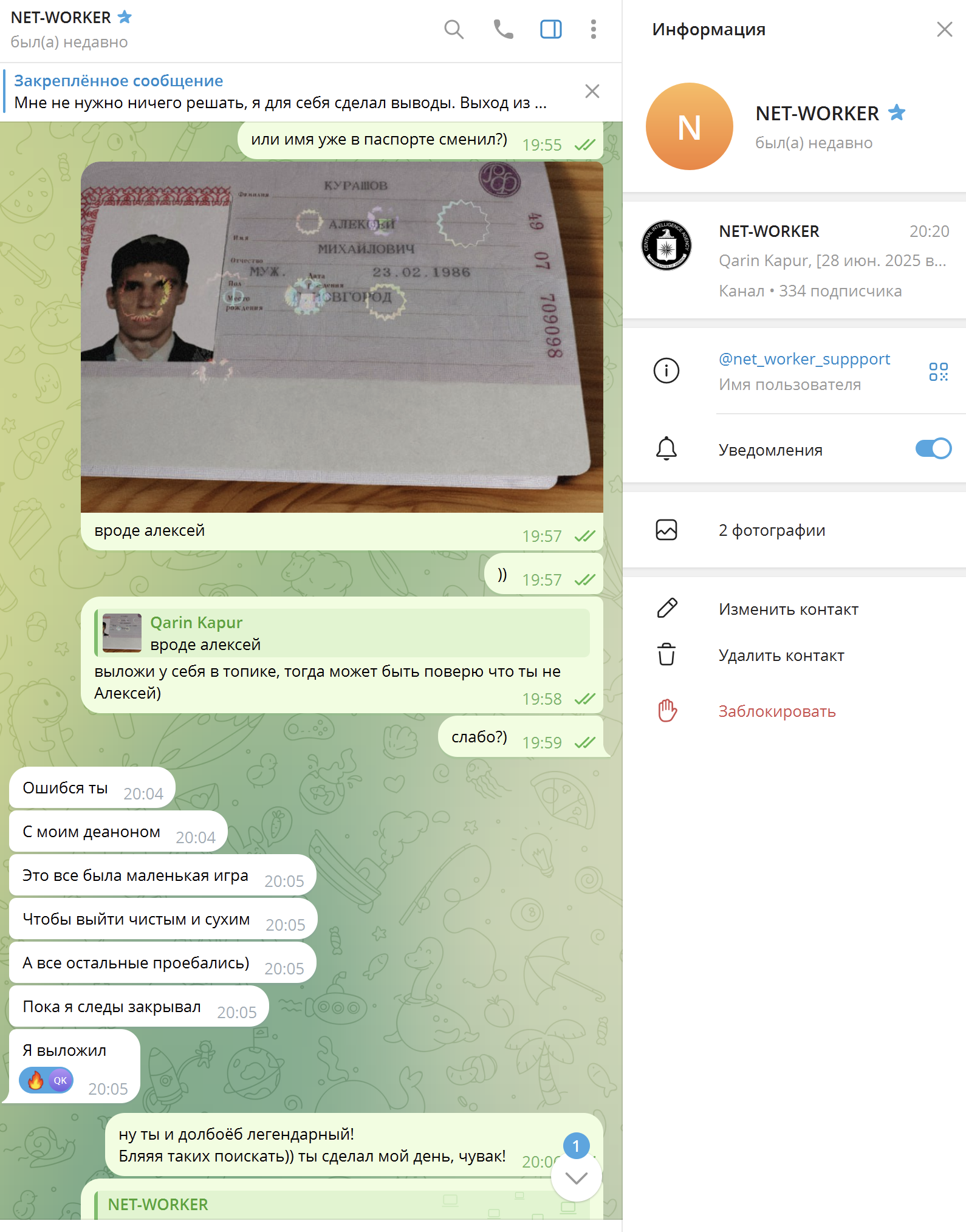
Attempt to hide behind a “schoolboy” again
After the refusal, NET-WORKER claimed that he was just trolling and “pretending to be Target”.
He sent voice messages (voice of a young man about 15-20 years old) and geolocation, demonstrating that he is a teenager and not hiding.In response, I suggested a simple test — put Kurashov’s passport on the avatar. He agreed and did it (it should be clarified that at that moment I had not yet published anything about Target-Kurashov; I did so only in August 2025).
He sent voice messages (voice of a young man about 15-20 years old) and geolocation, demonstrating that he is a teenager and not hiding.In response, I suggested a simple test — put Kurashov’s passport on the avatar. He agreed and did it (it should be clarified that at that moment I had not yet published anything about Target-Kurashov; I did so only in August 2025).
Additionally, a repeated stylometric analysis was performed. Result: complete match with the RED account from Conti’s Rocket-Chat, another pseudonym of Target (Kurashov).
The “drop” role
During the investigation, the name Kirill Panteleev, born in 2008, surfaced. His videos and voice match part of the materials sent by NET-WORKER.With high probability, the teenager was used as cover, but the account is controlled by Target (Kurashov) himself. A classic scheme for communicating with the media and deflecting suspicion.
Same speech, same thinking
Final confirmation — the language.Target in Conti chats previously wrote:“The office should pay for itself, not reach into pockets.”NET-WORKER wrote:“It’s not worth reaching into my pocket, everything is fine there.”Or:Kurashov:“Send it wherever you want — they’ll laugh at you.”NET-WORKER:“Send it to the FBI — they’ll laugh.”This is not copying. This is the same way of formulating thoughts.
Conclusion
NET-WORKER is not a teenage genius and not a new figure in the darknet. It is Aleksey Kurashov, who after the collapse of Conti created a completely new persona for himself.But habits, language, and behavior gave him away faster than any leak.
Instead of anonymity, he left a detailed digital trail — thereby exposing not only himself, but also his activities after Conti.
Instead of anonymity, he left a detailed digital trail — thereby exposing not only himself, but also his activities after Conti.
Let’s now prove it.
PART 1
De-anonymization without content: how Telegram metadata, traffic fines, and flights form one profile
One public message in Telegram gives almost nothing.
Ten messages — also almost nothing.
Even a hundred messages — these are just recorded moments of activity: the user was online, wrote something in a public chat, and disappeared.But what if there are thousands of such messages?
What if they are distributed over time not randomly, but with repeating intervals, gaps, and bursts?
What if these points on the timeline are matched against other, external data sources?In this part, I show how even with strict OPSEC compliance and complete absence of personal information in public messages, a person leaves a stable behavioral trace that can be recorded, visualized, and analyzed.We are not talking about the content of correspondences.
Only metadata. Only correlation. Only patterns.
Ten messages — also almost nothing.
Even a hundred messages — these are just recorded moments of activity: the user was online, wrote something in a public chat, and disappeared.But what if there are thousands of such messages?
What if they are distributed over time not randomly, but with repeating intervals, gaps, and bursts?
