Ping Pong Pizza Porn: Did Comet Host Illegal Images?
By Bernie Najarian
In the year following the election that raised Donald Trump to the highest office in the land, and then to the lowest poll ratings ever for the office, most people have forgotten about some of the more colorful features of the election. One exotic flash-in-the-pan that left little impression on the popular consciousness was a conspiracy idea that connected a hipster pizza restaurant in Washington, DC, with the notion that opposition candidate Hillary Clinton and her co-campaigners, who sometimes had fundraisers at the restaurant, were key figures in a massive ‘pedophile ring.’ This cabal was supposed to be shipping babies and other children to be sexually abused and, in some stories, cannibalized by many of the powerful figures of the Western world – especially Clinton supporters.
I’ve written two detailed articles on this “Pizzagate” or “Pedogate” conspiracy theory (https://justpaste.it/18t8f, https://justpaste.it/19845) looking into all its major themes and showing the underlying realities that they were most probably based on.
Pizzagaters believed in three main threads of pseudo-evidence against Clinton and her campaign manager John Podesta.
One thread can be termed ‘icky art:’ Pizzagaters were impressed that Podesta’s brother Tony, head of the lobbying firm Podesta Group, collected feminist-influenced artists who emphasized the sometimes-grim realities of women’s lives; for example, he owned a Louise Bourgeois sculpture depicting extreme “hysteria,” and a Biljana Ɖurđevic painting showing young girls who had become casualties of the Yugoslav civil war. Ɖurđevic, if googled online, could be seen to have publicly exhibited a number of hyperrealist works depicting children being punished; these were part of a series on wartime atrocities that also featured, for example, scenes of soldiers with snarling dogs. These morbid works, to the alt-right American Christian ‘gun-damentalists’ predominating in the Pizzagate cult, conjured up a pre-conceived ‘satanic pedophile’ concept inherited from the debunked ‘satanic ritual abuse’ witch-hunts of the 1990’s (https://en.wikipedia.org/wiki/Satanic_ritual_abuse). Especially after Tony Podesta was found to socialize with Marina Abramovic, a New York-based Serbian performance artist who was mining the ‘wimmin’s magick’ branch of feminist art – featuring blood and ad-hoc rituals – the Pizzagaters began to assert that Satan was literally being summoned in Democratic Party fundraising.
The second thread of Pizzagate evidence was ‘puzzling emails,’ in which tediously routine emails from Clinton, Podesta and others, posted on the Wikileaks website, were interpreted via an ad hoc code in which every reference to food was taken to refer to child sex abuse – pizza for girls, hot dogs for boys, and so on. The code was made up by 4channers and redditors on Nov. 3, 2016, when part 28 of the Podesta emails was released by Wikileaks (see https://justpaste.it/19845 for details), but was mischievously misattributed to FBI information and rooted in credibility by referencing the long-standing use, largely specific to the 4chan website itself, of the phrase ‘cheese pizza’ as a same-initials euphemism for ‘child pornography.’
The third Pizzagate thread of pseudo-evidence was the Instagram account of James Alefantis, owner of the pizzeria/ping pong parlor Comet Ping Pong in Washington. Alefantis’s main crimes in the alt-right world were listed by redditor DumbScribblyUnctious early in the Pizzagate campaign, starting from around Nov. 4, 2016.
<blockquote>
Comet Pizza is a pizza place owned by James Alefantis, who is the former gay boyfriend of David Brock, the CEO of Correct the Record (a super-PAC funding body supporting the Hillary Clinton election campaign). It has been the venue for dozens of events for the Hillary campaign staff. John Podesta has had campaign fundraisers there for both Barack Obama and Hillary Clinton. John's brother and business partner Tony Podesta has his birthday party there every year.
</blockquote>
Examination of Alefantis’ ‘jimmycomet’ Instagram account revealed that he had done like many young gay urbanites and taken on the designation of godfather for the daughter of a couple of close heterosexual friends; this secondary parenting had resulted in many playful photos on the Instagram. One in particular where the god-daughter’s older sister had lightly taped her smiling sister’s wrists onto a ping pong table with adhesive tape was widely seized upon by Pizzagaters as an ominous suggestion that children were being tortured at the pizza parlor in preparation for grimmer satanic useages. Again, I’ve already discussed and analysed, in the articles I’ve mentioned (https://justpaste.it/18t8f, https://justpaste.it/19845), many of the images most commonly used by Pizzagaters as satanic evidence.
(I receive no payment for clicks on these articles in a commonly used, safe ‘paste’ website, where the simple format tends to prevent attachment of malware and where posters like me cannot track viewers by viewing incoming IP addresses. All my work on this topic is pro bono.)
Over the months following the election, many Pizzagate tropes have been debunked, and several attempts to fabricate more incriminating evidence have been exposed. True believers have begun to sense that the credibility of their ‘red-pilled’ ideas has fallen off even among those most inclined to believe that liberal politicians are appeasing Satan in private. For a few months in the summer, anonymous posters – perhaps professional Russian disinformationists, or perhaps inventive tabletop ‘researchers’ excited to put out new ideas – came out with a series of stories suggesting portentously that massive pedophile rings in Hollywood were about to be connected with Pizzagate – the annoying arts power of the liberals would soon be implicated along with the satanistic political powers. Fake news stories appeared, on the news-like fiction sites yournewswire.com and neonnettle.com, featuring people like Justin Bieber talking about their intimate knowledge of pedophilic conspiracy machinations in the entertainment industry. Debunks soon appeared, but by then the next fake news stories were trending. Meanwhile, the bulging-eyed wacko far-right YouTuber and nutritional supplement salesman Alex Jones talked of busloads of kidnapped children being regularly shipped to Los Angeles parties so that entertainment A-listers could rape them, have their tiny heads sawn open and then run their fingers sensually through the brains until the children were removed for dissolution in acid (as documented in https://justpaste.it/18t8f). None of these inventions and soothsayings did much to add to the Pizzagate credibility ledger.
The sudden mass exposure of Hollywood producer Harvey Weinstein as a thuggy casting-coucher was trumpeted at high volume for a few days by many Pizzagaters. Here was the proof that they had been right about those Hollywood satanic pedo rings – except that the fact that Weinstein and several other penis-wavers were heterosexuals who preferred to pester adults was a serious weakness. Pizzagate couldn’t be supported by exposing a monstrous heterosexual ring. Even though most of the mashers and opportunists were not above bothering an older teenager if they could get away with it, they clearly weren’t pedophiles. When Kevin Spacey emerged as a homosexual masher who’d used his position, in his younger years, to bother some younger teenagers, it turned out that he had already been well documented by paparazzi photos showing him making out with adults, and was decades removed from any perceptible trace of orientation towards minors.
Corey Feldman became the great hope to expose the rumored Hollywood pedos, but when he posted a go-fund-me page asking for over a million dollars to do it as a film, he became a relatively distant hope. Eventually, when he named two abusers free of charge, one, John Grissom, had previously been well described and fitted with a pseudonym very similar to his real name in Feldman’s autobiography, and the other, child talent manager Marty Weiss, had been convicted years ago of sexual crimes with children and had already been heavily publicized in Amy Berg's 2014 documentary An Open Secret. Grissom hadn’t worked in movies since the time of his unprosecuted alleged offenses with Feldman, and had long since taken the precaution of moving to Mexico. Feldman’s most dramatic contribution to the discussion was to annihilate some long-treasured cover-up theories by stating categorically that Michael Jackson had NOT been an abuser.
Just as I was in the process of researching this article, Feldman named a third alleged abuser, former youth club owner Alphy Hoffman. This was progress, clearly, but even this previously unmentioned bad-toucher didn’t seem to conspiratorially connect in a way that would account for Feldman’s oft-stated fears of being killed in retaliation for his revelations. Sympathetic onlookers, including me, can only encourage him to make a naming-names movie about his harrowing times, but it’s never been clear how doing so would deal with his stated fears. Some indication that he truly had a big, Weinstein-sized fish on the line, plus a plan for reeling it in, would help to dispel the gnat-swarm of question marks hovering over his often-dire statements and quest for big money.
Certainly, so far, he hasn’t appeared to offer anything to match the lurid online stories of busloads of children going to their brain-swishing deaths at fancy Hollywood homes.
