De-anonymization of LockBitSupp: Evgeny Dementyev as a potential leader of the group
UPDATE as of 15.02.2026.
I have added updated data to the timeline table — the exact timestamps of all messages (not rounded to 00:00), included an additional source — LockBitSupp’s posts from the ReHab forum, and added references to the sources. I also updated the screenshots accordingly to match the new data.
In addition, I added an analytical section and a description of the conclusions. The result has become even more precise.
In July 2025, my research focus shifted to the LockBit ransomware group, specifically its leader LockBitSupp, who has been publicly identified by the FBI as Dmitry Khoroshev. However, my analysis indicates that he is not the actual leader of the group.
Initial Lead
Dmitry Khoroshev was associated with a Mercedes GLE, license plate о517ет136, VIN: WDC2923241A144235
This vehicle is officially not registered to Khoroshev, but to the company LLC “NPG” (INN 9717048612).
The CEO and owner of this company is Evgeny Petrovich Dementyev (born 21.07.1987).
Factors Worth Noting
-
In 2018–2019, Dementyev took out a credit of approximately 1 million rubles (~$10.000).
-
After 2020, a sharp increase in expenses was observed, including numerous high-value purchases at TSUM (see attached materials).
-
The company has an annual revenue just under 1 billion rubles (~$10 million USD).
-
Lifestyle: private, minimal public activity.
-
Does not leave the territory of the Russian Federation.