What if these points on the timeline are matched against other, external data sources?In this part, I show how even with strict OPSEC compliance and complete absence of personal information in public messages, a person leaves a stable behavioral trace that can be recorded, visualized, and analyzed.We are not talking about the content of correspondences.
Only metadata. Only correlation. Only patterns.
Problem statement
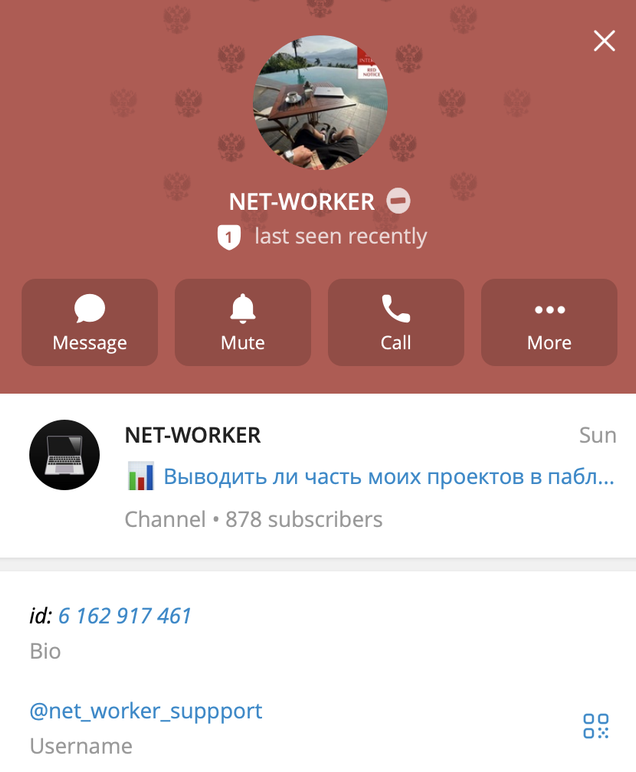
At the center of the analysis is the Telegram account NET-WORKER @net_worker_suppport and a specific person — Aleksey Mikhailovich Kurashov, born February 23, 1986.
The task is extremely simple and at the same time complex:
At the center of the analysis is the Telegram account NET-WORKER @net_worker_suppport and a specific person — Aleksey Mikhailovich Kurashov, born February 23, 1986.
The task is extremely simple and at the same time complex:
- does the same person operate the NET-WORKER account;
- can this activity be linked to Kurashov;
- with what degree of accuracy can this be done without resorting to message content;
- are there anomalies, and how to interpret them;
- does the totality of data allow a reasoned conclusion about de-anonymization.
Data sources
The analysis used available metadata from several independent sources:
The analysis used available metadata from several independent sources:
- Telegram activity
- more than 10,000 messages from the NET-WORKER @net_worker_suppport account ID 6162917461;
- sources: Telegram bots FanStat Bot @ShamiGems_bot (permanent link to the bot http://telelog.org/) and imsg Bot @imsg_bot — they allow exporting the user’s message history from open and even some closed group chats;
- mandatory synchronization of time zones to UTC+3 (MSK) (they differ in these services).
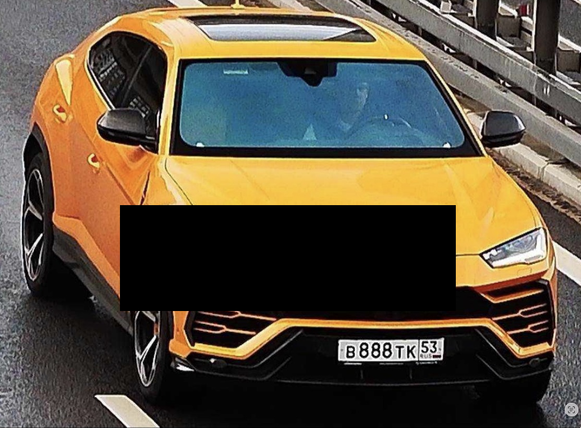
- Traffic fine history from GIBDD
- Lamborghini Urus vehicle, license plate в888тк53, STS 9941614859;
- Tesla Cybertruck vehicle, license plate а469мр77, STS 9963939949;
- data can be obtained legally through Avtokod, Drom, Avinfo, etc. — links https://vin.drom.ru/report/b888tk53/ and https://vin.drom.ru/report/a469mp77/ (≈$5 for both reports, payment only with Russian cards), but there are also free ways to get all fines;
- for 2023–2025 — 542 fines for Urus and 241 for Tesla (without duplicates);
- additionally — GIBDD fine data (including archive) can be purchased from https://probiv.space
- Photos and parking data
- both vehicles are regularly captured in parking spaces;
- parking spaces №3027, 3027, 3028 are owned by Aleksey Kurashov (see dossier);
- both vehicles were repeatedly recorded there in different months of 2024 and 2025;
- photos of these vehicles with parking spaces were legally and freely taken from Nomerogram — links https://www.nomerogram.ru/n/b888tk53-142f99e63/ and https://www.nomerogram.ru/n/a469mp77-184a93fb5/ (hundreds of photos of these vehicles available via these links)
- Flights
- data obtained through the “Magistral” system (source https://probiv.space)
- four independent reports from different contractors were used;
- period: 2023 — December 2024.
- 👉 RAW Data
- Attached documents
- Main file “NET-WORKER 6162917461 Timeline.ods” 👉 DOWNLOAD — all messages, fines, and flights combined into one table. Flights (green) and fines (yellow) are color-highlighted for quick search. (update: messages from user blood from the BlackBasta Matrix chat leak have been added to the general table — they are highlighted in red


Methodology
The key principle of the analysis is to reject details that distract from patterns.
At the first stage:
Value appears only when thousands of points from different sources are placed in parallel on one timeline.
The key principle of the analysis is to reject details that distract from patterns.
At the first stage:
- message text is not analyzed;
- the specific violation for which the fine was issued is not taken into account;
- flight geography is not important.
- chat message;
- camera violation recording;
- departure or arrival.
Value appears only when thousands of points from different sources are placed in parallel on one timeline.
Primary observations and timeline analysis
When analyzing the timeline, certain patterns immediately stand out. For detailed chronology, look in parallel at the NET-WORKER 6162917461 Timeline.ods table, where I marked and color-coded flights and fines for visual search convenience.
When analyzing the timeline, certain patterns immediately stand out. For detailed chronology, look in parallel at the NET-WORKER 6162917461 Timeline.ods table, where I marked and color-coded flights and fines for visual search convenience.