In reading the Pizzagate-related hashtag threads throughout this time, I developed the whimsical notion that someone in an office building, somewhere, was giving out prizes for ‘best new Pizzagate story of the day, no matter how improbable.’ Previously unseen usernames appeared in abundance, avidly touting unlikely tales like ‘Taylor Swift’s new video proves she’s involved in satanic pedophilia.’ The pattern of new hot conspira-scandals made me muse about which industrious rumorsmith had won that day’s 25-rouble gift card to Starbucks Moscow. Many of the themes would disappear after a few days, only to appear with new frills of scandalous embroidery later on. Rumors ping ponged back and forth between Twitter and a smattering of highly anonymized posters active in the wild dark of the 4chan website’s ‘/pol/ - Politically Incorrect’ subforum. Lunatics who claimed to be insiders in various police services and government departments predominated there, and mostly issued cryptic portents that were rendered meaningless by the slightest trace of critical thinking.
One day, however, there was something quite different in the mix: a bona fide, openly named American from Houston TX, Dean Fougere, usernamed ‘Titus Frost,’ posting a YouTube interview with an anonymous American “hacker” who claimed to have found links to a major child pornography network in a hidden section of James Alefantis’ cometpingpong.com website. The interview was over an hour long, an interval that requires serious commitment to listen to, but I and a couple of colleagues decided it was worth taking the trouble and making notes. If based in reality, it would be a serious accusation, unlike squeamishness about art, silly made-up food codes and Grundy-paranoiac interpretations of whimsical kid photos.
Dean Fougere (Titus Frost) and fiancee Jasmine
A partial transcript of the interview follows – approximately the first nine minutes. I was mainly listening for the actual evidence that there was some reality to the accusation, as were many people connected on a typed-comments live chat that was done while the interview was being recorded. As you can see, we came up quite short in that department.
<blockquote>
[deleted] www.youtube.com/watch?v=HTRewHDOr90 Nov. 3, 2017
Guest (‘the hacker’ BigFish): … It all started last November when the Podesta emails came out … Me and my crew, some of the people that I work with were researching the Podesta emails when they came out and um, we found the section on Comet Pizza that had a download section with (“bzuh” [inarticulate]†) files and we ended up getting into those files and ah, found that they contained child pornography, ah, so, ah, instead of going out on the internet, which you can’t really DO, you can’t really take that information out on the internet and display the evidence to everybody, you know, as much as you would like to, you know, say ‘hey, this is what they’re doing,’ but, ah, so, you know our thought was ‘let’s take it to the proper authorities,’ so, in late November, we did.
We took it to the authorities, the DC Metropolitan Police Department, and ah, when I first called, they kinda gave me the run-around and just kind of, uh, pushed my call around, like they would transfer me to another person, make me tell the whole story and they would transfer me to another person, until they basically tired me out to where I didn’t want to tell the story any more. *clears throat* …So then I told them the whole story, and I was pretty upset by the reaction that I got from the DC MPD – um, they seemed like they really didn’t want to hear about it, ah, and like I say, they kinda just gave me the run-around and that was late November.
† (BN: My Twitter-based colleague Kamil Beylant tweeted the interviewee, @trebillion, to ask what he had said here, but received no answer. The account was active at the time.)
So – I thought the next step might be to contact the FBI because I didn’t ...I knew… I knew a little bit about the corruption in the FBI but that was the only step I had, I mean I didn’t really know who else I could contact, and so I contacted the FBI and, um, I told them the whole story and, uh, they took notes and whatnot, but didn’t really say anything about it, and so I got off the phone with them, and again this was in late November, and uh … so I waited a little while, and December 4, we came upon Dec. 4, and on Dec. 4th was the day that Edgar Maddison Welch went down to Comet Pizza, supposedly with an assault rifle, um, and so when that news broke on the 4th , I knew right away that it was a false flag to cover up for the evidence that I’d given to the DC police department, I mean, I knew right away, like, right when it was happening…
So, the following day was the 5th, Dec. 5, and ah, right when I woke up in the morning, I called the DC MPD again. This time I got a whole different reaction from the DC MPD; they put me directly through to a detective named Marcus Stevens† … so when they put me through to Detective Stevens, he was REALLY interested in what I had to say… he listened, and ah, asked me if I would send the information over to him through email, and so that’s what I did on Dec. 5th – I sent him the information through email. When I talked to him on the phone, I said, uh, you know, Marcus, there’s a lot of hearsay out there and there’s a lot of speculation and there’s a lot of evidence that isn’t actionable but this IS actionable evidence and I said, you need to go down there and you need to ask James what this is and if he doesn’t tell you what it is, you need to ask him for what the passwords are and if he doesn’t ask you for the password – uh, if he doesn’t give you the password, then he’s hiding something from you. I said, “This IS actionable evidence.” And he agreed. He seemed like a really nice guy when I talked to him on the phone. And so, I sent him the email and then that night I thought about, you know, that I didn’t send any kind of confirmation on the email to confirm that he received it … that I confirmed that he received the email. But I also wanted to let him know that if he needed help getting into that section, if he needed help getting back to that part, if he needed any help at all, that I’d be happy to help. And so, I sent that email first before I actually sent the confirmation email. I sent him another email after that asking if he could confirm receipt of the evidence I had provided and, um, the next day I got an email back from him saying that he had received the email, so I said thank you, God bless, I appreciate it, you know, I don’t remember exactly what I said, that’s what I said to him. So, for the next two weeks, I was in contact with them, and I was sending emails, different stuff, um, because this wasn’t just that website, it was connected to nine different servers all across the globe, this is a huge network, this was a huge network
† (BN: Confirmed as the name of an actual person on the Vice Squad of DC MPD)
So, back to the Edgar Maddison Welch shooting on the 4th, when Edgar Maddison Welch went in there, they tried to say that he shot through a lock and into the computer’s hard drive, you just so happened that the magic bullet happened to go through the lock into the hard drive.
Fougere (under pseudonym Titus Frost): Yuh, and that story itself has been confirmed by James Alefantis himself who wrote in the Washington Post that that’s what happened, so that they’ve admitted that’s their version of the story.
</blockquote>
At this point in the interview, the interviewee diverged into seemingly ominous and threatening events that had occurred in his life after he had made these police reports. We’ll come back to those shortly. First, though, I’ll quote some pieces of later discussion that referred back to the processes of collecting and reporting evidence. These fragments bear occasional time stamps for easy retrieval in the YouTube. The interviewee’s set of assertions doesn’t amount to a particularly complicated story, but the credibility of that story depends entirely on whether we can really believe anything of legal interest was found. His testimony on that matter, so far, consists entirely of “we found the section on Comet Pizza that had a download section with ‘bzuh’ files and we ended up getting into those files and found that they contained child pornography.” This is all about a website that is extensively archived in the ‘wayback’ web archive project, and no trace of a link to a ‘download’ section, or even an unexplained link of any kind, is to be seen there. Everything archived is about food and entertainment events. Alternate possibilities for the sort of link the interviewee might have seen are discussed below.
<blockquote>
23:29 They (DC MPD) took notes on everything I said. Another key point is, as soon as I reported it, like, ah, either the first time or the second time, they (Comet – BN) took down the page, I think it was right after the first time, they took the page that you could actually enter the log-in keys on, so they took that page down, and after the second time, ah, a little while later, they actually redid the whole website, ripped down the whole site, and they did the false-flag with Edgar Maddison Welch… so after all this had occurred and after I’d contacted all these people… (contacted media including Fox 5) but after what happened to Ben Swann†, they can’t report on it.
</blockquote>
†Ben Swann was a presenter for the Russian-operated RT America news network who moved in Jun 2015 to being lead evening news anchor for CBS affiliate WGCL-TV in Atlanta, Georgia. He often dabbled in conspiracy theories in his independent program, ‘Reality Check,’ and, among other things, had speculated that the Sandy Hook mass school shooting involved two shooters, not just the disturbed Adam Lanza who was ascertained by law enforcement as the culprit. On Jan. 17, 2017, he produced a ‘Reality Check’ episode suggesting that earlier news reports dismissing Pizzagate as a fake news story had missed some tantalizing indications, and that further investigation on the veracity of the ideas should be carried out. This was widely seen as unwarranted further harassment of the people falsely accused of sexual crimes by the original Pizzagate outburst. The resulting uproar led to Swann’s removal from his prominent role by the WGCL; he closed his highly populated social media accounts and was reduced to doing local news stories (http://www.cbs46.com/story/35977779/cbs46-partners-with-atlanta-barbershop-through-books-to-kids-program). Pizzagate aficionados interpreted this bad-judgment slap as suppression by the conspiring ‘deep state.’