Second Vehicle
Dementyev also uses a BMW X6 XDRIVE40I, 2020, license plate K102CX799, which is also registered to LLC NPG.


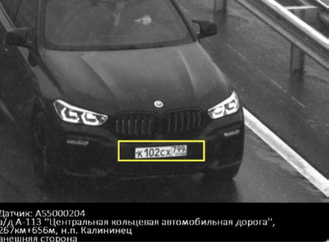
Data Collected
I gathered all available traffic fines associated with this vehicle and all public messages of LockBitSupp, and analyzed them chronologically.
Sources:
-
Traffic fines of Dementyev’s BMW K102CX799 — publicly available through services like Autocode (extended report https://avtocod.ru ), AvInfo (extended report), etc. (or https://probiv[.]space/).
-
Public posts of LockBitSupp on the XSS forum ( https://xss[.]pro accounts: LockBitSupp and LockBit)
- Public posts of LockBitSupp on the ReHub forum (http://rehubg7wpn5vuwttbzqrzm5epq6ta5mqm6cbfpn7wtukaskzte3ehcyd[.]onion account: LockBit)
-
Messages from LockBitSupp’s Tox messenger (published in an interview by Tor Zirael – file petuh.txt)
-
Public posts of Telegram account Fox William Mulder, ID 7262708360 (official LockBitSupp account, now deleted)
All files are attached to the article.