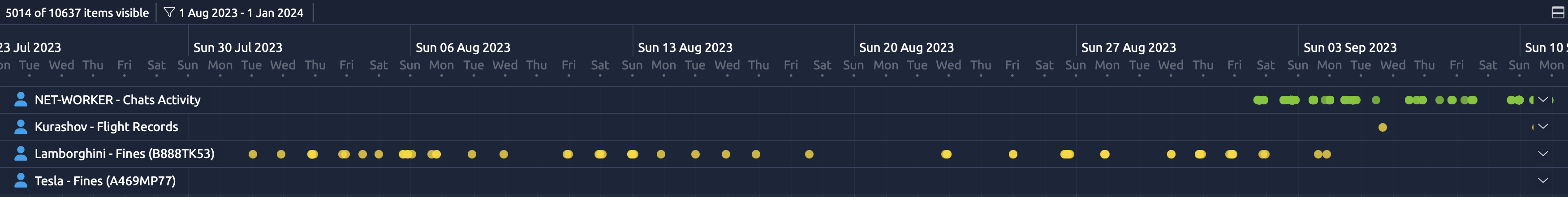
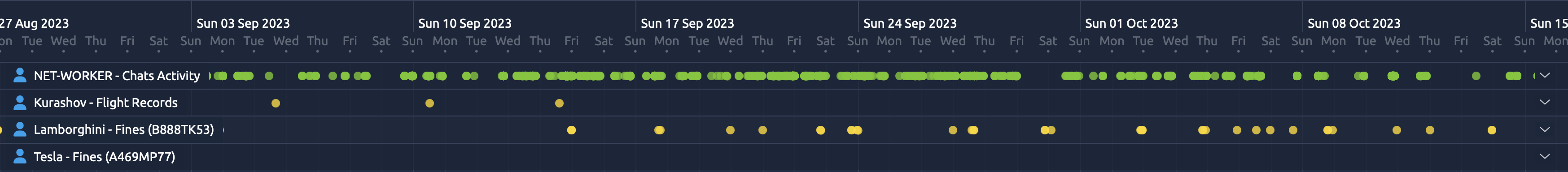
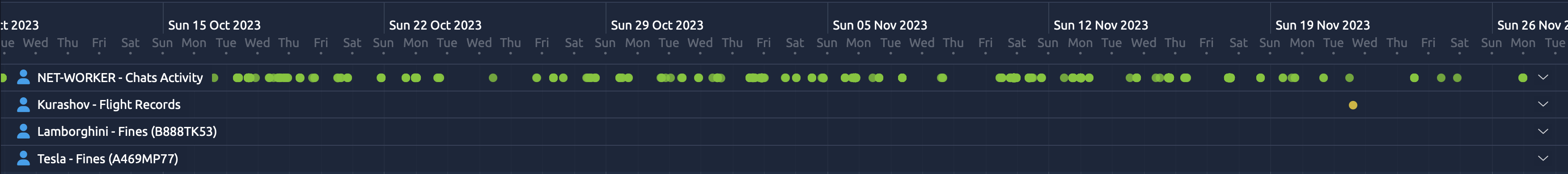
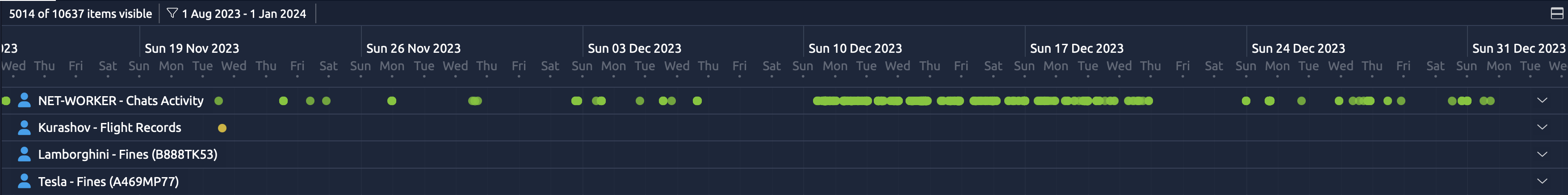
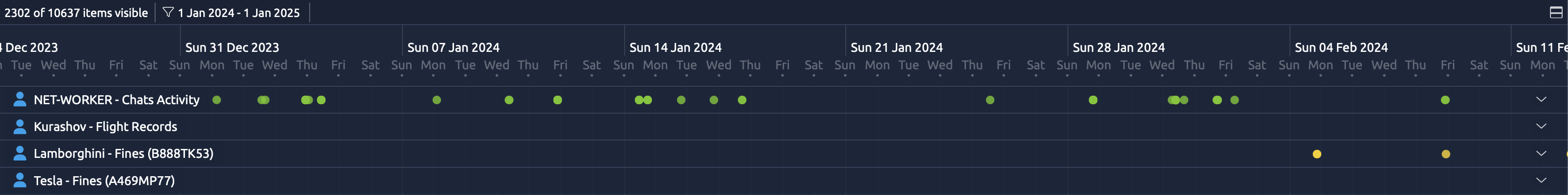
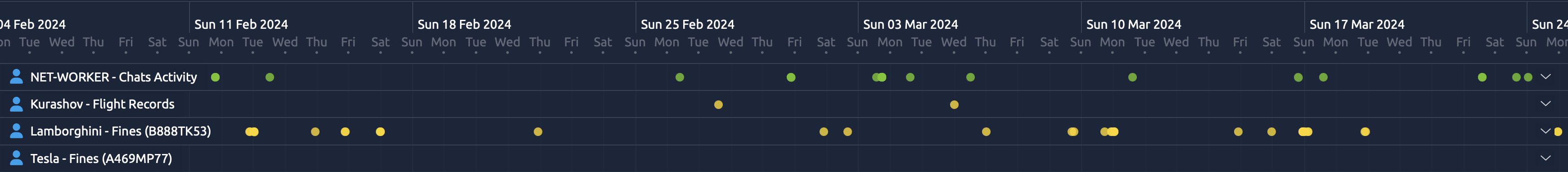
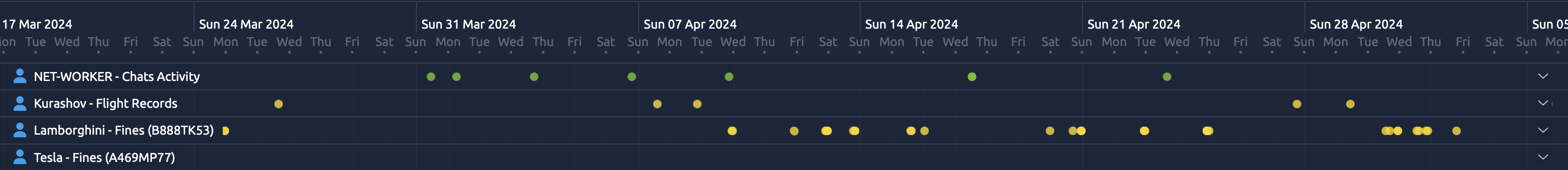
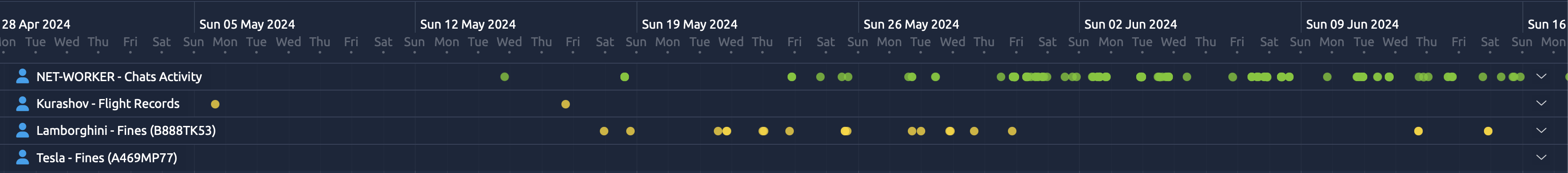
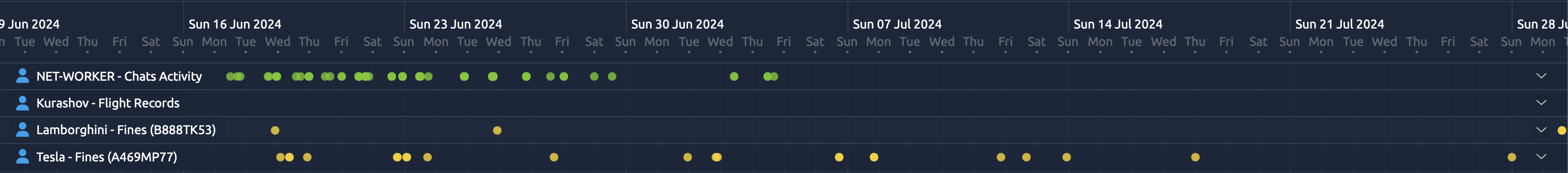