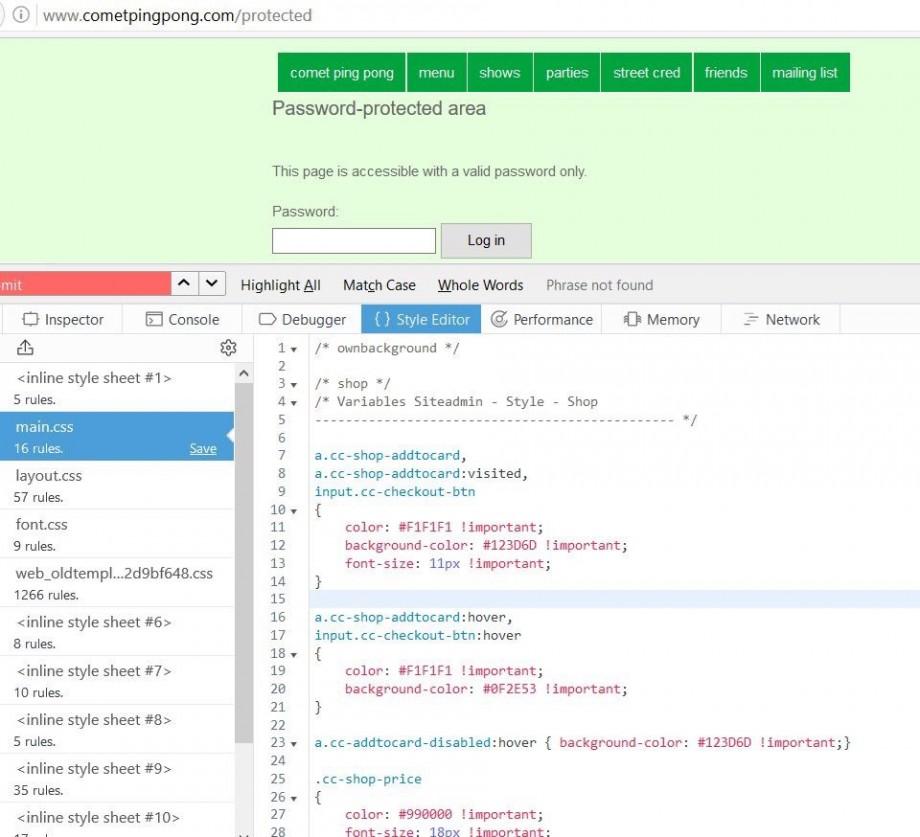
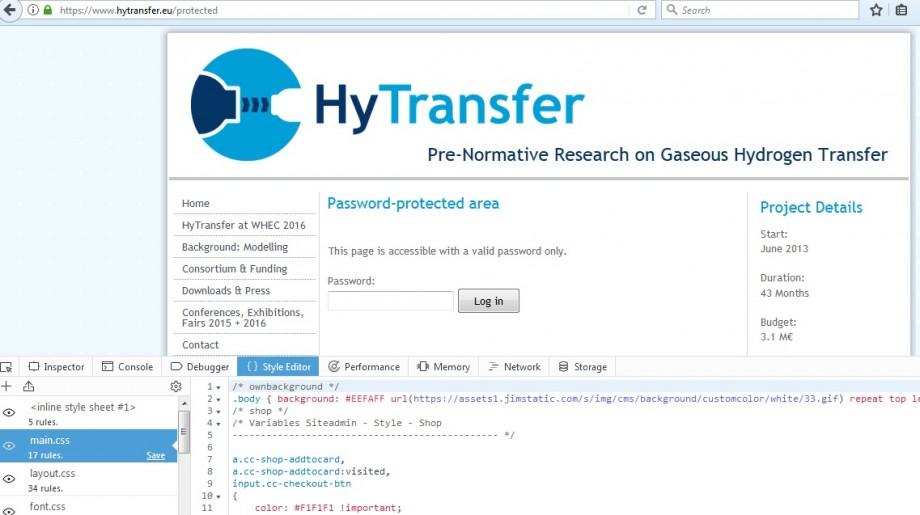
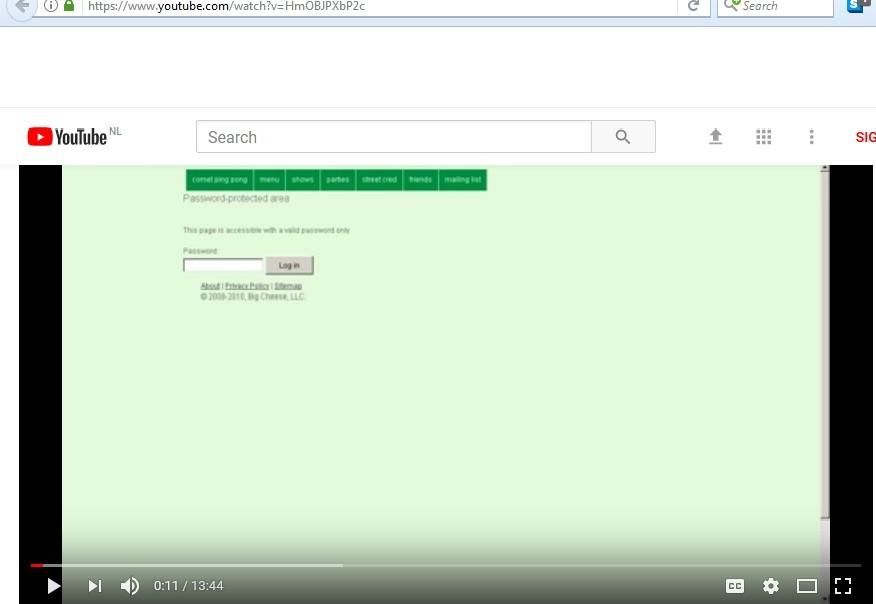
What had actually happened to the Comet website (cometpingpong.com) was that, around the time Pizzagaters began to pick at it for scandal fodder, the managers of the website changed it from a relatively simple do-it-yourself commercial website software system, Jimdo, to a somewhat more upscale one, Squarespace. The likely non-criminal explanation for such a move was only made plain in February, 2017, after Dean Fougere published an initial YouTube ( //www.youtube.com/watch?v=TnW7OT6Dkuw – Feb. 12) outlining the evidence that hidden areas had been found on Comet’s website. These allegations were bitingly criticized shortly afterward by an online Youtuber from Portland, OR, who had clearly worked as a computer professional – WAPTEK,’ said to be William A. Price by real name. He published a blistering YouTube retort to Fougere on Feb. 22, 2017 ([deleted] www.youtube.com/watch?v=HmOBJPXbP2c), pointing out that all websites in Jimdo software came with a ‘protected’ link for administrative use. Experienced admins, he said, tended to change the default name “yoursitename.com/protected” to something less obvious to conceal it from ambitious hackers; Comet had not done so. I’ll get into more detail below about the Jimdo system and its entanglement in the scandal allegations. Squarespace, in any case, had an alternate administration system that didn’t feature a readily found private admin link. It had nothing that onlookers could speculate about as hidden content.
Now, back to the interview.
<blockquote>
25:46. BigFish: OK so there was a few different aspects to the website, it was connected to other servers, so … there was, like, there was a server in Berlin, Germany, there was servers all across the world, and basically it was just, I don’t know if it was a site where they were actually sharing child porn that they had committed themselves or if they were just, if it were just a place where you could easily get it, but then also, there was a few other things on the back end of the website, like there was a shopping cart, and, uh, different things that you could see on the back end of the website, also... zip files, images, movies, there were things they were selling, I couldn’t see what they were selling [a key admission – BN], but they were selling things …
[Re: “shopping cart.” A screenshot circulating on the web showed a half-page view of the Comet passworded admin page at cometpingpong.com/protected with underlying cascading style sheets, as viewed in Firefox’s Development Tools Inspector. This view revealed some code supporting a possible credit card-using shop, apparently present as a Jimdo template that could be used or not used. Following a suggestion from WAPTEK, I confirmed that the exact same code is present in the protected admin page of another Jimdo website at hytransfer.eu/protected. This is a non-commercial site. More on related matters below – BN]
BigFish (cont.): The problem is the DC police are corrupt, the FBI are corrupt, the DOJ (Department of Justice – BN) is corrupt … you could literally have a movie of them raping kids and they’re not going to do anything about it … The DC police have the info, the FBI…
31:00 – Fougere: For obvious reasons, you couldn’t download the information onto your computer because that makes you guilty of a crime, and anyone who’s reported child porn knows that the only thing you can do with it is bring it straight to the police, you call them and you tell them where it is, and then they have to investigate it.
BigFish: Yeah that’s all I could do, and then just document the fact that he had … confirm with him that he had received the information that I gave him and I did that.
