Defeating protection of RepetierServer PRO features
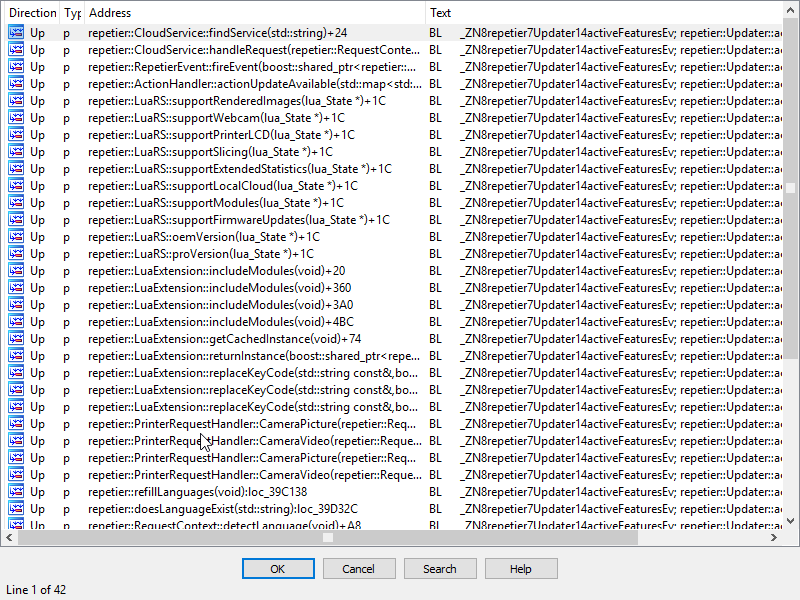
RepetierServer is a C++ app and every binary of any processor architecture can be dissambled in a static manner. So it wont be needed a hard setup of devices and debuggers. Just some good dissabler like IDA is fine to go. Luckily some literal strings about license refers to network methods that can be followed (fe: repetier::MainRequestHandler::noLicenseError) trought references we can find a common call to method
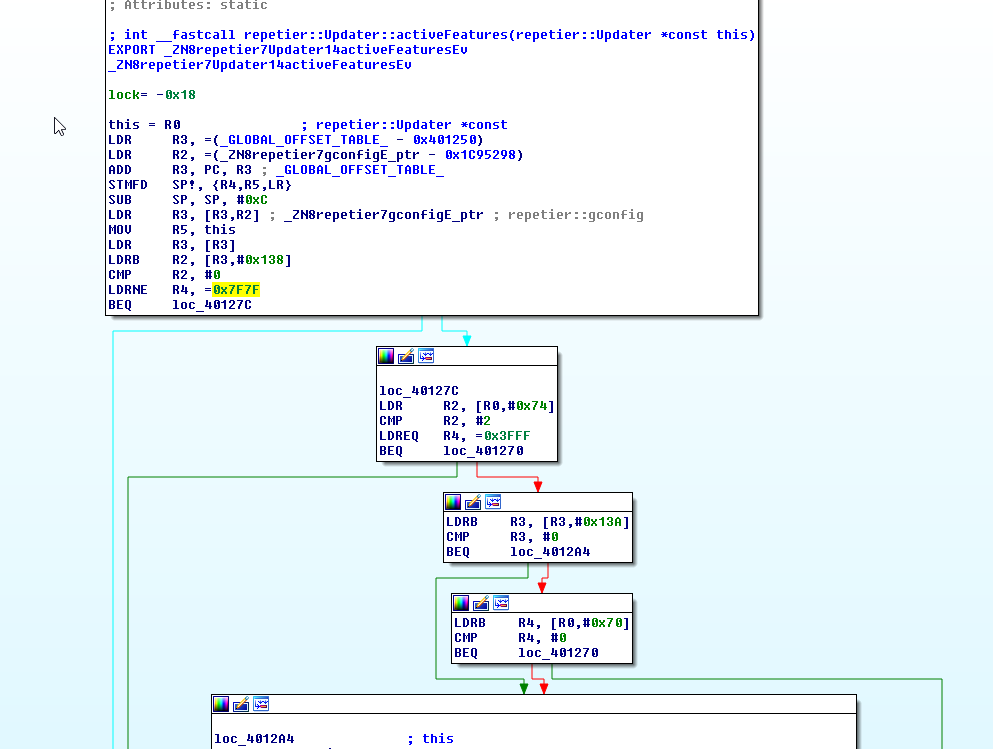
repetier::Updater::activeFeatures
this method tell the software what features are enabled or not. to do so, it returns a number meaning the privilege of execution. At this point seems 0x7f7f is the key value to return to get all features enabled.