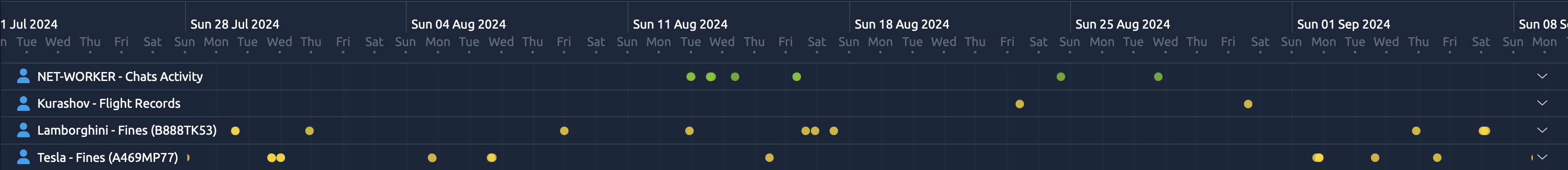
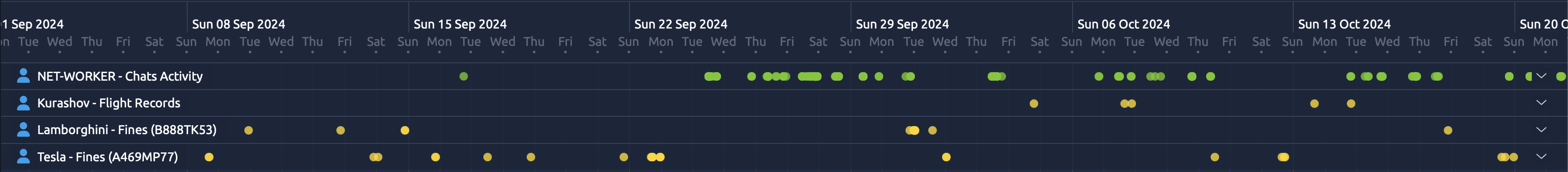
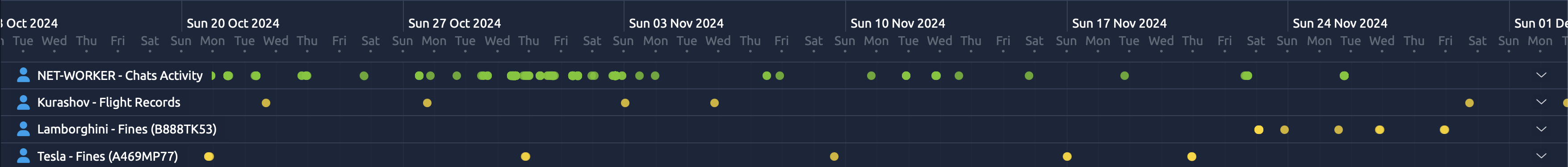
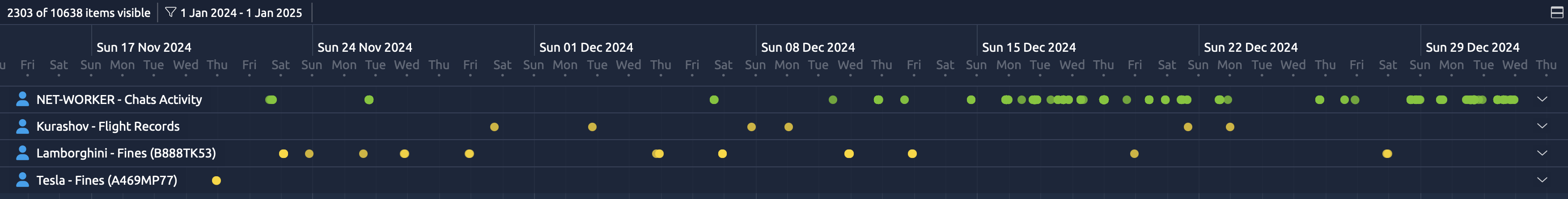
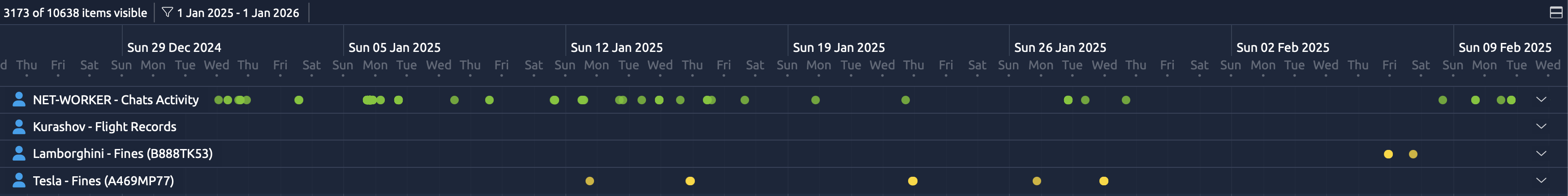
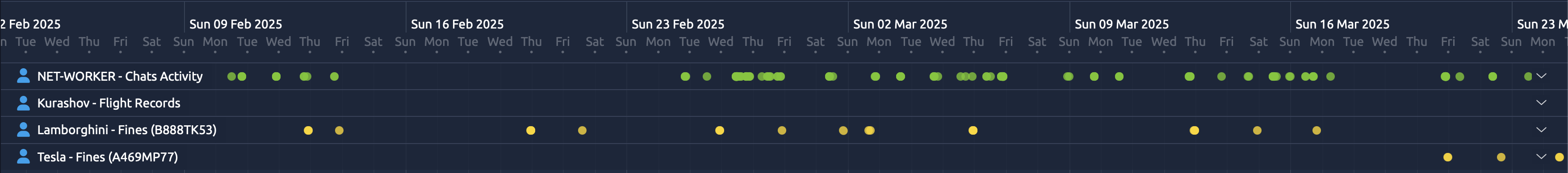
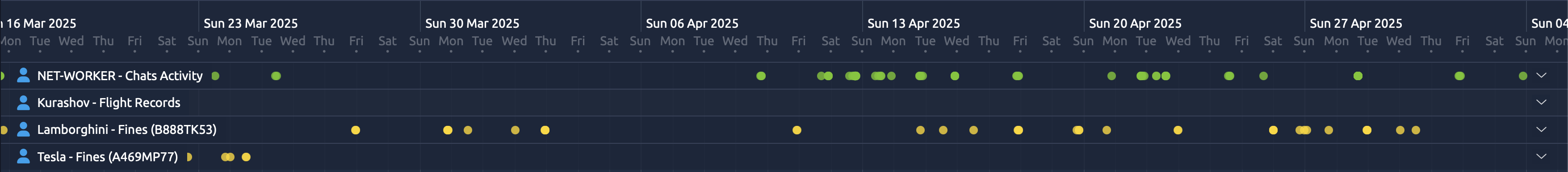
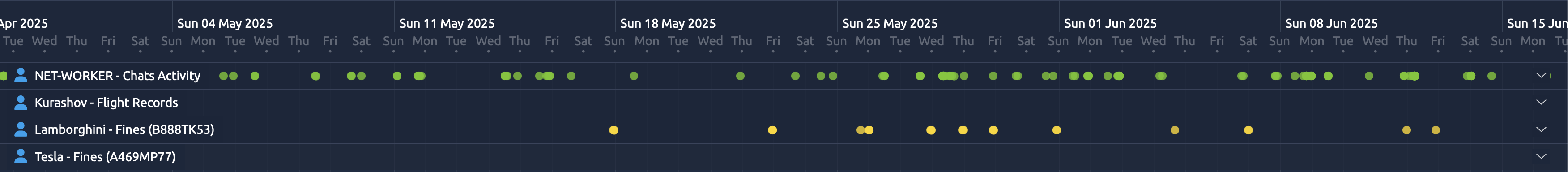
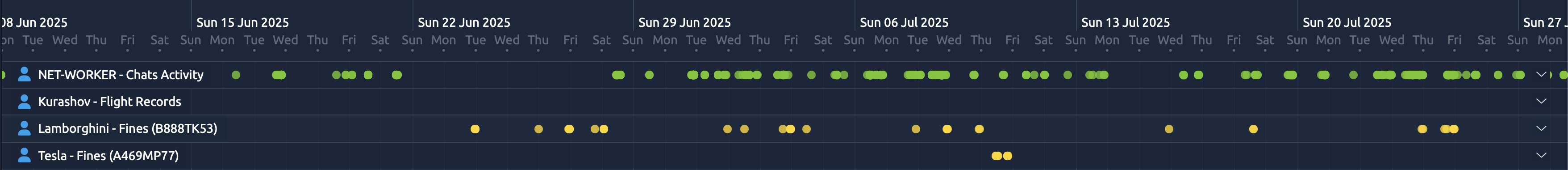