… Ask Peter Newsham yourself. (Washington DC police chief – BN)
… If you look into the past of Peter Newsham, it’s not exactly … uh, well, let’s just say it’s a checkered past, um, he covered up the rape of an 11-year-old, by, you know, three or four different men; he beat his wife and knocked her teeth out; he was found drunk on the street, you know, and someone took his service revolver right out of his, right out of his holster, so um, Peter Newsham’s not very clean. He was also, um, in charge of ethics with the DC MPD when Seth Rich [mysteriously murdered Washington man touted by Pizzagaters as an alternate, non-Russian source leaking the Podesta mails to Wikileaks] was murdered, uh, under Cathy Lanier, and magically he was promoted to – Chief. So, um, I don’t know if it’s him that’s covering it up, or if it’s the FBI or what.
42:02 – (re: the alleged Comet child porn site) it’s connected to other servers
… what I think is they’ve just been getting away with it for so long that they just got, they got lazy, they got complacent, they think they’re above the law so it doesn’t really matter, you know, so it was just right out there in the open, and I think a lot of their clientele is, um, you know, people from different embassies, different nations, a lot of times, and so it had to be something easy, you know, almost like if you were staying at a hotel room and you wanted to watch porn on the TV in your in your hotel room, you know, it would be that easy to download it, you could just click on a button, you know, you don’t have to explain to ‘em, oh go to the dark web, go do this, go do that,’ it’s just like ‘here’s a code, you can enter this,’ you know, type of deal. Either that or it was something like: they shared acts that they were performing, like they’d perform an act and they would put it up there for other people in the club to watch, kind of like a forum, but, um, you know, when you see money – money transactions and a shopping cart it’s like, it would seem more to me like something where you’re selling it to people from other nations, you know, that aren’t very technical, that don’t know how to get on the dark web and do anything like that... Or it could be, you know, like a lot of people have speculated that James works for the CIA because his house is out there in McLean, right by the pig farm and so, I don’t know, it could be a CIA Op where they’re trapping people with that stuff, like, they give people a code and they log in there and then they’ve got ‘em. (people they want to blackmail – BN) … you go back in history and the CIA’s always been involved in child trafficking … from my research it seems like he’s involved with the CIA in some way…
</blockquote>
Eventually, questions from the online audience were taken, and most of them were about the reliability of evidence. Some of the questioners clearly spoke sysadmin lingo, and want to elicit some real tech talk from BigFish. They didn’t get answers back in their own argot, just more of the same we’ve already seen.
<blockquote>
Online questioner: “If you were on the back end and you wanted evidence without (downloading) child porn, would you not scrape the source code?”
BigFish: There was a lot of evidence that was provided like I say … just not the actual, you know, direct child porn, not like sent (? [inarticulate]) movies, there was a lot of evidence provided to the police, more than enough evidence to be actionable, there was a lot more than that that was provided to ‘em, and also I told them exactly what to go asking and what to do if they needed help…
With what I sent them, the metadata and everything, they should have been able to easily go through it and track everybody down who ever used the systems. I even gave them the servers and a lot of other information, too.
… when I first called the DC Police … when they answered the phone they knew my name …
What you do is you call the police, you show them where it is on the phone, and then the police are supposed to investigate it, that’s how it works.
</blockquote>
Fougere then took his audience to task for being so dubious about his guest’s lack of demonstration that porn was really present.
<blockquote>
Fougere: For the evidence, what do you guys thinking I was going to do tonight, like play child porn in this video for you all? What exactly were you guys hoping to see? This is the hacker, this is the truth, this is the story.
BigFish: I told you who to call (Washington police – BN) and who to ask to verify it.
</blockquote>
Fougere had mentioned that people in the DC MPD hadn’t been responding to his queries lately, so the usefulness of this verification technique wasn’t self-evident.
Other questioners also received frustrating answers.
<blockquote>
Fougere: So ‘epiczee’ [a username, rendered as heard – BN] says “Comet Ping Pong is powered by Squarespace, do you know anything about that?”
BigFish: I don’t want to go exactly into all the technical of the website, but, um… (long hesitation)
Fougere: Yeah, I’m not going to ask you to tell them how you got in there, that would be obviously not a good idea to broadcast live over the internet (laughs)
</blockquote>
BigFish’s failure to correct the questioner about the website’s current and previous software is mysterious. His evasion could be taken as an attempt to mask ignorance by pretending to find something dangerous in the answer – but after prominent criticisms by WAPTEK, how could BigFish not know that the software at the time was Jimdo rather than Squarespace, and how could he pretend that releasing this information was hazardous? Perhaps he simply found it convenient to avoid all penetrating queries about website components by finding an excuse to brush off the whole topic.
The general perception of threat that is summoned up here becomes ever stronger as the interview draws near its end.
<blockquote>
… whoever was sent to my house, either was hacking into my phone or they were sent here by law enforcement, because those were only people who knew who I was or that I had ever provided this information, so, yeah, they track you and they know exactly what you’re doing at all times, everybody knows that, so, that’s nothing really…
I’m not from DC so I didn’t know how corrupt the police were there … same with FBI, I knew Comey was corrupt … but I figured if you called a regular FBI agent, they’re going to do something if you reported a crime…
</blockquote>
It was interesting that BigFish didn’t make any effort to respond to the specific critique of his assertions by the website admin WAPTEK. These objections had been out there for over eight months at the time of his interview. I’m going to let WAPTEK give them to you in his own words. To save you listening to a longish YouTube, at least for now, here’s a transcript of the bits that are most pertinent. WAPTEK’s tone is often sarcastic, so beware of back-handed irony in some statements.
<blockquote>
[deleted]//www.youtube.com/watch?v=HmOBJPXbP2c (Feb. 22, 2017)
Here we go again with amateur night. This is ‘cometpingpong.com/protected.’ (Shows the screenshot that has been repeatedly shown by Pizzagate accusers of Comet – BN). This page is accessible with a valid password ONLY. Password: (‘Password-colon’), notice the spelling and case. ‘Password-protected area.’ Gee, I wonder what would happen if we did the über-hacker thing of turning off the style sheet. (Shows screenshot of same page with style sheet formatting turned off – BN). Oh, look! Log-out and edit! Where’s the log-in? That’s the log-in. But, it’s not there, this way! They’re hiding it! … (makes scary face)
Why would a website have a password and log-in area?
OK? Well, let’s hit the style sheet thing again, you know, that über-hacker thing. Now let’s load our mouse over here, ignore ‘Big Cheese Pizza’ (Comet’s corporate name – BN) … focus please … when you hover over ‘logout,’ it posts (at lower left corner of screen – BN) ‘e.jimdo.com/cms/app/logout.php’ – CMS is ‘content management system,’ by jimdo.com, for the logout button, and there’s the edit for jimdo.com/app/auth(orization)/signin/jump(to)cms= page, and then it has the PAGE number, which it shouldn’t be showing us, but there it is. It shows you what page number to jump to after the password’s been logged in so that you can edit the website.
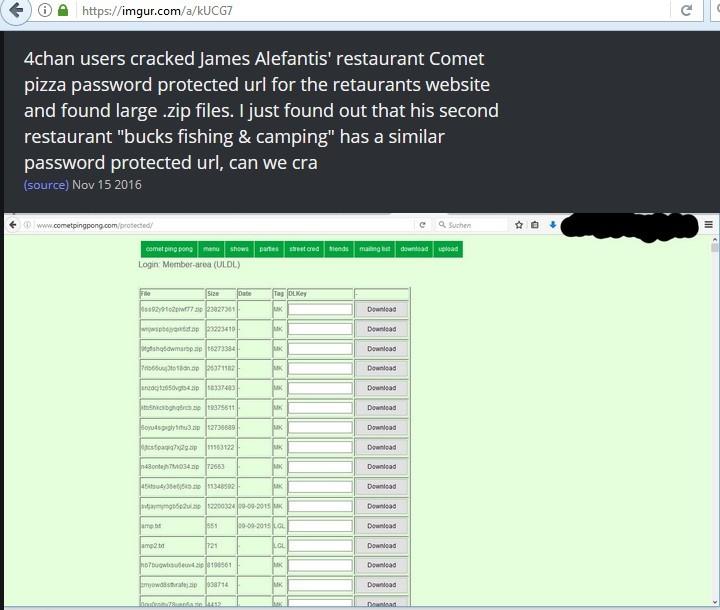
This is the content management system, otherwise known as the website editor…. this is like that guy who found that secret, über-secret storage area on the net with files on it, you know, because that’s what this is about (referring to Upload/Download screenshot - see below). So, someone claims they got in here with a password. I don’t know whether that happened or not because just like everything else on this subject, no one will corroborate anything. But thank you very much for the person who did the screenshot, so we can see the word ‘search’ (in the browser of the person who took the screenshot – BN) as ‘S-u-c-h-e-n’ so that you could see which language it was in (German – BN) [Examines files, points out that there are two small ones with file extensions in .txt and several larger ones with randomized-looking names made mostly up of letters, plus a .zip extension; the latter are marked in the file chart with the classification ‘MK.’] So why does it have the tag MK? … The claim about this was that someone was able to download this stuff, using the password to get into the website, and then they used another password to download, right? … do you know the default behavior for this kind of content management system? Did you know you can have it email you the links to your website’s backup zip files? And have each one of them have their own download key?