This is normal follow of method
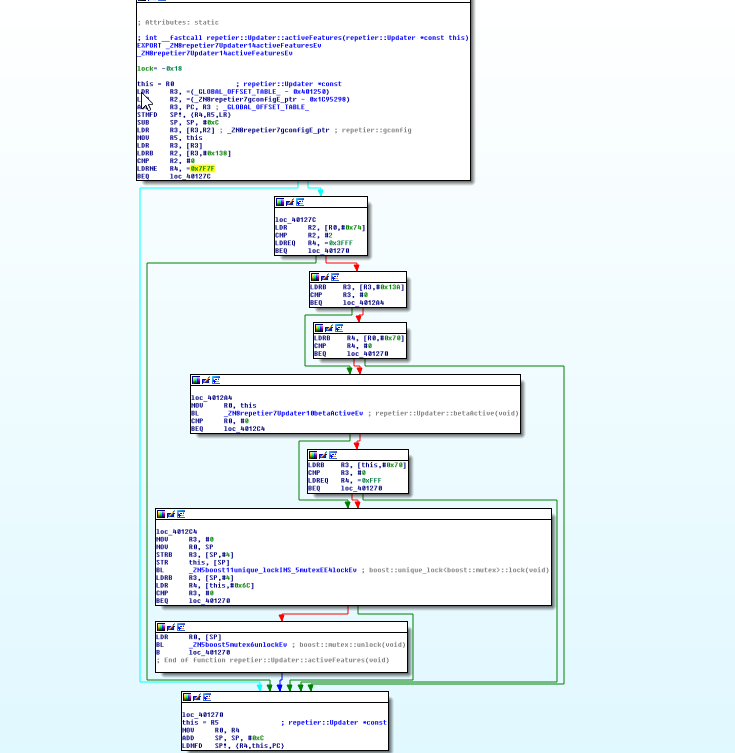
It just check stuff to make up a number with your privilege level. As we want to make it simply return 0x7f7f we can do some byte patching.
Those opcodes means some numbers on ARM architecture (in this case) so we can just insert few nop opcodes instead original ones to disable some functions.
On arm all opcodes contain 4 bytes a nop for example will be 00 F0 20 E3 this opcode will make nothing for 1uS so after a bit of cleaning should have something like this
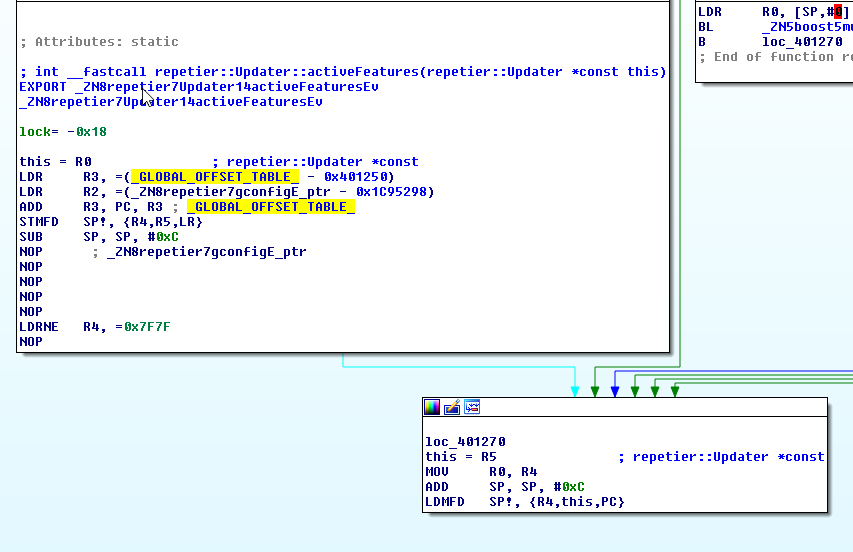
This is clearly ripping off some code outside the bounds of function but that wont affect the working of the method if its not too badly done.
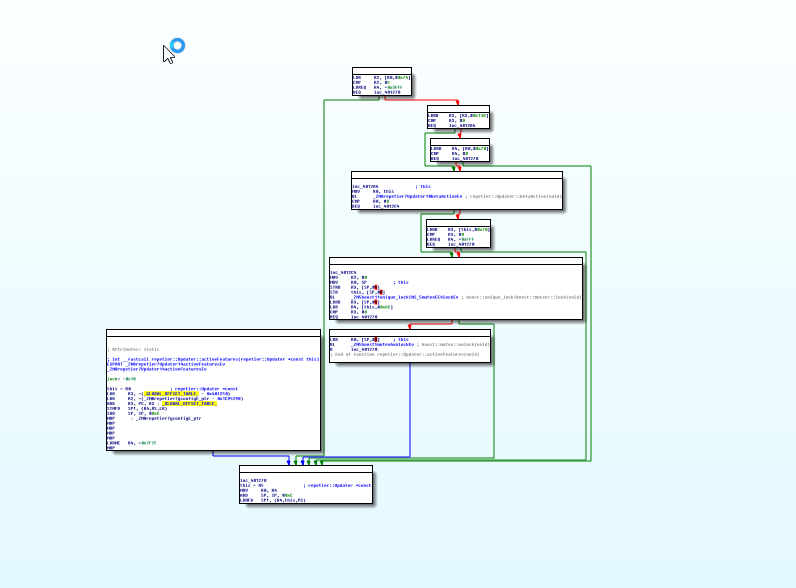
This function returning this exact value gives plenty of PRO features and its systematically been called by all method that need pro level
So being this patch applied PRO features get enabled, but account stuff remains as unregistered.
ARMhf ARMv7 32bit 0.80.3 build
Address: 0x391B06
Change from: [ 47 F6 7F 74 93 F8 38 21 12 B1 ]
To: [ 43 F6 FF 74 C0 46 C0 46 C0 46 ]
ARMabi ARM RPi 0.80.3 build
Address: 0x3F9254
Change from: [ 02 30 93 E7 00 50 A0 E1 00 30 93 E5 38 21 D3 E5 00 00 52 E3 8C 40 9F 15 02 00 00 0A ]
To: [ 00 F0 20 E3 00 F0 20 E3 00 F0 20 E3 00 F0 20 E3 00 F0 20 E3 8C 40 9F 15 00 F0 20 E3 ]
Hope it clarify it a little. regards Pabloko, amsspecialist.com