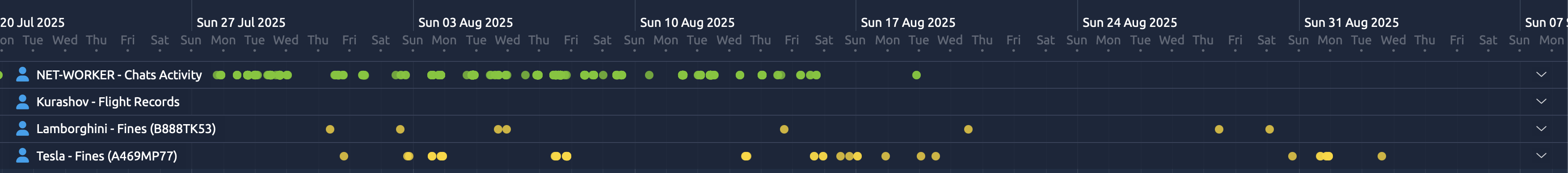
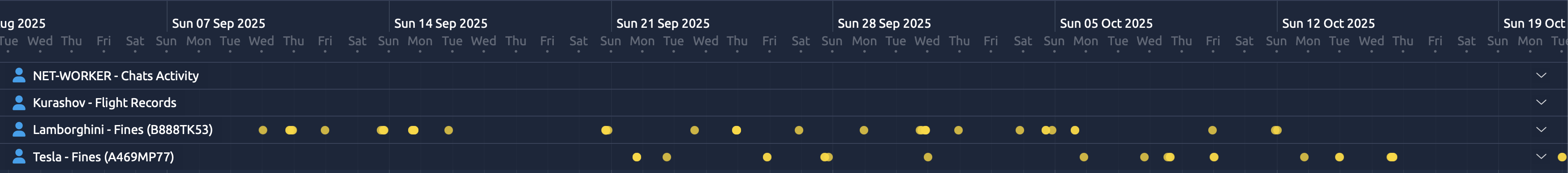
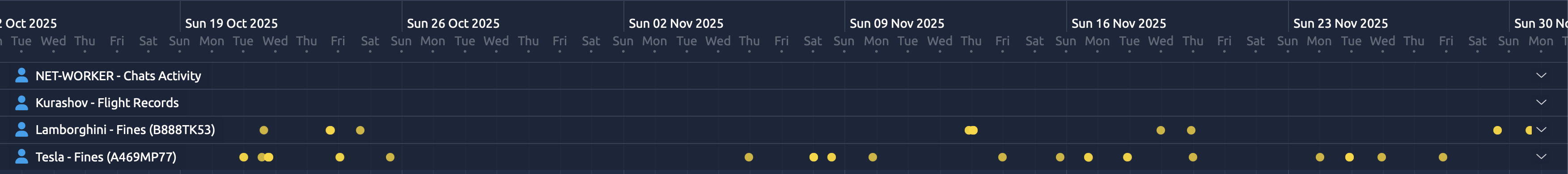
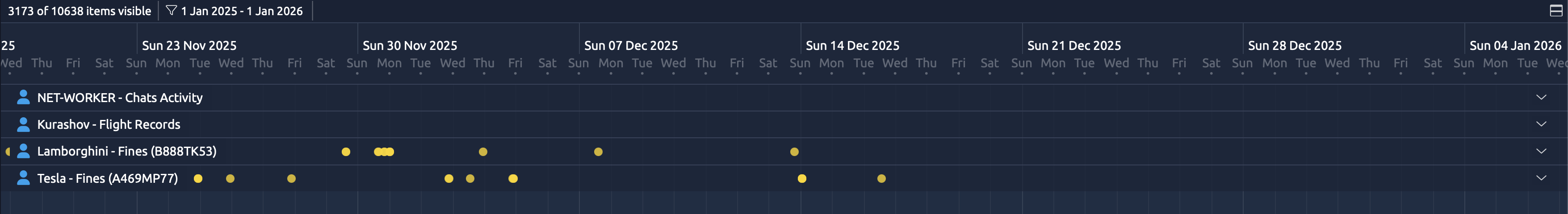
Absence of overlaps: fines and messages do not intersect in time
When overlaying two independent data streams — Telegram messages and GIBDD violation records — absolute absence of time overlaps is immediately noticeable.