[shows a series of other jimdo websites, such as hytransfer.eu, with the same protected page and log-in system as cometpingpong.com]
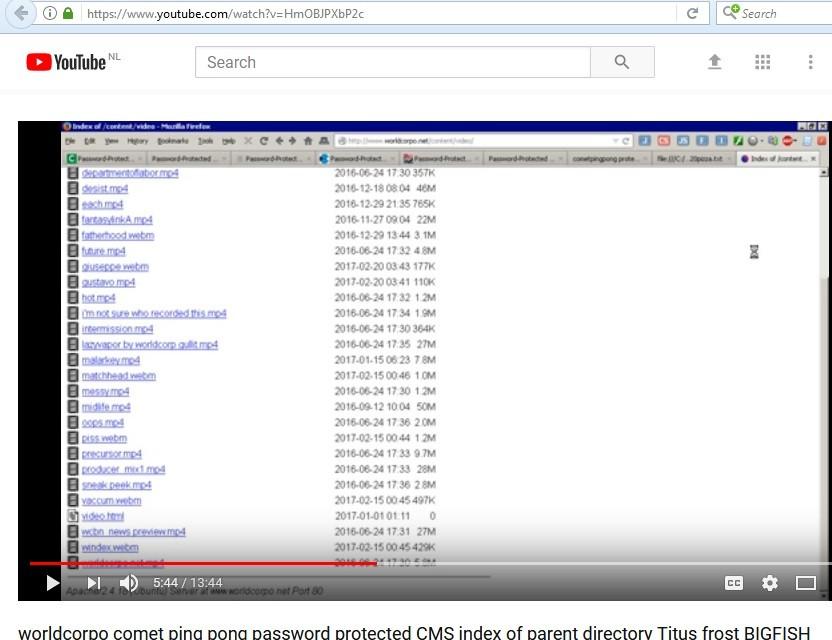
… Let’s go over now to ‘index of contents’ at worldcorpo.net [Since the Comet site had changed, Waptek used another loosely controlled website, worldcorpo.net, as an example. It has since been upgraded. At time of this video, Waptek was looking at an open admin link, worldcorpo.net/content/video – BN] … They’re just not making it impossible for you to grab their files, because there’s no point. Yes, there’s a bunch of files here (mostly mp4 videos – BN) … someone found it suspicious that if you click a file, like something that says mp4 or whatever, then it says ‘download’ (in the hover pop-up – BN) and it doesn’t play the video… that’s the default behavior of your computer, especially if it’s running Linux; it doesn’t know what to do with the file – it can download the file, or it can tell you some detail about it. It’s default behavior is to download it … not to play it, unless you’ve told it to do so.
You type in ‘parent directory’ (into a search engine – BN) and ‘index of’ and you’ll find literally millions of websites with an open parent directory
So, let’s go back here again to (cometpingpong): someone found a way to get into the log-in member area for ‘upload-download,’ that’s ‘ULDL,' for being able to upload and download raw zip files, but it’s mostly used for trying to download archives of your website, just like every other damn website in existence.
[WAPTEK surveys passworded log-in admin pages of several websites, and notes that there’s no log-in identification, just a password, because each site is built to assume the person logging in is the site’s admin]
… [talks about googling for various websites’ open ULDL member area] … and look for zip files with the tag MK … you’ll find out most of the time, these MK files are backup copies of the website’s archives, logs, whatever. I disable them on mine (Waptek’s website[s]) because I had to erase them every few weeks. This is what us geeks use when we run a website to find out who’s been visiting from what part of the world, just like YouTube does to figure out whether people are coming in from Korea, or Japan, to look at your videos … it’s the same damn thing… This isn’t hacking – it’s generic default behavior.
</blockquote>
After Fougere had published his long interview with BigFish, Waptek came out with a tech-savvy rebuttal on Nov. 19. It is excerpted below.
<blockquote>
[deleted] www.youtube.com/watch?v=TEAxZo4rUpc
I also pointed out in that video I made that what they were looking at was most likely the 11-20 MB worth of server logs or data traffic used for market research that you download. I also pointed out that in order to get in there, you’d have to have a password that would be the same password for making the website editable so you could change the website, and then each of the files required their own download key, which is basically a password, and that each of those files could be encrypted – that could be anywhere from 2 to 3 layers of encryption required for a hacker to break into a server that’s set up with a recent copy of proper encryption, and that that was not only unlikely but it was damn close to impossible, and that the supposed hacker, who’s now being called BigFish retroactively, has never explained how he did this, and has never addressed any criticism of this, nor has Titus Frost-ybutts, nor any of the other people. … Again, 11-22 MB consistent file sizes in zip format on a web server, right where you would expect to get the data downloads for backup copies of the server data backup copies of the website itself …
.. (why don’t you) prove the hacker got into the site by setting up another Jimdo page yourself and asking him to break in by doing the same damn (technique) … I did the same thing (WAPTEK set up test website http://waptek0.jimdo.com/ – BN) and nobody took up the damn offer.
If you want to prove this actually existed, all anyone needed to do at the time was one simple thing: you can feed the website, in the command line, the password to get into that page – it’ll take it. Jimdo doesn’t even make that secret; they have a page on how to do it – I included it in the video… it was included as one of the archives [linked below the video – BN. WAPTEK describes the procedure in detail at [deleted] www.youtube.com/watch?v=LJgHxZjB-cw, 14:45 ff, Dec. 1, 2017]. And then you can use that in the archive temporarily to archive the file set to make a screenshot of it. That would’ve been trivial. Or the person could have just said, yeah, the password was this, just wait until they change it so it isn’t valid any more … because that would then be listed as a password that would have worked for a previous hash – look up how passwords are hashed. … he could have archived just the ‘get in to look at it.’
</blockquote>
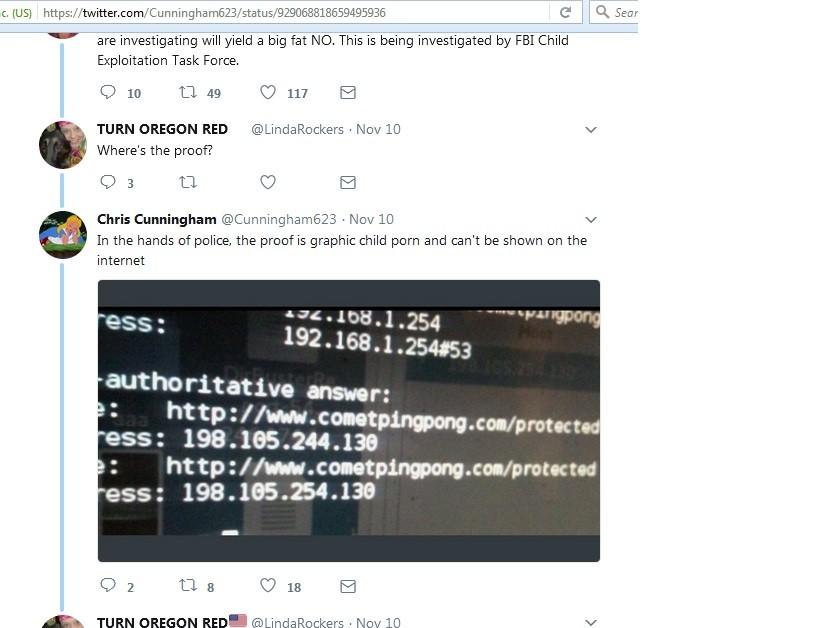
This leaves a few allegations in the Bigfish interview unaddressed, and the reason for this is that WAPTEK had already dealt with them in yet another reply, this time to a now-vanished YouTube posted by a user called Sye Phan (@phan_sye on Twitter), who had later deleted all his content. He had been caught fabricating several items, including a fake menu of commercially available sexual assaults on child victims that he claimed he had found on Comet’s hidden site while he was hacking in. Once his fakes were exposed, he disappeared. Some of his allegations and screenshots, however, remained in circulation. Especially of interest to those continuing the allegations were screenshots that showed IP addresses of the supposed worldwide network of websites linked to Comet’s server (mentioned by BigFish, above). As WAPTEK points out, anyone bothering to identify these IP addresses in a look-up site finds that they belong to Amazon and a default search engine called Search Guide.