Timeline Analysis
The overall graphical timeline looks as follows:
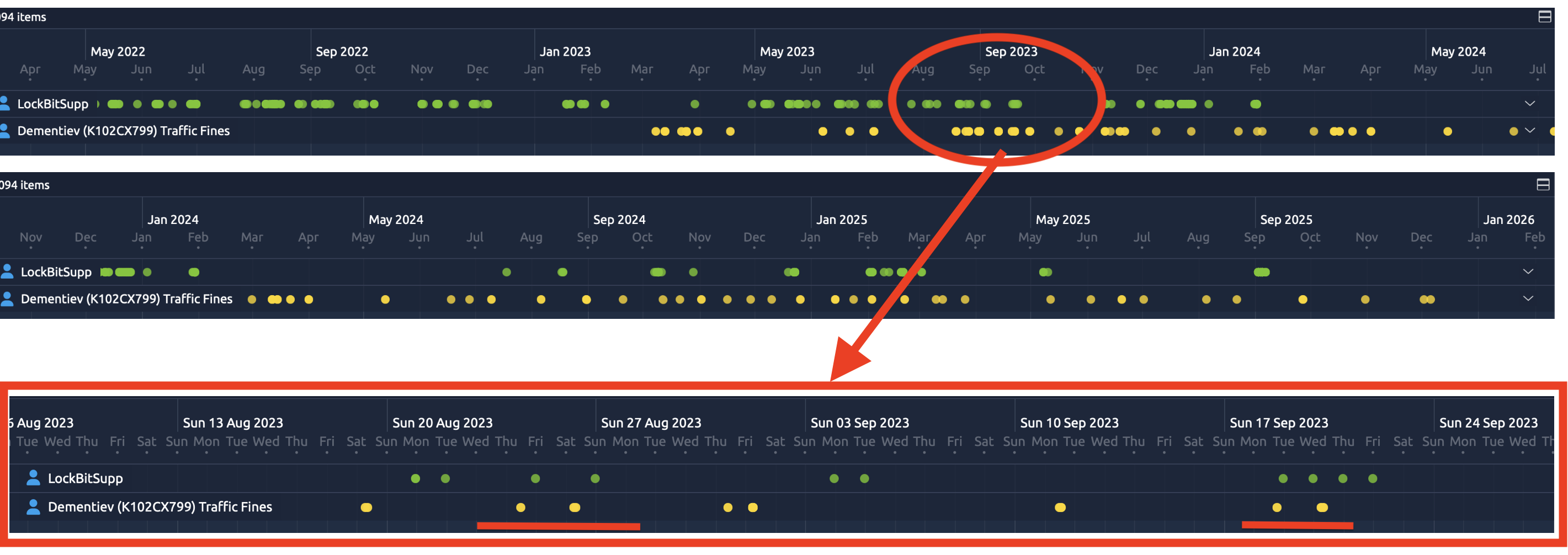
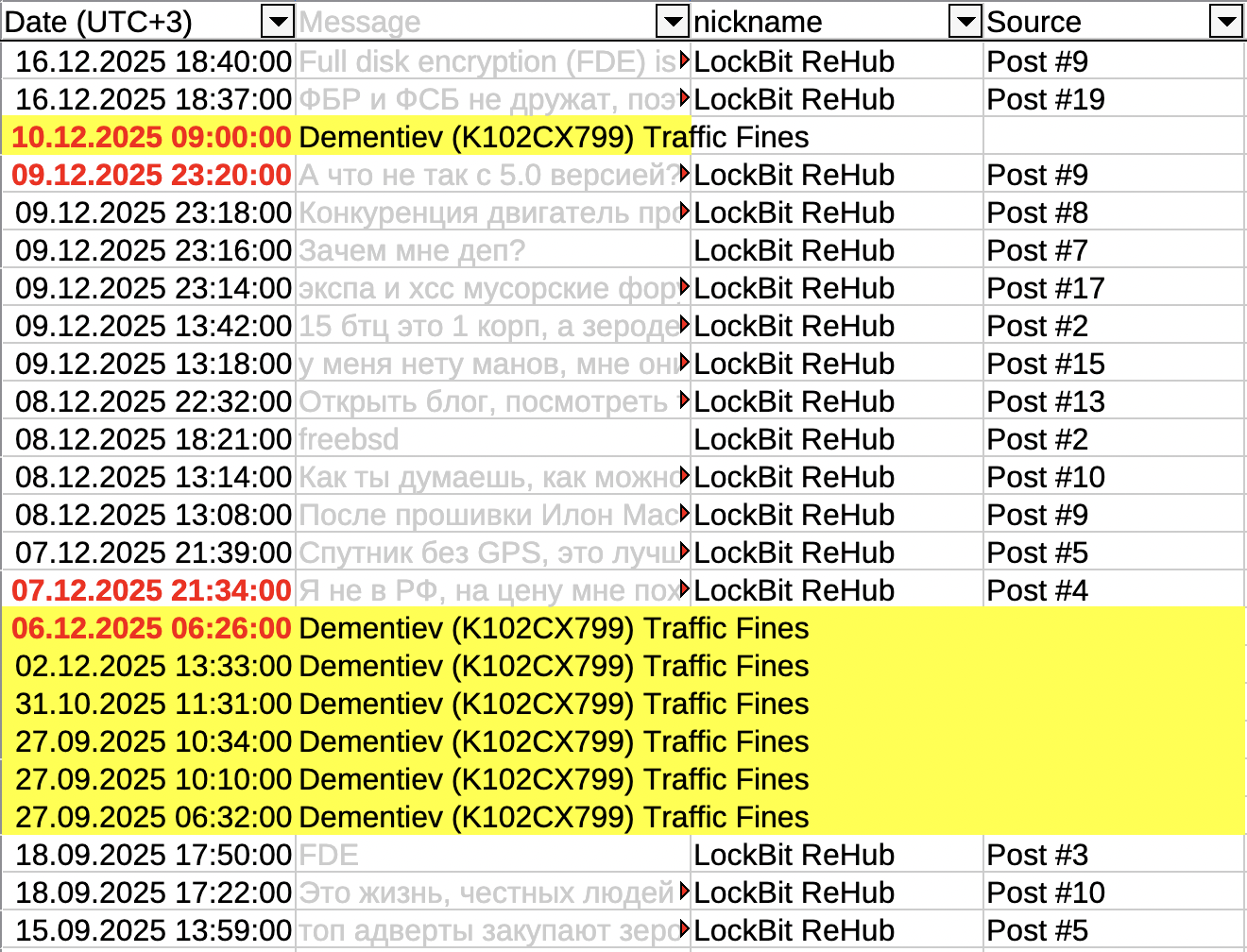
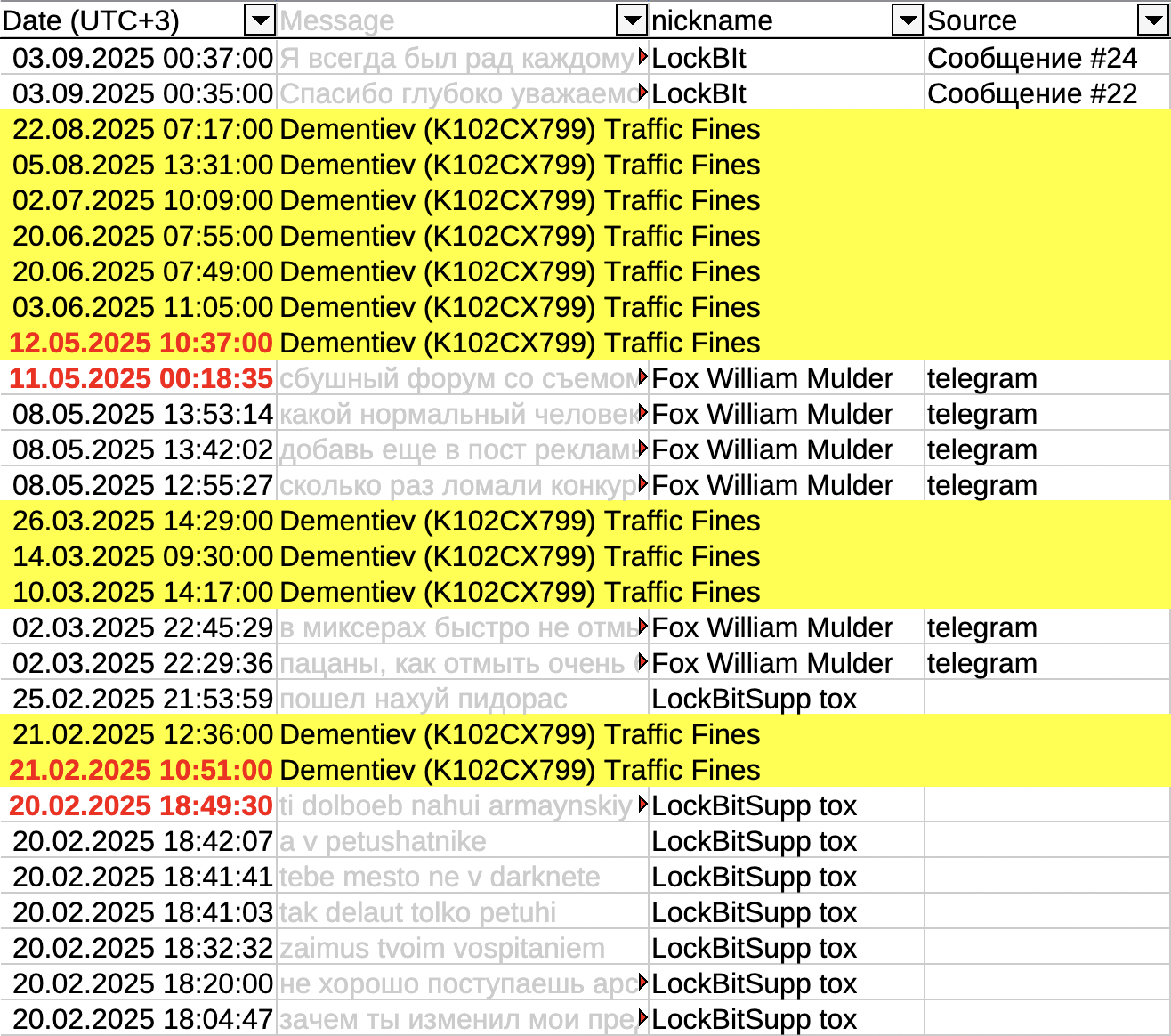
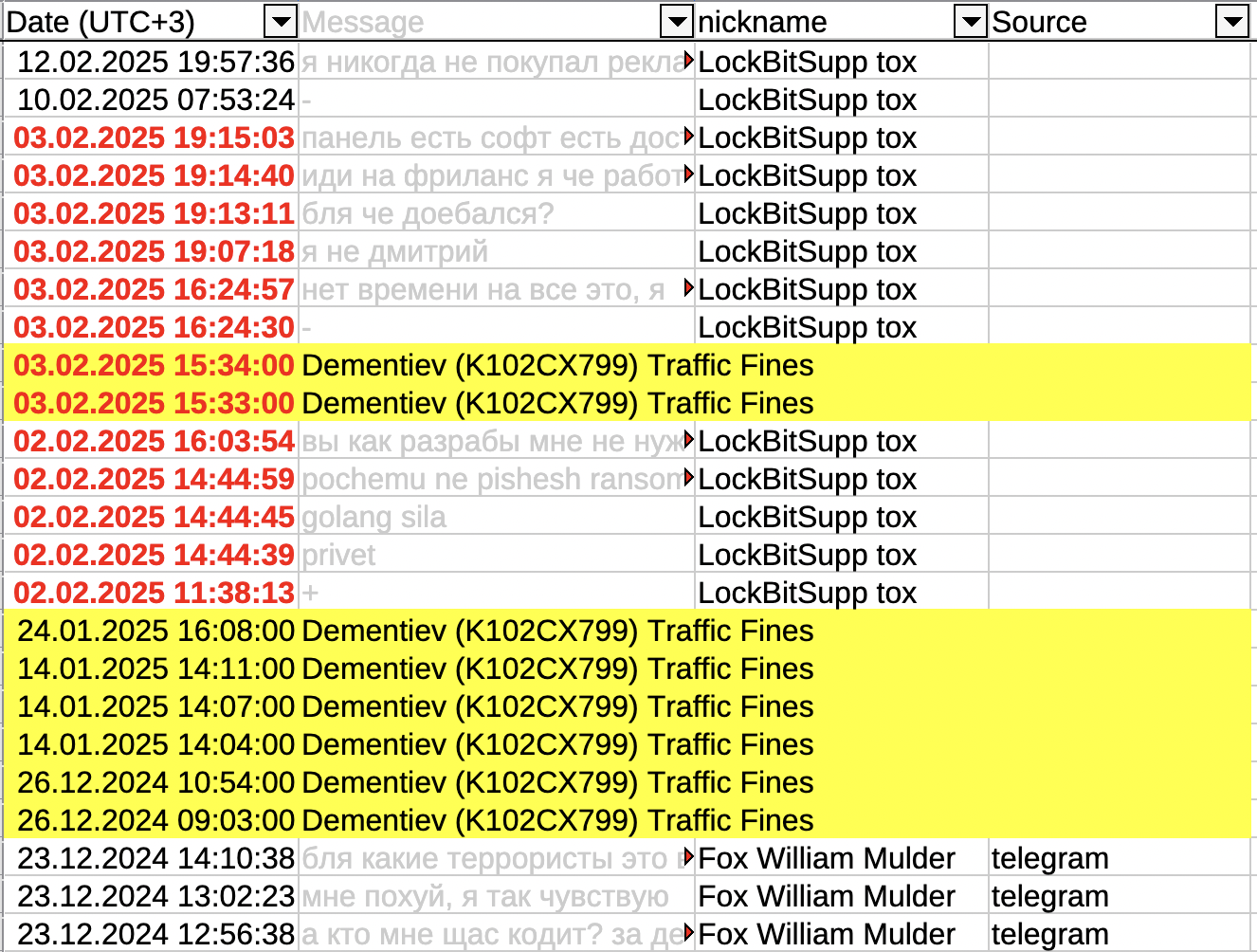
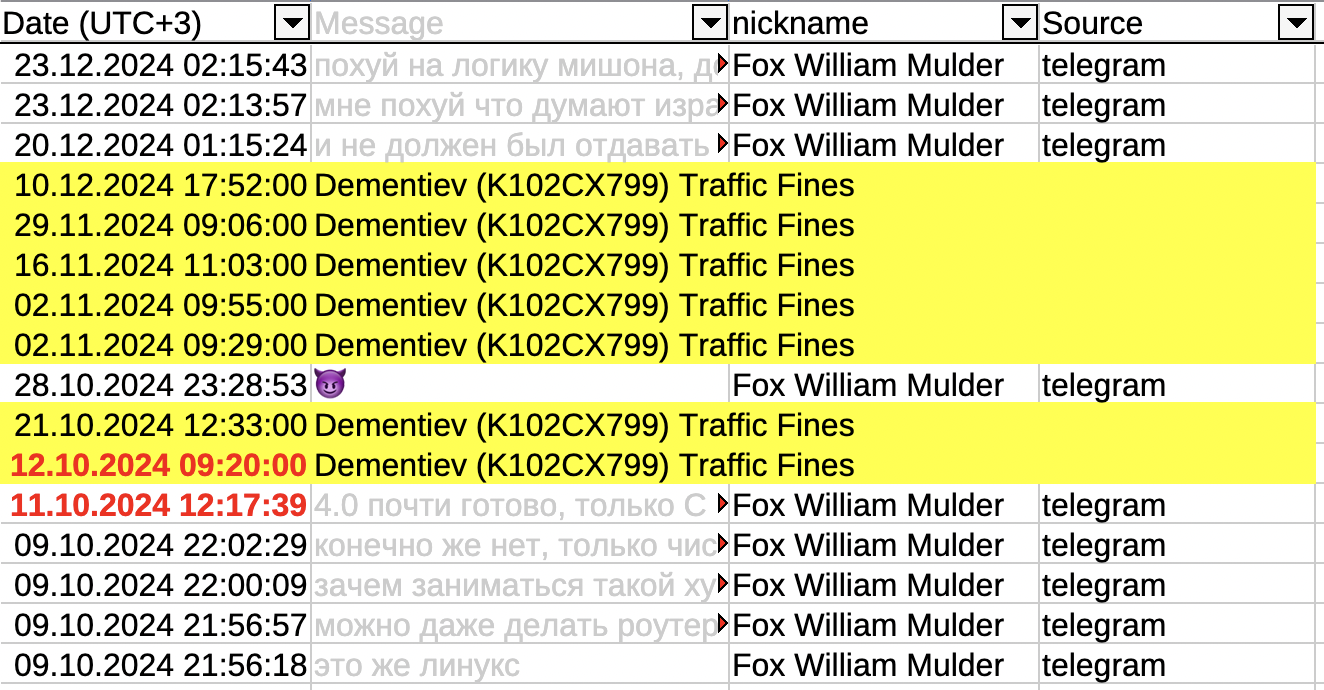
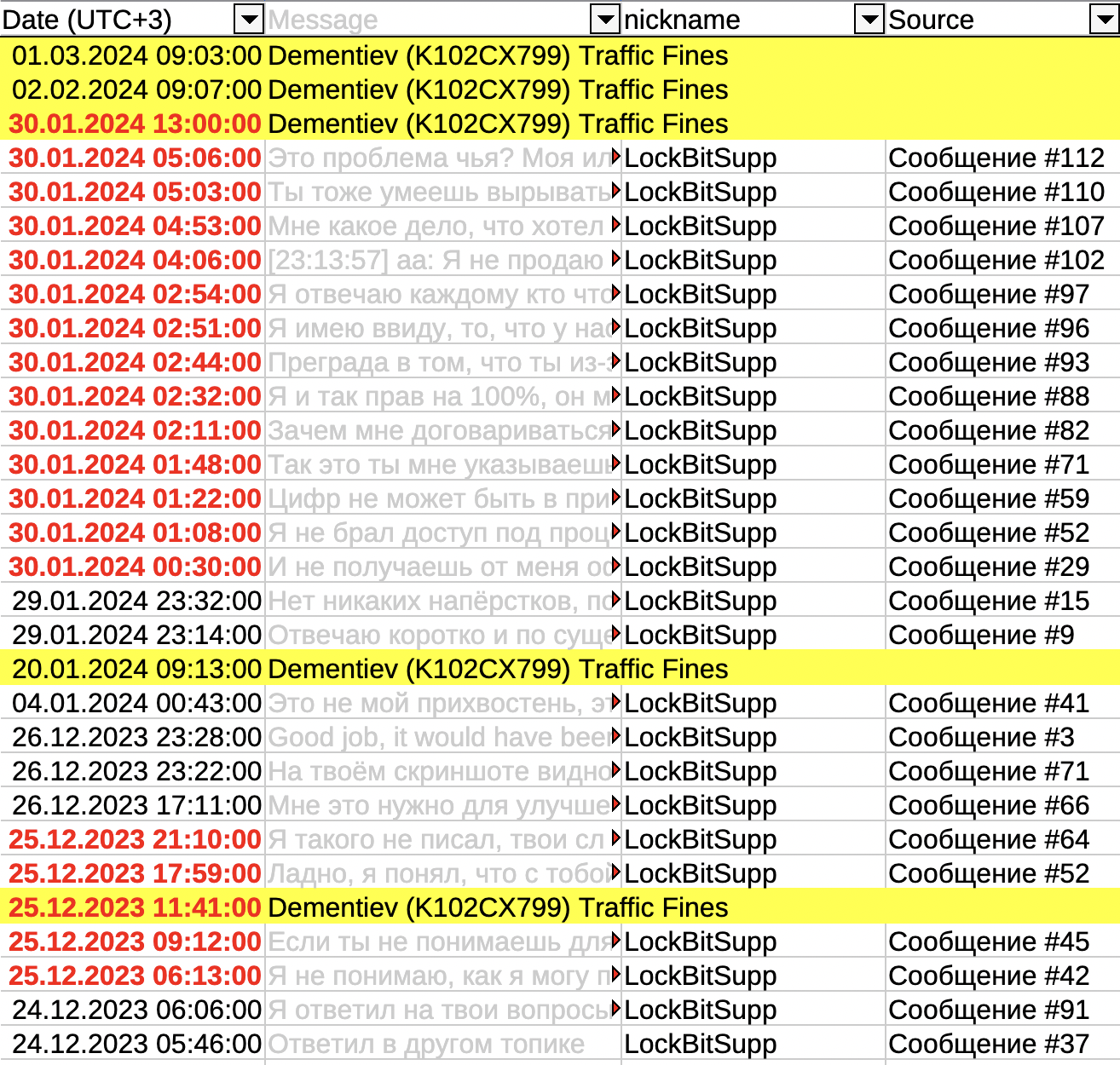
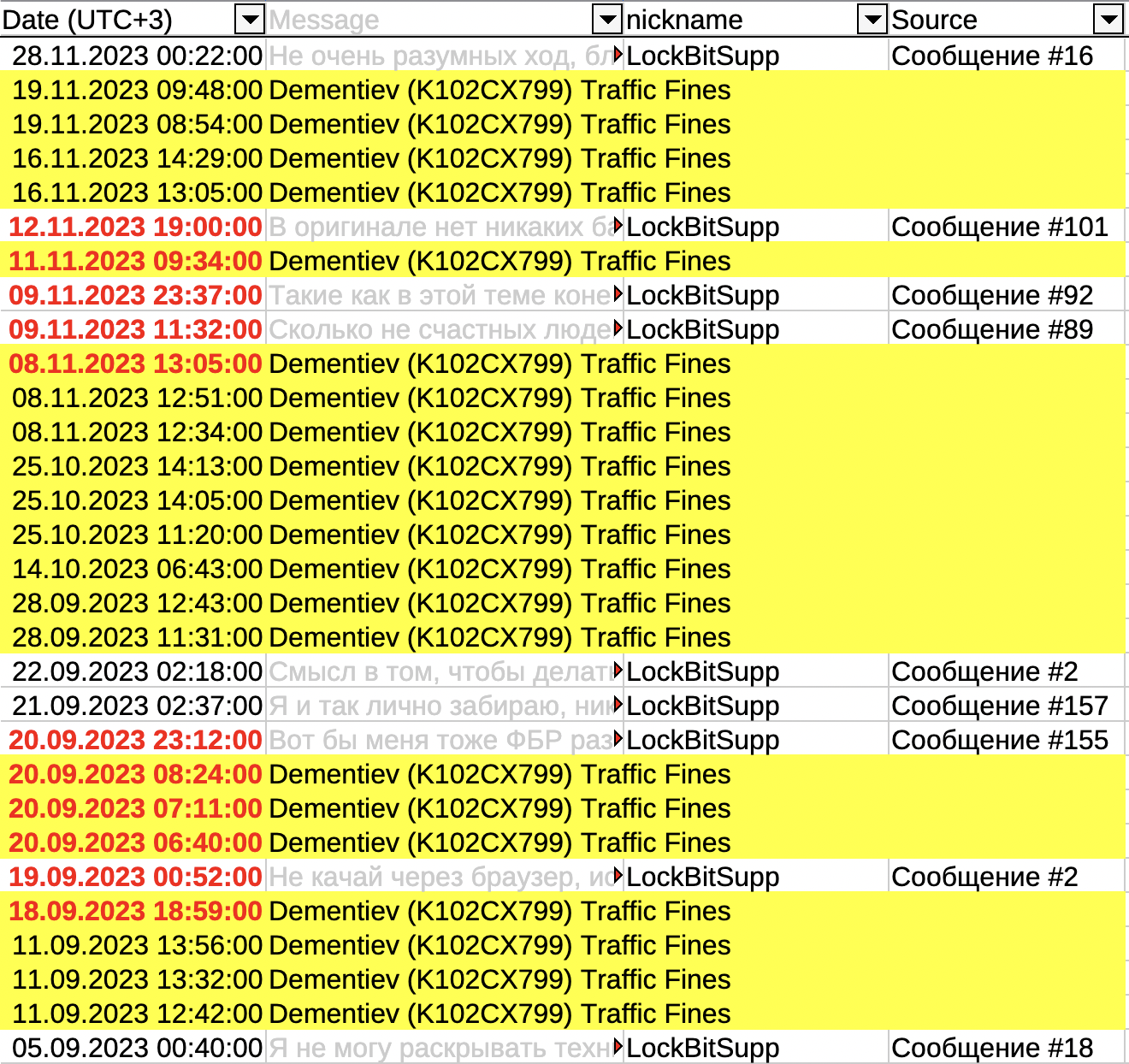
I consolidated all this data into a single timeline table 👉 Download, with traffic fines highlighted in yellow for clarity.
The observed pattern allows a high-confidence link between Evgeny Dementyev and the LockBitSupp account.
Examples
Screenshots highlight key points in red. The content of messages is irrelevant — only the dates and metadata were analyzed.
Note: You can collect more precise data and replicate the analysis independently — all sources are open, links provided.
This discovery is the result of several days (and even weeks) of meticulous work.
I plan to describe the methodology in a separate article or an interview.