Out of all 750+ fines, only one case showed minimal overlap (difference of tens of seconds, episode from 07.08.2025, described below). In all other cases, at least several minutes pass between the nearest NET-WORKER message and the fine recording moment.This is not random noise. This is a systematic picture over almost three years.
Out of all 750+ fines, only one case showed minimal overlap (difference of tens of seconds, episode from 07.08.2025, described below). In all other cases, at least several minutes pass between the nearest NET-WORKER message and the fine recording moment.This is not random noise. This is a systematic picture over almost three years.
Why it matters:
- GIBDD fines (mostly for speeding) are recorded at the moment when the driver is actively driving (or violated parking rules — but those are very rare).
- Active chatting in Telegram (NET-WORKER writes frequently, sometimes several messages in a row) requires attention: reading, typing, sending.
- A person can sometimes send a short message or one-word reply while driving, but maintaining a regular chat is extremely risky and atypical, especially at high speeds.
This creates a very strong marker: the “chat” and “driving” activities of the same profile are strictly separated in time. One person does not do both at the same time.The only noticeable anomaly (exception)
There is exactly one episode with minimal difference:
07.08.2025, daytime:
- 13:06:40 — message
- 13:07:00 — speeding fine
- 13:07:50 — message
- 13:08:00 — another speeding fine
- 13:08:32 — message
- at that moment someone else was driving the Tesla Cybertruck;
- or the messages were sent not by the driver (unlikely).
Using vehicles as a behavioral marker
The timeline clearly shows two lines — fines for Kurashov’s two vehicles.
Simple but telling observation:
The timeline clearly shows two lines — fines for Kurashov’s two vehicles.
Simple but telling observation:
- in the vast majority of cases, fines are recorded either on one vehicle or the other;
- on the same day, fines almost never appear on both at once;
- vehicles are not used in the morning and before lunch (12:00) — exceptions occurred a couple of times.
- noticeable when vehicles are used alternately, day after day (visually as a snake of dots on the graph).
- first day after purchasing the Tesla;
- several episodes starting from July 2025.
Flights and activity gaps
An additional layer — flights.
On the timeline it is noticeable:
An additional layer — flights.
On the timeline it is noticeable:
- during flight periods, activity in Telegram chats sharply disappears;
- after return, activity resumes;
- these “gaps” coincide in time with flights.

TABLE UPDATE: important correction, the Sochi-Moscow flight on 07.10.24 was canceled, ticket refunded.
07.10.24 20:10 ADLER - SOCHI SHEREMETYEVO (MOSCOW) REFUNDI found out that Kurashov flew first from Sochi to St. Petersburg, and then from SPb to Moscow — on the same day. The time shifted by 1 hour 50 minutes. That is, there were 2 flights that day, not one. He flew via Piter.
07.10.24 16:40 07.10.24 20:55 SOCHI () PULKOVO () 07.10.24 16:12 BOARDING07.10.24 22:00 07.10.24 23:30 PULKOVO () SHEREMETYEVO () 07.10.24 21:30 BOARDING
07.10.24 20:10 ADLER - SOCHI SHEREMETYEVO (MOSCOW) REFUNDI found out that Kurashov flew first from Sochi to St. Petersburg, and then from SPb to Moscow — on the same day. The time shifted by 1 hour 50 minutes. That is, there were 2 flights that day, not one. He flew via Piter.
07.10.24 16:40 07.10.24 20:55 SOCHI () PULKOVO () 07.10.24 16:12 BOARDING07.10.24 22:00 07.10.24 23:30 PULKOVO () SHEREMETYEVO () 07.10.24 21:30 BOARDING
Other important patterns:
- when Kurashov departs from Moscow — GIBDD fines are completely absent. When he arrives — fines appear.
Anomalies and their interpretation
As in any living dataset, there are deviations here:
As in any living dataset, there are deviations here:
- individual days with overlapping fines on both vehicles;
- pattern changes in mid-2025.
- emphasize that we are dealing with real behavior, not synthetic data;
- allow several interpretations: change of habits, vehicle handover, schedule change.
Key questions and answers
Is the same person behind the NET-WORKER account?
On the considered time interval, the data indicate a high probability of this.
On the considered time interval, the data indicate a high probability of this.
Can this activity be linked to Kurashov?
The correlation between Telegram activity, fines, flights, and daily habits points to the same person.
The correlation between Telegram activity, fines, flights, and daily habits points to the same person.
Can a definitive conclusion be made?
Absolute — no.
Reasoned with a high degree of confidence — yes.
Absolute — no.
Reasoned with a high degree of confidence — yes.
Can one “hide” while complying with OPSEC?
Content can be hidden.
But hiding the rhythm of life is significantly more difficult.
Content can be hidden.
But hiding the rhythm of life is significantly more difficult.
Conclusion
Each date and time a message is sent is just a tiny trace.
But when there are thousands of such traces, and other independent markers appear nearby, they form a clear behavioral profile.This story is about de-anonymization for 500 rubles.It is about how metadata that seems harmless turns out to be far more dangerous than any text.
And about the fact that perfect anonymity does not exist — there is only the illusion of it until someone assembles the full timeline.
Each date and time a message is sent is just a tiny trace.
But when there are thousands of such traces, and other independent markers appear nearby, they form a clear behavioral profile.This story is about de-anonymization for 500 rubles.It is about how metadata that seems harmless turns out to be far more dangerous than any text.
And about the fact that perfect anonymity does not exist — there is only the illusion of it until someone assembles the full timeline.
PART 2
Contextual facts: Finishing the de-anonymization with additional confirmations
To dispel any remaining doubts, let’s add a layer of context. Although the main analysis in PART 1 relies exclusively on metadata, rare “anomalies” in the data are not weaknesses, but additional evidence. Let’s take two cases where NET-WORKER activity continued during Kurashov’s flights (international flights with onboard Wi-Fi internet; domestic flights within Russia have no internet onboard). At first glance, this might suggest a second person behind the account. But upon closer examination of the message context (without violating the “no content” rule — only for interpreting anomalies), everything falls into place. These episodes do not destroy the hypothesis, but strengthen it, showing a real person in a real situation.