<blockquote>
[deleted]://www.youtube.com/watch?v=Gmn3OKo3TQ0 Feb. 24, 2017
Yet another Pizzagate hacker, here we go! Sye Phan, Twitter hacker. Screenshots! Him hacking, Comet Ping Pong and … Pizzeria hack, and if you just stop looking at the title and look up the numbers on the screen, which I did, you find out he was breaking into or ‘pinging’ and trace-routing Amazon and a website called Search Guide. So, this is the equivalent to claiming you’re hacking something by typing in the IP addresses and MAC addresses – which you can derive – of Google and Yahoo. None of that had anything to do with Comet Ping Pong. … 198.105.254.130 and 52. 30.181.190. IP addresses resolve to Search Guide and Amazon.com. … Why didn’t anybody archive all this? ... If any of the images posted as proof of a hacking is fake, all of them are fake! … it does not include corroboration, linkbacks, but the video images basically include someone basically running ping on Amazon.com … Again, this isn’t someone hacking the Pizzagate page that you think is Comet Ping Pong pizza. This is someone showing screenshots of him(self) messing with Amazon.com and a website called Search Guide.
Do you know why? Because Search Guide automatically comes up because your internet service provider channels you there, if you type in, by accident, anything. So, you might have typed in ‘Comet’s Ping Pong’ or ‘Comet Ping Pongs’ and it might have redirected it. … And why didn’t he just go ahead and look up Comet Ping Pong’s IP address and go for that? That’s the server, right? Pro tip! An IP address leading to a server, a computer, doesn’t mean you’re at that internet service provider’s internet page. It could serve a hundred other websites. That’s usually what’s done. You can have hundreds of websites on one server; you can have a hundred of servers be associated with one website. It’s a very fluid system. If you don’t know exactly what you’re doing, you can fool yourself into thinking you’re hacking, whereas really, you’re just messing with the search engine that pops up because you’ve typed the wrong IP address or hit the ‘dot’ twice.
</blockquote>
Here, BigFish’s statement that “there was, like, there was a server in Berlin, Germany” becomes especially poignant. To quote Wikipedia, “The Jimdo head office is in Hamburg, Germany. It also has an office located in Tokyo. (The German Wikipedia adds: ‘Ab 2011 unterhielt Jimdo auch ein Büro in San Francisco, das 2017 wieder geschlossen wurde.’ – A US office existed in San Francisco from 2011 to 2017). As of 2015, Jimdo's team consists of 200 people from 15 different countries… To increase speed performance for their worldwide user base, Jimdo maintains data centers in the US, Germany and Japan. As of March 2017, over 20 million websites have been created with Jimdo.” Either the ‘hackers’ were looking at international servers of Amazon and Search Guide, as shown in their screenshots, or, if we give them credit for skill not substantiated by their evidence, they may have been adept enough at pinging to detect that the Comet Ping Pong site was being hosted by Jimdo, with its speed enhanced by a dispersion of servers.
As WAPTEK and the online live questioners pointed out in the various YouTubes above, there was much evidence that BigFish and Sye Phan could have brought forward, if they’d had it, that didn’t involve re-posting pictures of child pornography. They could have documented their steps to show their procedures, and, especially after the website had been replaced, could have included passwords. They could have “scraped the source code.” They could even, being hackers, have created anonymous identities and broadcast the incriminating links and passwords so that hundreds of fellow-hackers could see everything for themselves, as the Anonymous movement routinely does with ghostbin and pastebin lists of actual child pornography sites they are collectively attacking. (Fougere claims to be an Anonymous member, albeit now de-anonymized). Heavily proxied Anonymous members have never been reticent to give links to child porn sites to their (in theory) fellow-attackers.
All that exists in the public domain to document the alleged ‘child pornography on the Comet Ping Pong site’ is the passworded admin page of the old Jimdo website (including its ‘turn off style sheet’ and ‘view page source’ views), plus the Upload-Download page with links for moderately large zip files labeled ‘MK’ (marketing) and small text files labeled ‘LGL’ (legal, presumably holding copyright statements for the website). In a recent YouTube posted by Fougere on Nov. 13, 2017 ([deleted] www.youtube.com/watch?v=KRyP8DrWlqw), BigFish virtually admits in a rambling query to DC Police lieutenant Daniel Godin that that’s all he sent in (admission is marked in double square brackets):
<blockquote>
I guess my frustration is, over a year ago, I turned in evidence of child pornography to detective Marcus Stevens and I was in contact with him for a good month and he was investigating it and then all of a sudden, he wouldn’t email me back, they wouldn’t let me talk with him every time I called down there, and so, I really don’t understand why nothing has been done because it was clear, actionable evidence and everything was given to him, uhhh, back, actually the first time I called was in late November and when I finally got to talk to Marcus was Dec. 5, 2016. And so, when I talked to Marcus on the phone, uhh, you know, I asked him, you know, you need to go down there and [[ask James why he has a heavily encrypted download and upload section on a Pizza place’s website. That’s totally out of the ordinary, there’s no reason to have a heavily encrypted, password-protected section on your website with giant zip files on it, you know, where you require the people to enter a key to access this info.]] And so, I told Marcus, this is what it is, I emailed him all the evidence… and ask him why he removed it from his website after people started investigating Comet Pizza on the internet… after this broke, about three days later, he pulled that part of his website down, so I told Marcus, go ask him why did you take that down?
</blockquote>
If BigFish had sent in actual evidence that child porn was being held in the zip files, available to diplomats with a key – as he so vividly describes the hypothetical situation in his interview with Fougere – he would not need to be sending the DC Police down to “ask James why he has a heavily encrypted download and upload section.”
The very perceptive WAPTEK also points out that in screenshots BigFish made of his list of emails to Marcus Stevens, the emails labeled ‘Screenshots Comet log-in’ and ‘Bucks Camping Login as well’ have the paper clip logo showing they contain appended files, whereas the email entitled ‘Comet Pizza secret zip files’ has no attachments. In fact, its entire content is a Dec. 6, 2016 message to marcus.stevens@dc.gov pointing back to the log-in screen: ‘Marcus. One more thing if you need help getting to the login screen from your computer give me a call and I can walk you through how to get back to it even though they tried to erase and hide it. Thanks again.”
It seems that, in BigFish’s mind, the zip files on the Upload-Download page ARE child pornography. Merely to look at the filesizes, in the context of this Podesta-linked pizza parlor, makes unseen images of exploited children pop into his mind. His child pornography derives from his own mental hovering algorithm and can’t be seen by less imaginative browsers. He has hopes, however, that the DC Police will make his dreams real by getting into the suspicious zip files. Especially when they know the files are somehow linked to servers all over the world.
Even though, then, the ‘Comet Ping Pong child pornography’ scandal seems to be an illusion pumped up with a lot of advertised aspirations, there are some continuing events that could be taken to suggest that there is more to the matter than meets the eye.
One of these is the threats made to BigFish at his home. Maybe he really turned in something that the criminal elites are worried about. Here are some brief excerpts from the Nov. 3, 2017 interview, with time stamps.
<blockquote>
12:7 [BigFish came home to his house in a usually crime-free zone in a quiet cul de sac in a wealthy neighborhood, Dec. 2016] “All of my mail was opened and it was still in my mailbox”
11:28 [A few days later] “I got home from work” [went to bed 9:30, son knocked on the door, said, dad, someone at the door] … “when the person saw me coming they took off running…. I looked off to the right and one of the work trucks was smashed, he T-boned it.”
16:45 [some days later, hears a noise] “I came out with my gun … police were pulling some guy with a black ski-mask on out of my bushes.”
</blockquote>
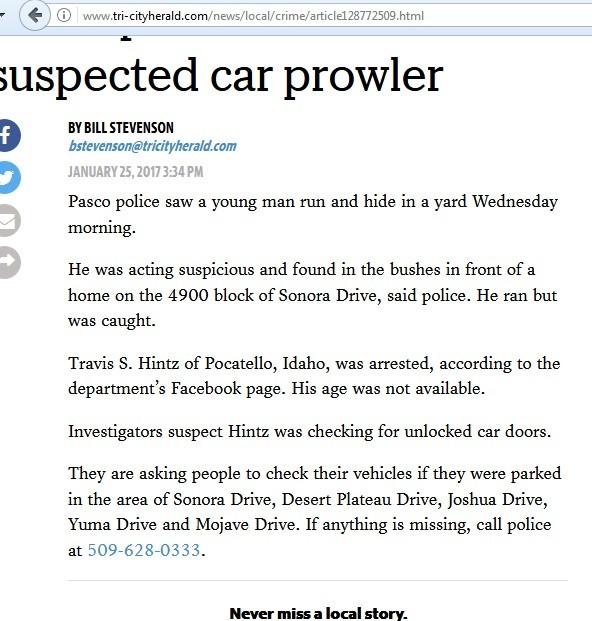
The incident is documented with photos of a white vehicle with a smashed front fender, and a newspaper story about the man who was found in the bushes.