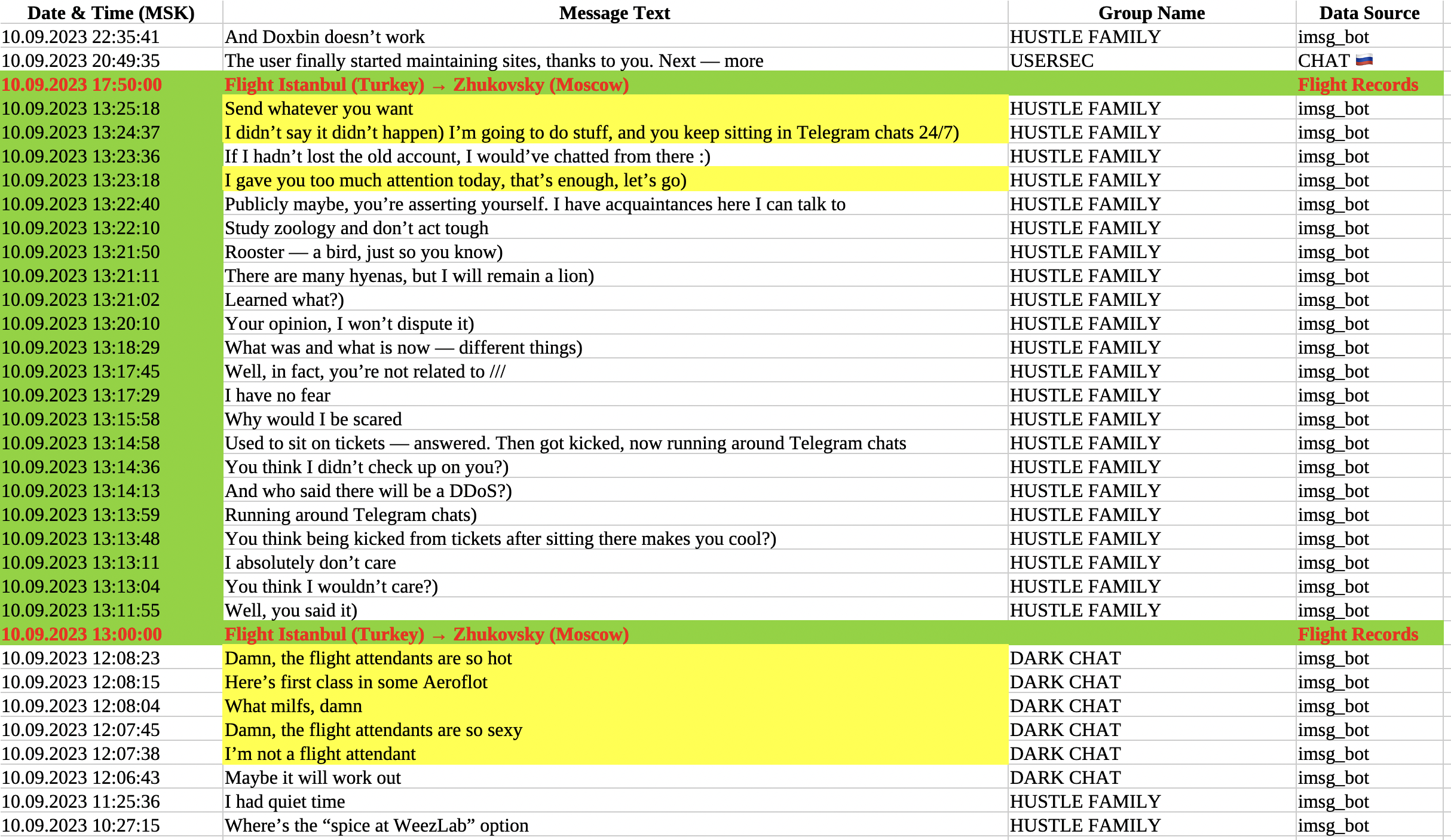
Istanbul — Zhukovsky (Moscow) flight, 10.09.2023
(Translated from Russian. The original message text is provided in the Russian version of the article)
Kurashov’s flight was scheduled for 13:00. NET-WORKER activity does not stop completely, but its context perfectly fits the “passenger on board” scenario:
- 50–55 minutes before departure (12:07–12:08): NET-WORKER actively jokes about stewardesses in the chat. Messages are full of enthusiasm: “Fuck the stewardesses are so sexy”, “What milfs damn”, “Here’s first class on some Aeroflot”, “Fuck there are such stewardesses”. This is typical “airport” humor — the person has just passed check-in or boarded the plane and sees the crew. The stewardess topic directly refers to the flight, and the timing matches the pre-departure period.
- During takeoff (13:23–13:25): Activity continues, but you can see NET-WORKER trying to end the conversation: “I paid you too much attention, enough for today, bye)”, “I didn’t say that never happened) I’m going to do things, and you keep sitting in telegram chats 24/7)”. Final message: “Send whatever you want” — and silence. This is classic: the passenger ends the chat because the plane starts takeoff, Wi-Fi drops, or the stewardess asks to put away devices. No messages during the flight — connection cuts off exactly at the start of the flight.
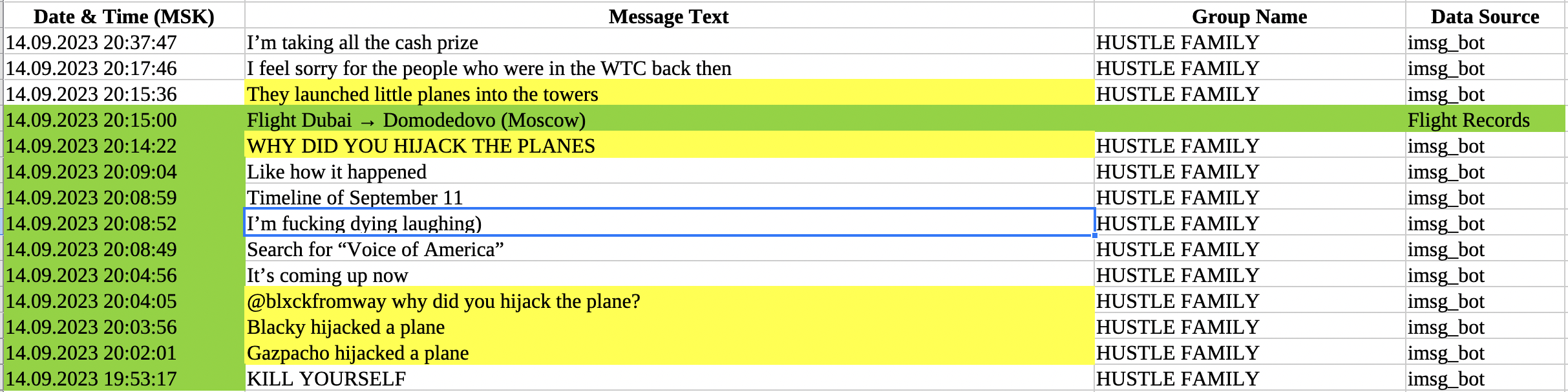
Dubai — Domodedovo (Moscow) flight, 14.09.2023
(Translated from Russian. The original message text is provided in the Russian version of the article)
Kurashov’s flight from 15:00 to 20:15 (including landing). NET-WORKER activity resumes closer to the end of the flight, and again the context screams “I’m on the plane”:
- During flight/landing (20:02–20:17): NET-WORKER suddenly starts joking about “hijacking planes” — “@blxckfromway why did you hijack a plane?”, “Blackie hijacked a plane”, “Gaspacho hijacked a plane”, “PLANES WHY DID YOU HIJACK”, “Little planes launched into towers”. The topic is 9/11 (flight a few days after the anniversary), but with humor about “plane hijacking”. This is not random flooding: a person on a plane, possibly joking with a neighbor, referencing the tragedy.
- Key fact: On this flight, Kurashov was traveling with his friend and partner Ivan Shvaikov (both participants in the Conti hacker group, as confirmed by my investigations on the GangExposed channel). The nicks mentioned in the messages (“Blackie” or “Gaspacho”) may refer to Shvaikov or their mutual acquaintances in the chat. Activity occurs during the landing phase — when Wi-Fi works, but the flight is not yet over, then breaks for 20 minutes after landing (exiting the plane), and then messages continue.
This is not an anomaly — it is a real “leak” of OPSEC in real time, where flight context breaks through the metadata.
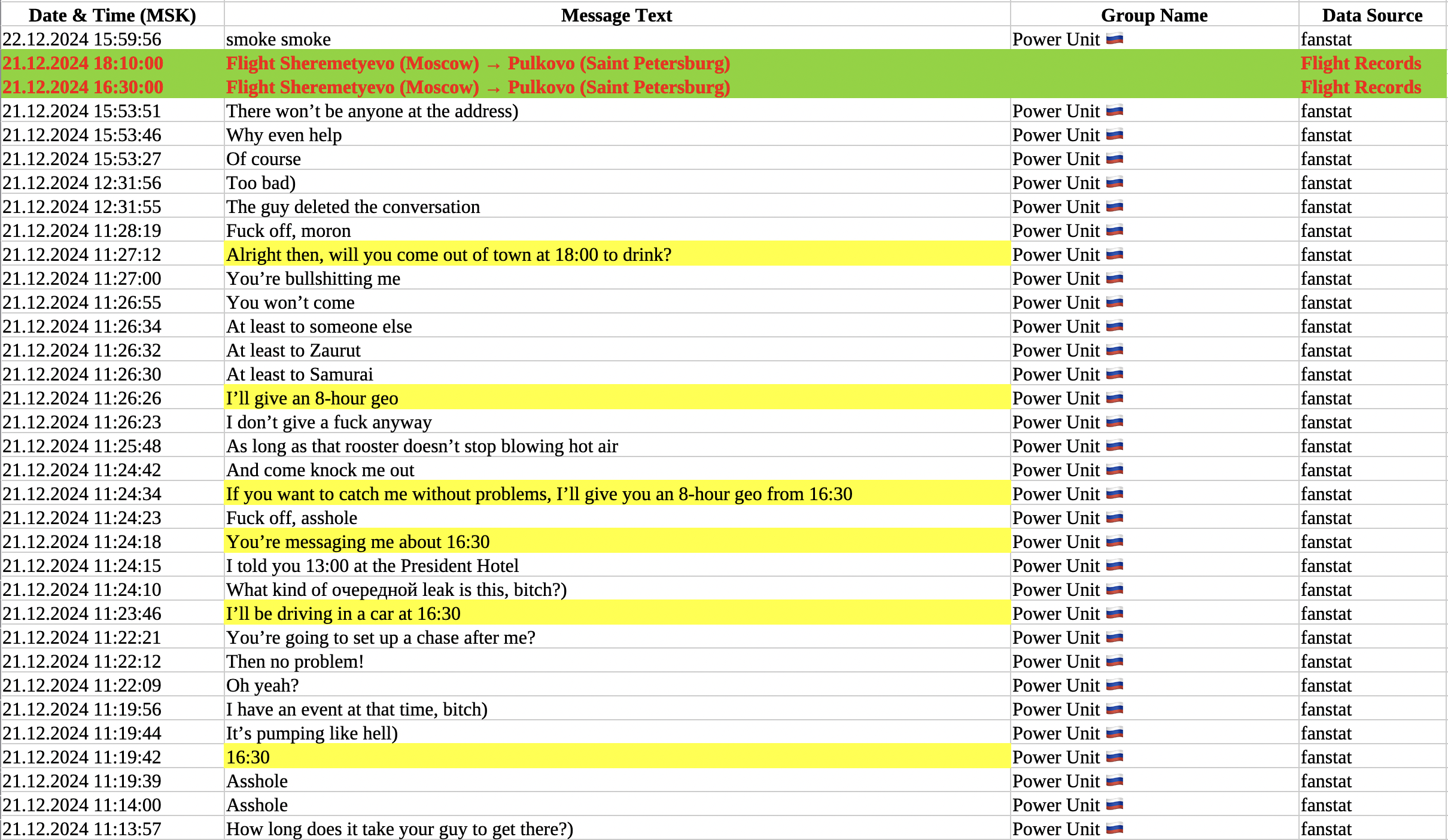
Here is another interesting episode related to NET-WORKER messages and Kurashov’s flight — pay attention to the messages highlighted in yellow, and the scheduled flight time.
(Translated from Russian. The original message text is provided in the Russian version of the article)
And I found several more similar examples after adding flight information to the messages table and highlighting them in color. This method made it easy to find previously invisible OPSEC mistakes.
Why this “finishes off” the de-anonymization?
These two onboard communication cases — out of 30+ flights — and both are explained by the presence of Wi-Fi on international flights (unlike domestic Russian ones with no internet). The message context is not neutral — it directly refers to the flight situation: stewardesses, takeoff, plane hijacking jokes. Add all the conclusions from the first part of the article. These are not random coincidences — this is a behavioral profile where metadata + minimal context of anomalies leave zero room for doubt: NET-WORKER is Aleksey Kurashov.
In the end, even attempts to find a “second person” lead to the opposite: everything points to one person, with his rhythm of life, habits, and environment. De-anonymization complete.
These two onboard communication cases — out of 30+ flights — and both are explained by the presence of Wi-Fi on international flights (unlike domestic Russian ones with no internet). The message context is not neutral — it directly refers to the flight situation: stewardesses, takeoff, plane hijacking jokes. Add all the conclusions from the first part of the article. These are not random coincidences — this is a behavioral profile where metadata + minimal context of anomalies leave zero room for doubt: NET-WORKER is Aleksey Kurashov.
In the end, even attempts to find a “second person” lead to the opposite: everything points to one person, with his rhythm of life, habits, and environment. De-anonymization complete.
Final conclusion:
I conducted this work to demonstrate how even the most cunning hackers hide, and to show the tools, methods, and techniques by which they can be de-anonymized. In my next publications, I will show several related exposés based on similar sources of information, and I will also reveal the real identity of the leader of the LockBit group.
Additional information for researchers (unedited, drafts)