The story, by crime reporter Bill Henderson of the Tri-City Herald (http://www.tri-cityherald.com/news/local/crime/article128772509.html), serving Pasco, Richland, and Kennewick, WA, says
<blockquote>
January 25, 2017 03:34 PM
Pasco police saw a young man run and hide in a yard Wednesday morning.
He was acting suspicious and found in the bushes in front of a home on the 4900 block of Sonora Drive, said police. He ran but was caught.
Travis S. Hintz of Pocatello, Idaho, was arrested, according to the department’s Facebook page. His age was not available.
Investigators suspect Hintz was checking for unlocked car doors.
</blockquote>
Fougere had said in his February 2017 YouTube that he didn’t want to disclose this story, since it might lead to the identification of BigFish, but by November, with credibility fading, he and BigFish evidently decided that improved documentation was needed to keep the Comet pornography story credible. In the interview, BigFish mentions how Hintz was apprehended hiding in a hedge of shrubs bordering his swimming pool. While discussing the earlier automobile smashing incident, he mentions running a business from his home. A look at Google maps of the 4900 block of Sonora Drive in Pasco discloses only one swimming pool with a hedge bordering it, and the address in question also happens to be the site of a home business – a driveway paving company, complete with suitable trucks. It’s, as predicted, at the end of a quiet cul-de-sac, a street called Mojave Court. That all seems to check out pretty well and tentatively identifies BigFish as Daniel Miner, a hard-working family guy who spreads himself over two jobs, neither of them obviously related to computers or websites. His Facebook lists liking for the New Resistance “conservative resistance” affinity group (https://www.facebook.com/conservativeresistance/), as well as the libertarian Freedom Works, associated with the Tea Party, the pro-Trump news site RightAlerts.com, Conservative News Today, Washington State for Donald Trump 2016, and the Mr. Conservative media website. Seems like a contender for a Pizzagate activist. A message from researcher Kamil Beylant to BigFish (@trebillion) on Twitter, asking if he confirmed or contended with this identification, went unanswered (tweets on other matters were responded to), as did queries to two parties claiming to know his identity.
Perhaps the reluctance of our ‘hacker’ to discuss technical website details comes from greater familiarity with paving driveways.
The mention of the eerie incidents was clearly thought by BigFish and his host to lend credibility to the idea that they were brave activists experiencing reprisals for their dangerous interference in elite business. If so, though, the release of abundant description of BigFish’s home, partnered with a news article specifying which city block it was on, suggests that the level of concern hasn’t remained very strong. Of course, since we’re in the world of conspiracy theories here, we have to mention that Dan Miner might be a ‘false flag’ pinpointed by Fougere and a still-mysterious BigFish as a well-chosen plausible stand-in. Since the present author is not much of a conspiracy theorist, he tends to think Miner is being accurately indicated. If not, Miner can ask to have the YouTube that descriptively pinpoints his house removed.
We’ll leave our hacker as BigFish for now.
BigFish also, in the list of eerie experiences given in his interview, mentioned that “when I first called the DC Police … when they answered the phone they knew my name.”
It’s not clear whether he had good reason to find this exceptional, or whether he was unfamiliar with caller display.
The final grasp for credibility that has been made on behalf of the Ping Pong pornography idea has consisted of ongoing assertions that the DC Police or the FBI are still looking into the matter.
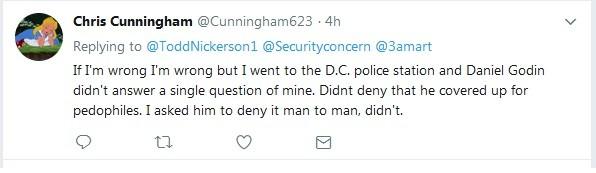
On Nov. 6, 2017, a 21-year-old Pizzagater named Chris Cunningham, conveniently situated in Berwyn, PA, decided to press the DC Police about whether or not they still had Comet’s alleged pornography on their docket. He wrote to the department’s current child porn specialist, Chanel Dickerson of the Youth and Family Services Division, linking BigFish’s interview video and asking for an update. Cunningham says, “This video reveals actionable evidence was given to the police in Nov., 2016. I am perplexed why it has taken a year to arrest anyone.”
Chris Cunningham
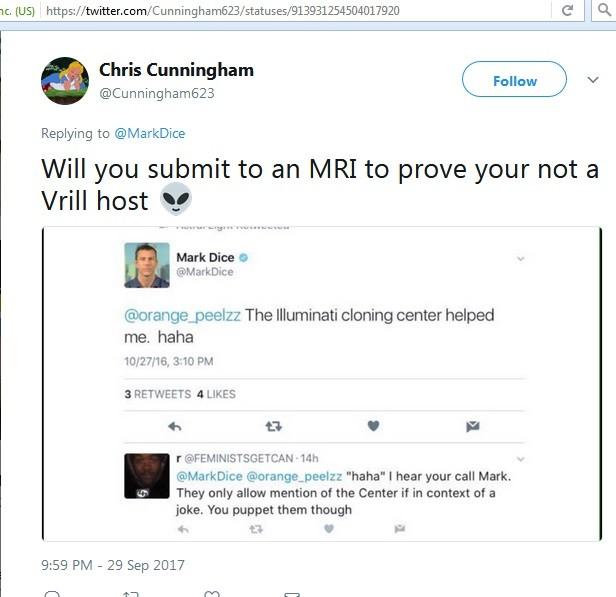
Cunningham doesn’t indicate that he has parroted the phrase ‘actionable evidence’ from BigFish. He himself seems not to have been highly trained in evidential standards. His Twitter shows that he enthusiastically believes that ‘the Illuminati’ are taking over the world via “human cloning centers,” “Vril lizards” (an idea derived from an 1871 sci-fi novel by Edward Bulwer-Lytton, usually titled ‘Vril, the Power of the Coming Race;’ it describes superior subterranean humans who are able to telepath information, get rid of pain, and put others to sleep using a fluidic energy called ‘vril’), “parasited (sic) hosts of vril (a.k.a. ‘drones’)” and “chipheads,” people who’ve been modified by the Illuminati to have hidden control chips manipulating their brains.
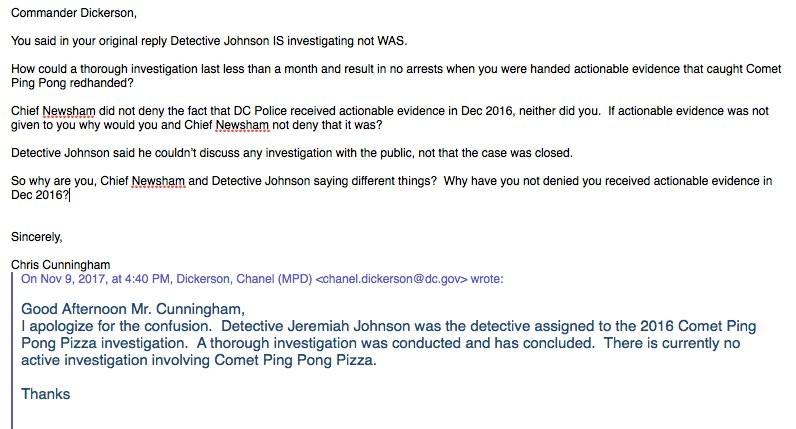
Dickerson, in any case, responds with “Detective Jeremiah Johnson is assigned to this case. I will ensure that he gets the video link you provided.”
Cunningham then sends his questions to Johnson, a Detective in the FBI Child Exploitation Task Force, and, on Nov. 9, gets the deflecting answer “I am not at liberty to discuss any investigation with the public.” He’s refers Cunningham to the public information office. Instead, Chris asks Dickerson for clarification and gets the response, “I apologize for the confusion. Detective Johnson was the detective assigned to the 2016 Comet Ping Pong investigation. A thorough investigation was conducted, and has concluded. There is currently no active investigation involving Comet Ping Pong pizza.”
Every step of the discussion is tweeted, and other Pizzagaters get involved. Mellisa Zaccaria (previously featured in my story at https://justpaste.it/PizzaZaccaria) reveals that her “media contact” has gotten someone at DCMPD to say “Detective Johnson is looking into the information that was received by Mr. Cunningham.” This apparently simply means the YouTube link Cunningham sent in is not being ignored. Pizzagaters embrace the response as an indication the Comet case is still open at the FBI. One inquirer, Brian Richmond (@B_Rich33NO) shows that he got a letter in response to a Freedom of Information Act request in May, 2017, saying that “The Metropolitan Police Department did not conduct an investigation regarding alleged pedophile ring at the Comet Ping Pong Restaurant.” This seems to flatly contradict Dickerson’s statement that a thorough investigation was done, but has been concluded. Confusion continues in the Nov. 13 YouTube, mentioned above, in which BigFish telephones Dickerson’s colleague Daniel Godin, and reveals the officer giving a baffled response. The hesitant officer encourages BigFish to re-send any evidence he possesses about the location of child pornography, and sticks to this advice even after being told that his colleague Marcus Stevens has already had possession of every bit of the evidence for a year.
Sometime in late November, Cunningham decides to travel the 2 ½ hours to DC to straighten things out in person. His reports about his meetings emerge over subsequent days. On Dec. 1, referring to the exchange that stimulated his travel, he tweets “I called Detective Stevens and asked, ‘Do you have any evidence against Comet?’ and he said, ‘What evidence, there’s no evidence.’” After being reminded of his year-old history of emails with BigFish, Stevens tells Cunningham to call the FBI. Cunningham tweets, “and then I went to the D.C. Police and questioned Daniel Godin and Sarah Hoffman” (both members of the Youth and Family Services Division).
Some of the other tweets he’s emitted about his meetings include:
<blockquote>
Chris Cunningham @Cunningham623 Dec. 5, 2017
Next day I went and saw Sarah Hoffman who assured me Jeremiah Johnson who she knew personally as a(n) honest man was investigating along with the FBI and that the media had been told to conceal the investigation so the public wouldn't interfere, which is the biggest load of BS ever.
Chris Cunningham @Cunningham623 Dec 3
… I spoke with Detective Sarah Hoffman and she assured me the FBI was and has been investigating, they told "Big Fish" the same thing. I called Marcus Stevens and confirmed he received actionable evidence.
Chris Cunningham @Cunningham623 Nov 27
They don't respond to my emails and I couldn't record the convo with Detective Sarah Hoffman. She told me they were investigating, I'm not lying, they won't respond to my confirming E-mails. I'll go down and get video of them saying that soon.
Chris Cunningham @Cunningham623 Nov 27
Yea after that E-mail they never responded so I went down to the D.C. Police station and Sarah Hoffman assured me the F.B.I. specifically Jeremiah Johnson is investigating.
Chris Cunningham @Cunningham623, Nov 27
Who's been to the DC police station?!? Me or You? Detective Sarah Hoffman assured me the F.B.I. is currently in the midst of a massive investigation. So ... did the DC police lie to my face?
Chris Cunningham @Cunningham623, Nov 29
Oh and here's the cop's business cards to prove I actually went and talked to them. And they are complicit in a child pornographers cover up whether you wanna believe that or not, it's the truth, unlike y'all I really don't make assumptions, I have things proven to me.
</blockquote>
Including ‘vril lizards,’ one deduces.
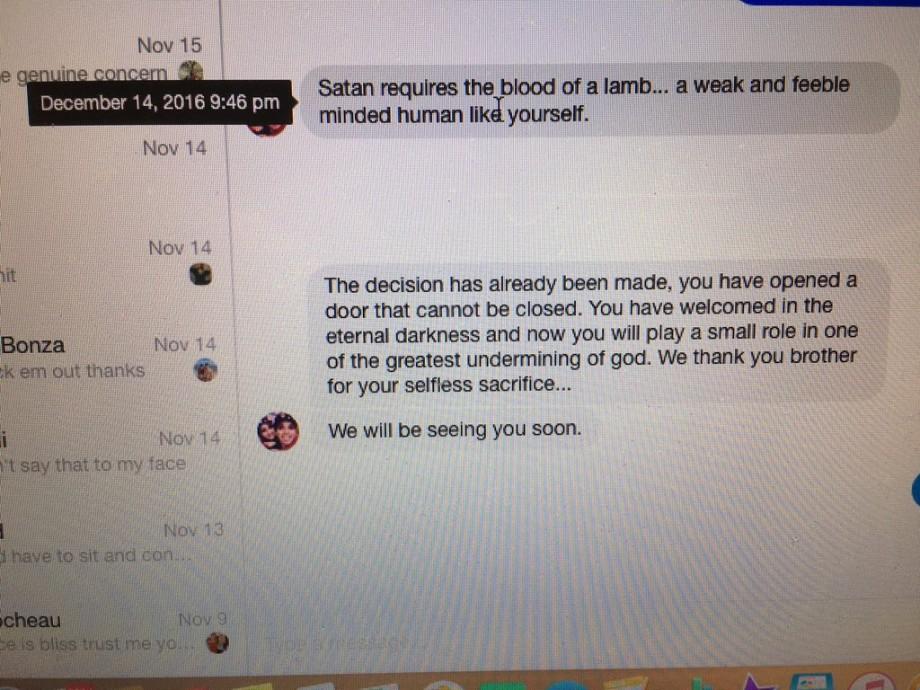
He consistently insists both that he’s talked to police who assure him that an investigation is going on, and that the police are engaged in a child pornography cover-up. At one point, to press his case with Officer Hoffman, he apparently shows her some threatening messages he received from a person claiming to be an Illuminati Satanist who had taken an interest in him. (He had earlier tried to confront Arrington de Dionyso, an artist who’d received grief from Pizzagaters for painting a long-gone mural on a Comet Ping Pong wall – https://medium.com/@arringtond/how-i-became-a-target-of-the-alt-right-66f14eceaffe, – with a YouTube showing a girl who claimed to have been subjected to Satanic ritual abuse. Arrington’s friends had decided to respond to this belated harassment by mockingly throwing the fear of Satan into the credulous young man with statements like “Greetings from the Pizzagate brotherhood. James Alefantis thanks you for spreading the word about our wonderful organization …Satan requires the blood of a lamb … a weak and feeble human like yourself … You have welcomed in the eternal darkness … We thank you brother for your selfless sacrifice… We will be seeing you soon.”)
Cunningham vividly documents the police officer’s response to the scary messages, as well as his own interpretation of that response.
<blockquote>
Chris Cunningham @Cunningham623
Haha retard admitted to it (Arrington’s mischievous friend ‘admitted’ to being an agent of the Illuminati – BN) and Detective Sarah Hoffman's response was, "oh, do you believe the Holocaust wasn't real? I mean, if you believe in the Illuminati you could believe in anything." She is complicit in a child porn cover up, they refused polygraph tests!! "Big Fish" would take one!
</blockquote>
There’s no way the DC Police are going to escape being implicated in Satanic machinations now.
It’s not clear whether the DC Police, accustomed as they may be to handling the public with utmost seriousness, feel compelled to give this unusual young man the most carefully researched answer they can. To what extent any of his statements can be taken literally, even when they are accurate records of what he heard, is surely moot.
In any case, Cunningham’s interventions, along with BigFish and Fougere’s technical obfuscations, are the main factors that are now keeping the Comet child pornography allegations afloat on the internet.
The scandal never had much of a toehold in credibility in the first place. The only factor even suggesting that there MIGHT be child pornography associated with Comet was the pre-election blitzkrieg of speculation about Tony Podesta’s art, the food references in John Podesta’s emails, and the ironic wit attached to the god-daughter photos on James Alefantis’s Instagram. That plus the intense desire to associate pedophilically motivated murder with any and all Democrats, especially Hillary Clinton. This welter of mischief is probably the main factor that made some large file-size numbers turn into dancing naked children before BigFish’s imaginative eyes.
Right now, this fantasy is getting very old. The efforts to maintain Pizzagate, in general, are becoming ever more garish, despite some coincidental power-abuse scandals from Hollywood.
There is, however, one piece of interesting evidence in the Comet child porn scandal that has been noticed, but not yet linked to other, similar evidence. The ‘hacker’ who made the screenshot of the alleged Comet Upload/Download page was using a browser that had, in its standard search blank in the upper right, the German word ‘Suchen,’ for ‘search.’ It’s unlikely this person with a German browser was a Big Fish named Miner from Pasco, WA. I had noticed previously that a large proportion of Pizzagaters’ screenshots of James Alefantis’s Instagram posts, snapped in a hurry in early Nov. 2016 before the account was set to private, were made by people whose browsers indicated German geolocation. Although the latter findings of German text could possibly be explained by use of Tor proxy servers situated in Germany, if that were so, there should also have been some shots showing other common Tor server languages like Romanian and Hebrew. Not so. The shots were all in German or English.
I am left wondering why so much of the imagery made as part of an American political campaign was fueled by apparently German sources. A Russian espionage outpost somewhere in Deutschland, perhaps?
If not, it’s time for a new conspiracy theory.
-- 30 --
(number is not a conspiracy symbol)